Thousands of Mega logins dumped online, exposing user files

(Image: ZDNet)
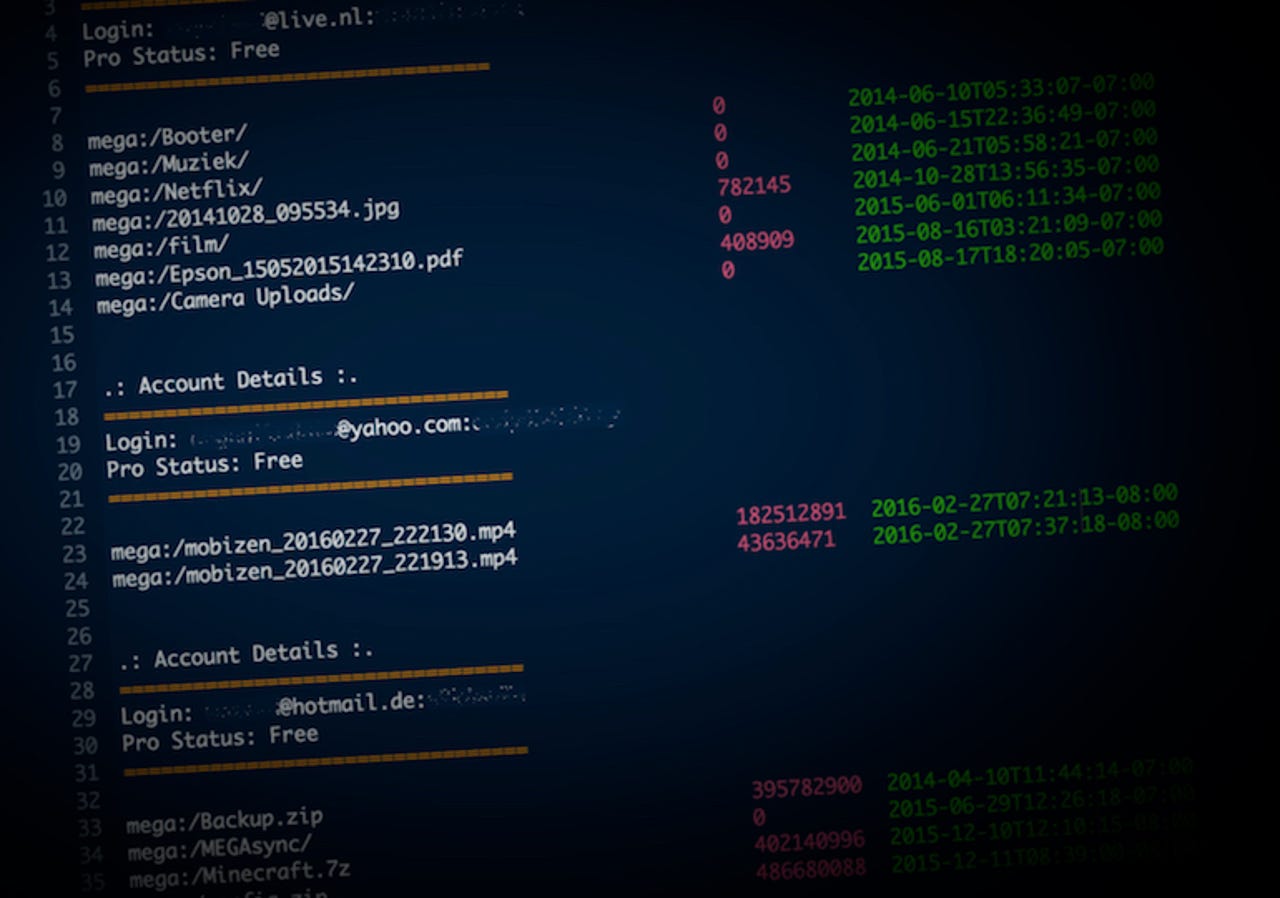
Thousands of credentials for accounts associated with New Zealand-based file storage service Mega have been published online, ZDNet has learned.
The text file contains over 15,500 usernames, passwords, and files names, indicating that each account had been improperly accessed and file names scraped.
Patrick Wardle, chief research officer and co-founder at Digita Security, found the text file in June after it had been uploaded to malware analysis site VirusTotal some months earlier by a user purportedly in Vietnam.
Wardle passed the data to ZDNet.
We verified that the data belonged to Mega, the file-sharing site formerly owned by internet entrepreneur Kim Dotcom by contacting several users, who confirmed that the email address, password, and some of the files we showed them were used on Mega. (You can read more here about how we verify data breaches.)
The listings date back to the cloud service's debut in 2013, and as recently as January.
We sent the data to Troy Hunt, who runs data breach notification site Have I Been Pwned, to analyze. His analysis pointed to credential stuffing -- where usernames and passwords are stolen from other sites and ran against other sites -- rather than a direct breach of Mega's systems. He said that 98 percent of the email addresses in the file had already been in a previous breach collected in his database.
Some 87 percent of the accounts in the Mega file were found in a massive collection of 2,844 data breaches that he uploaded to the service in February, said Hunt.
Of those we contacted, five said that they had used the same password on different sites.
When reached, Mega chairman Stephen Hall also said the exposed credentials pointed to credential stuffing, and not a breach.
He said in an email that the list is "only 0.0001 percent of our 115 million registered users."
It's not known who compiled the list or how the data was scraped. Although the site claims to offer end-to-end encryption so that even the company can't see what is uploaded, the site doesn't allow for two-factor authentication -- making it far easier to break into accounts when a user's account password leaks. An attacker would only need to use the credentials to log in to each account to confirm they work, and to scrap the file names.
Hall said the company plans to introduce two-factor authentication "soon," but did not say when.
Mega keeps a record of the IP address of each user who logs in to an account. Three users said they saw suspicious logins accessing their account from countries in Eastern Europe, Russia, and South America in the past few months since the credentials file was uploaded.
One of the accounts in the file contained file listings for what appeared to describe child abuse content. Given the nature of the account's content, ZDNet informed the authorities.
In a reply to our email, Hall said it was "unclear" if the child abuse content was uploaded by the original account owner or if it was uploaded by someone else using the account as an anonymous drop box.
But the illegal content was uploaded years earlier, according to upload dates on the file listing, making any recent third-party involvement unlikely.
"Mega has zero tolerance for child sexual abuse materials," said Hall. "Any reports result in links being deactivated immediately, the user's account closed and the details provided to the authorities."
"Mega can't act as censor by examining content as it is encrypted at the user's device before being transferred to Mega," he said. "As well as it being technically impossible, it is also practically infeasible for Mega and other major cloud storage providers, with 100s of files being uploaded each second."
It's not the first time Mega has faced security issues. In 2016, hackers claimed to obtain internal Mega documents. Hall said at the time that no user data was compromised.