Code that encrypts world's GSM mobile phone calls is cracked

A German computer engineer said Monday that he had cracked the secret code used to encrypt most of the world's mobile phone calls.
Nohl revealed his success at the Chaos Communication Congress in Berlin, Germany. He said that 24 people worked independently to reproduce the code book, or binary code log, for the algorithm, which contains the equivalent of about two terabytes of data.
He announced his intentions to crack the GSM algorithm at a conference in August.
[Nohl's wiki page for the A5/1 project]
The GSM Association reportedly said that Nohl's actions were illegal in the U.S. and U.K., and said it was unlikely that Nohl had actually cracked the code.
Nohl reportedly said the code book is available on the Internet through BitTorrent.
The issue at the center of it all: should wireless carriers and/or the government take more steps to ensure the security of GSM wireless phone calls?
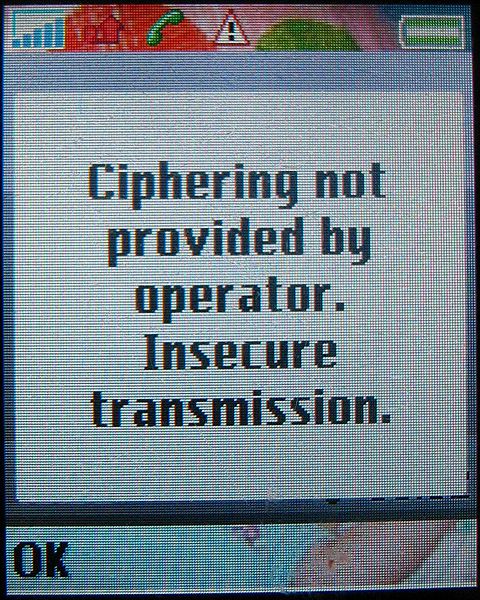
The GSM algorithm is an A5/1 algorithm, a 64-bit binary code now slightly outdated compared to the 128-bit codes used today to encrypt calls on third-generation networks. A successor, called the A5/3 encryption algorithm, was later developed, but most network operators haven't yet implemented it.
A known encryption expert, Nohl has a PhD. in computer engineering from the University of Virginia.
Earlier this year, he exposed weaknesses in the security algorithm for cordless home phones, prompting the DECT Forum, a standards group, to revisit it (.pdf). Nohl previously studied the security of RFID systems.
About 3.5 billion of the 4.3 billion wireless connections across the globe use GSM. In North America, 299 million consumers use the technology.