Former NSA exec: We misjudged potential of insider threats like Snowden

Despite being inside the organisation. the NSA had no idea what Snowden was doing with files.
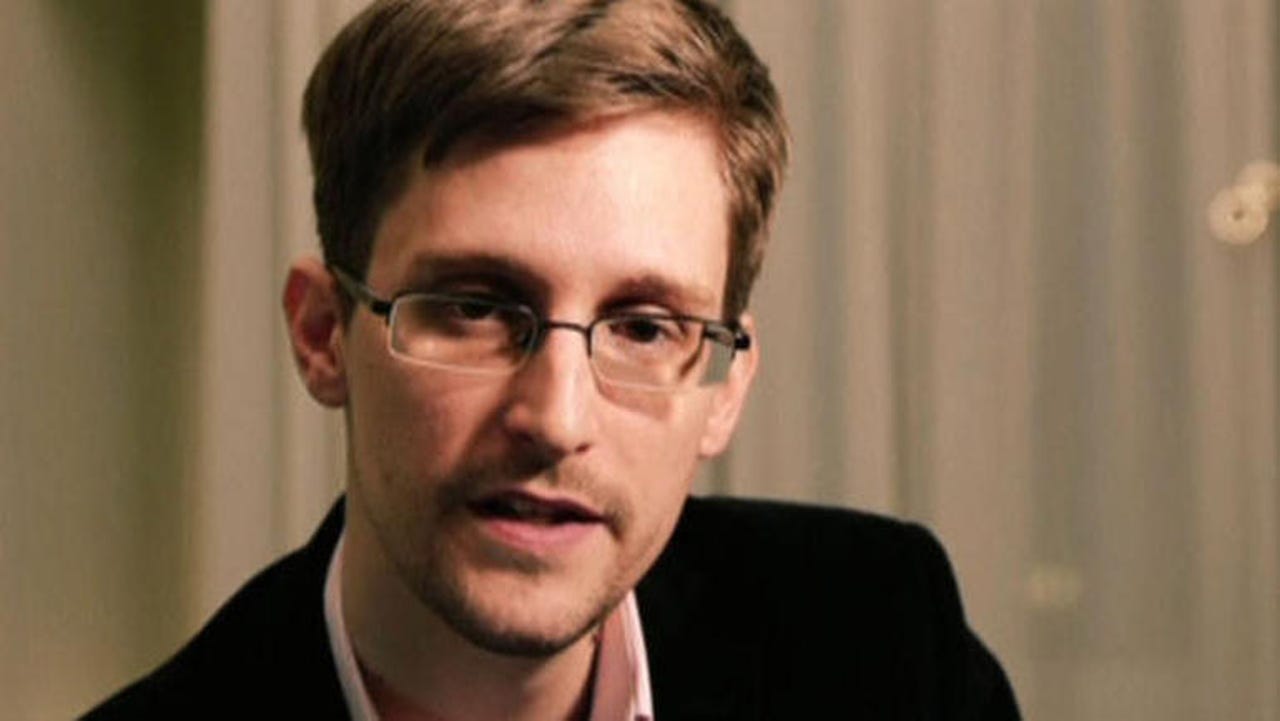
Edward Snowden shocked the world when he released a vast number of files detailing the wide-ranging surveillance schemes being carried out by the US National Security Agency, the UK's GCHQ and other intelligence services across the globe.
Of course, the leak also shocked the NSA, which didn't have any idea that Snowden had systemically accumulated sensitive files then shared them with press across the globe -- all without anyone within the organisation being aware of what he was doing, despite Snowden gathering and storing intelligence for some time.
"What Snowden taught the NSA -- and perhaps many people watching NSA -- is that it's probably very likely we underestimated the probability and the consequences of an insider," says Chris Inglis, former deputy director of the NSA under the Bush and Obama administrations and during Snowden's time at the agency.
Speaking to gathered press at the British Museum, Inglis argued that privileged insiders with a malicious intent now "have an opportunity to do much greater harm, much quicker, much faster" than they once did, due to the number of computers and systems they can find themselves with access to.
As a result, underestimating the consequences of an insider threat can be "extraordinary", and all organisations, not just the NSA, need to raise their game in defending the insider space.
One way to do that, Inglis suggests is simply more stringent checks on who needs access to which data and for how long. After all, the higher the privilege required to access data, the more dangerous it is to allow someone unfettered access to it.
"You can't do it the old fashioned way, which is to simply vet and extend trust to people based on that day; that's got to be the precursor to establishing trust with someone in your system and you need to follow that up with a much more granular and time-sensitive understanding of what they're doing with those privileges," said Inglis, who is now an adviser to the board at cybersecurity firm Securonix.
That, he explains, means organisations can no longer just look to their perimeters when defending against threat, because it's no longer the case that "mischief inside will be caught at the margins and restored to good order". Focusing on external threats ignores the fact that a malicious insider can do a lot more damage and in an even shorter amount of time - all without actually leaving the network.
The answer? Ensuring that those responsible for providing and removing privilege always have an understanding about what's happening to data in real time.
"That means you need to have data about data and you have to have an ability to synthesise that and understand the behaviour associated with that privileged entity, which drives you not to just collection of data, but analytics to make sense of it and coherently understand what's happening," said Inglis.
Ultimately, the former NSA deputy director says, organisations should aim to be able to do what the NSA weren't able to with Snowden, and spot threats before they materialise.
"The goal isn't to react well, or even to track well, it's to anticipate, to see these things coming and step in before the disaster occurs and mitigate it".
The agency is arguably acting on its own advice, as NSA contractor Harold T Martin was recently arrested, accused of stealing thousands of highly classified documents, computers, and other storage devices from the intelligence organisation.