500,000 stolen email passwords discovered in Waledac's cache
"More specifically, they have 123,920 login credentials to FTP servers at their disposal. This number is significant, considering the Waledac controllers use an automated program to login to these servers and patch (or upload) specific files to redirect users to sites that serve malware or promote cheap pharmaceuticals.
We also discovered 489,528 credentials for POP3 email accounts. These credentials are known to be used for “high-quality” spam campaigns."
Abuse scenarios
- Stolen email accounts can be used for email impersonation attacks abusing the trust chain between the owner and a countless number of services and contacts related to him. Once the trust chain has been abused, the malicious attackers can also easily embed the accounting data into their spam platforms, in an attempt to take advantage of the DomainKeys ecosystem and increase the probability of reaching the user's Inbox.
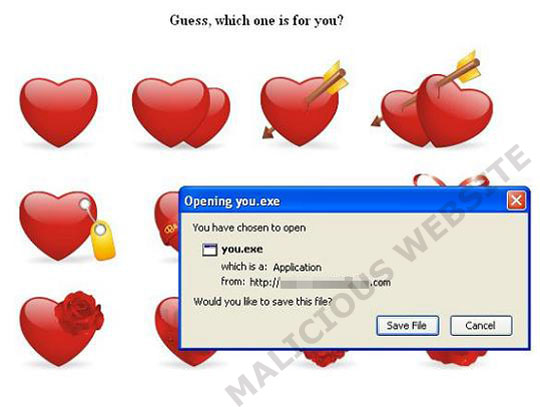
- The stolen FTP accounts are usually embedded in efficiency-driven blackhat SEO (black hat search engine optimization) tools, and managed spam/exploits-serving services, allowing the malicious attackers to easily tailor their campaigns, be it pharmaceutical scams, pure blackhat SEO campaigns with real-time syndication of trending topics across the Web, and, of course, serving client-side exploits through legitimate web sites.
See also:
- The current state of the crimeware threat - Q&A
- Embedding Malicious IFRAMEs Through Stolen FTP Accounts
- Embedding Malicious IFRAMEs Through Stolen FTP Accounts - Part Two
This is perhaps the perfect moment to change your passwords -- in a perfect world best practices are in place -- from a malware-free host.