Uber 'shared trip' data leaked into Google search results

Dozens of trips taken using private car service Uber have been cached by Google, making them available to anyone with a simple search term.
By site-searching "trip.uber.com" in Google, a list of past trips appear in the search results.
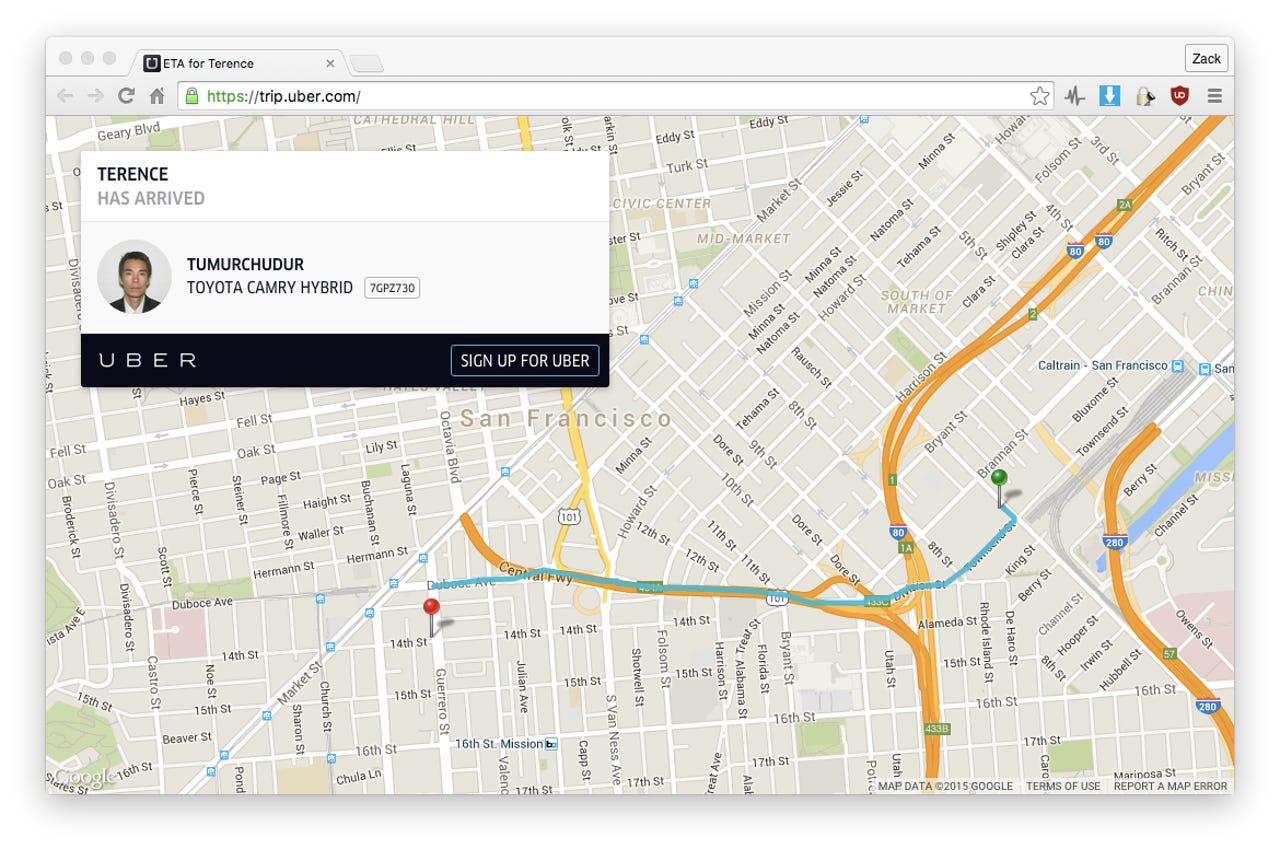
These trips are shared by the user from the mobile app, allowing others to track their current location, and other information associated with the ride -- including the driver's name, and car registration -- from a single link. Many tweet their location and estimate arrival times. After a hiatus, Google recently started picking up tweets again in search results.
Some of these trips date back as far as 2013, and include trips from the US, UK, Russia, Indonesia, India, and the Philippines -- data and information that remains online and accessible even today.
Uber gives out very little visible information from each ride on the "shared trip" page, except for a map with the arrival and destination entered by the user on the Uber app, route and also the first name of the driver and passenger.
But hidden in the page's code is often exact address data -- which can be a home, or work address, or a public location, like a railway station, airport, or hospital. The code also includes exact dates and times that trips were made.
By cross-referencing the search results with other public information, such as social media accounts, it took just a few minutes to get one Uber passenger's full name, job description, and other sensitive personal information -- including a reasonable guess why that person took the trip in the first place.
Whoever this man whom I had never met was, suddenly I knew a lot about him.
"Personally, I'm not that concerned about it, but I may be a bit out of the norm. I hyper share my location publicly. I also publicly tweeted my trip, so I fully expect that people would be able to see it," said the person, who we are choosing not to identify.
I gave him the rundown of what I thought he was doing, based on the route locations, time of day, and other information I could gather from his Twitter account. I knew when, where, and how, but I didn't know why he had taken that Uber that day.
He gave his side of the story. In his words, "you got fairly close."
"Again, we are very public people, so this isn't a huge deal to me... but I can totally see why other people may be concerned," he added.
"I think being able to personally access all of your trip history via the app or Uber.com is great (which you can do). But I don't really think keeping these trips publicly accessible in the long term serves much of a purpose," he said.
Internet of Things
Joe Sullivan, Uber chief information security officer, said in a tweet to Mikko Hypponen, F-Secure chief research officer, that the car service company was "looking into this."
It's not thought a specific security flaw is to blame. Sullivan followed up, explaining that: "We found that all of these links are deliberately shared by users. Our user data is critical; will look for ways to further improve."
Sensitive information, such as credit card data, usernames and passwords were not revealed. All of the data on the Uber share page is metadata, which can tell another person "where" and "when," but not necessarily "why."
In some of the trips seen in the Google search results, it can be reasonably assumed some people are leaving work to go to the airport, or in some cases -- based on cross-referencing a time late in the evening with a cross-references location of a popular bar -- that some users are getting an Uber home when they've had a few to drink. In other cases, people are leaving hospitals or schools at a certain time of day or night. Do people work there, or are they there for another reason? Do they really want the answers to these questions to be searchable?
Uber spokesperson Molly Spaeth said in an email: "This is not a data leak. We have found that all these links have been deliberately shared publicly by riders. Protection of user data is critically important to us and we are always looking for ways to make it even more secure."