A bug in cell phone tracking firm's website leaked millions of Americans' real-time locations

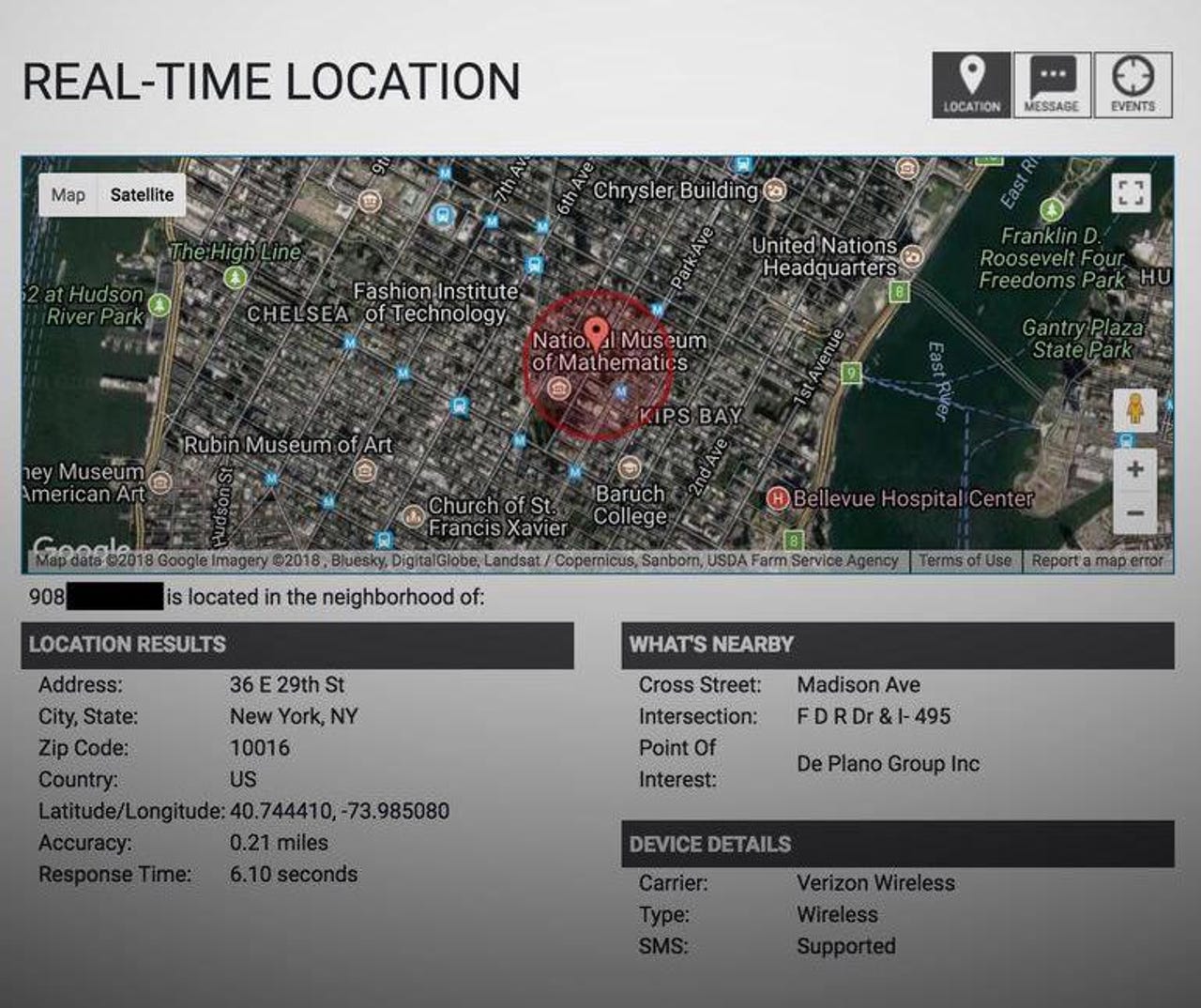
A bug allowed anyone to skip a consent requirement in a cell phone location tracking site. (Image: ZDNet)
A company that collects the real-time location data on millions of cell phone customers across North America had a bug in its website that allowed anyone to see where a person is located -- without obtaining their consent.
Earlier this week, we reported that four of the largest cell giants in the US are selling your real-time location data to a company that you've probably never heard about before.
Read also: Evidence of stingrays found in DC, Homeland Security says
The company, LocationSmart, is a data aggregator and claims to have "direct connections" to cell carriers to obtain locations from nearby cell towers. The site had its own "try-before-you-buy" page that lets you test the accuracy of its data. The page required explicit consent from the user before their location data can be used by sending a one-time text message to the user. When we tried with a colleague, we tracked his phone to a city block of his actual location.
