Googling for Conficker clean-up information? Be careful

If you're trawling the Web for information on disinfecting the Conficker worm, be very, very careful.
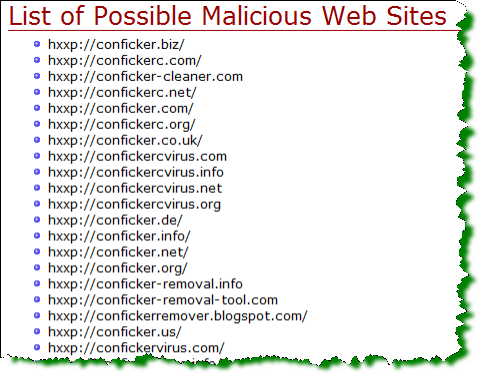
Cyber-criminals are latching onto the hype around the Windows malware threat and have started registering domain names linked to Conficker and poisoning search results to trick users into installing fake anti-virus software programs.
According to this growing list maintained by the Conficker Working Group, at least one of the domains is actively serving malware. F-Secure dug into one of the domains and found an a rogueware (fake anti-virus) campaign attempting to bilk users out of $39.95 for non-existent Conficker clean-up.
Yesterday, just hours after the release of enterprise scanning tools to help fingerprint the virulent worm, search results on Google were poisoned to serve malware for queries related to that news. In one instance, the top Google result for "nmap conficker" was serving up a redirect to a drive-by download exploit site.
Trend Micro has additional details.