But that website had a bug that allowed anyone to track someone's location silently without their permission.
"Due to a very elementary bug in the website, you can just skip that consent part and go straight to the location," said Robert Xiao, a PhD student at the Human-Computer Interaction Institute at Carnegie Mellon University, in a phone call.
"The implication of this is that LocationSmart never required consent in the first place," he said. "There seems to be no security oversight here."
The "try" website was pulled offline after Xiao privately disclosed the bug to the company, with help from CERT, a public vulnerability database, also at Carnegie Mellon.
In a statement, spokesperson Brenda Schafer said the company has "confirmed that the vulnerability was not exploited prior to May 16, and did not result in any customer information being obtained without their permission," but provided no evidence to support that claim.
Xiao said the bug may have exposed nearly every cell phone customer in the US and Canada, some 200 million customers.
The researcher said he started looking at LocationSmart's website following ZDNet's report this week, which followed a story from The New York Times that revealed how a former police sheriff snooped on phone location data from Securus, a customer of LocationSmart, without a warrant.
The sheriff has pleaded not guilty to charges of unlawful surveillance.
Xiao said one of the APIs used in the "try" page that allowed users to try the location feature out was not validating the consent response properly. Xiao said it was "trivially easy" to skip the part where the API sends the text message to the user to obtain their consent.
"It's a surprisingly simple bug," he said.
Xiao showed ZDNet a video of a script he built exploiting the bug in the company's API.
LocationSmart did not immediately respond to a request for comment.
Xiao verified the bug with a few people he knew. Brian Krebs, who first reported the story earlier today, also verified the bug with several people who allowed him to test the bug.
"None of them got any notification that their location was being tracked," he said.
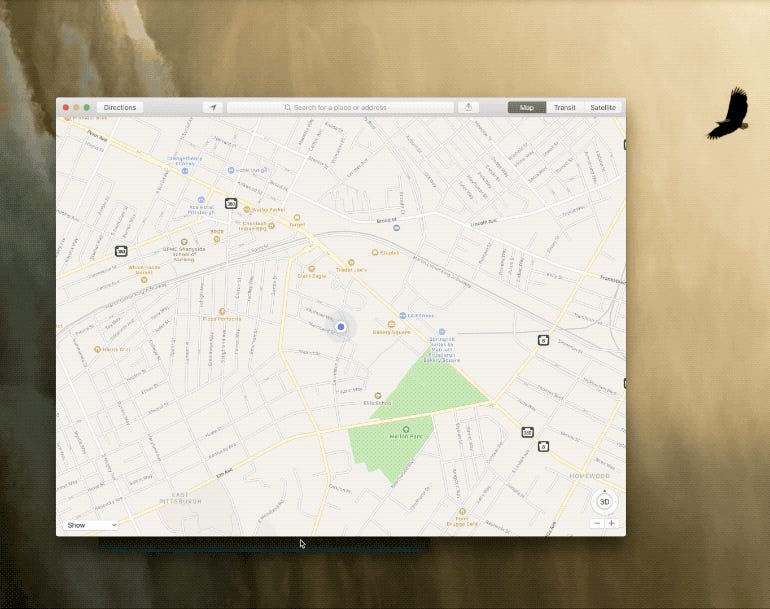
"I had a friend who was driving around Hawaii and [with permission] pinged the location and I could watch the marker move around the island," he said. "It's the kind of thing that sends chills down your spine."
Read also: Stingray spying: 5G will protect you against surveillance
Sen. Ron Wyden (D-OR), who last week called on the cell carriers to stop sharing data with third parties, offered a statement.
"This leak, coming only days after the lax security at Securus was exposed, demonstrates how little companies throughout the wireless ecosystem value Americans' security," said Wyden.
"It represents a clear and present danger, not just to privacy but to the financial and personal security of every American family. Because they value profits above the privacy and safety of the Americans whose locations they traffic in, the wireless carriers and LocationSmart appear to have allowed nearly any hacker with a basic knowledge of websites to track the location of any American with a cell phone," he said.
Wyden said the dangers from LocationSmart and other companies "are limitless."
"If the FCC refuses to act after this revelation then future crimes against Americans will be the commissioners' heads," he said.
We reached out to the cell providers -- AT&T, Verizon, and Sprint -- which all said they were investigating. T-Mobile did not respond to a request for comment.
But this newly disclosed bug shows the carriers are yet to cut off access -- if at all.