Linux Mint website hacked to trick users into downloading version with "backdoor"

A hacker has broken into the website of one of the most-popular Linux version and pointed users to malicious download links that contained a "modified" version of the software.
The surprise announcement was made Saturday, shortly after the breach was detected.
In a blog post, Clement Lefebvre, head of the Linux Mint project -- said to be the third most-popular version of the open-source operating system after Ubuntu and Fedora -- confirmed the breach.
"Hackers made a modified Linux Mint ISO, with a backdoor in it, and managed to hack our website to point to it," he said.
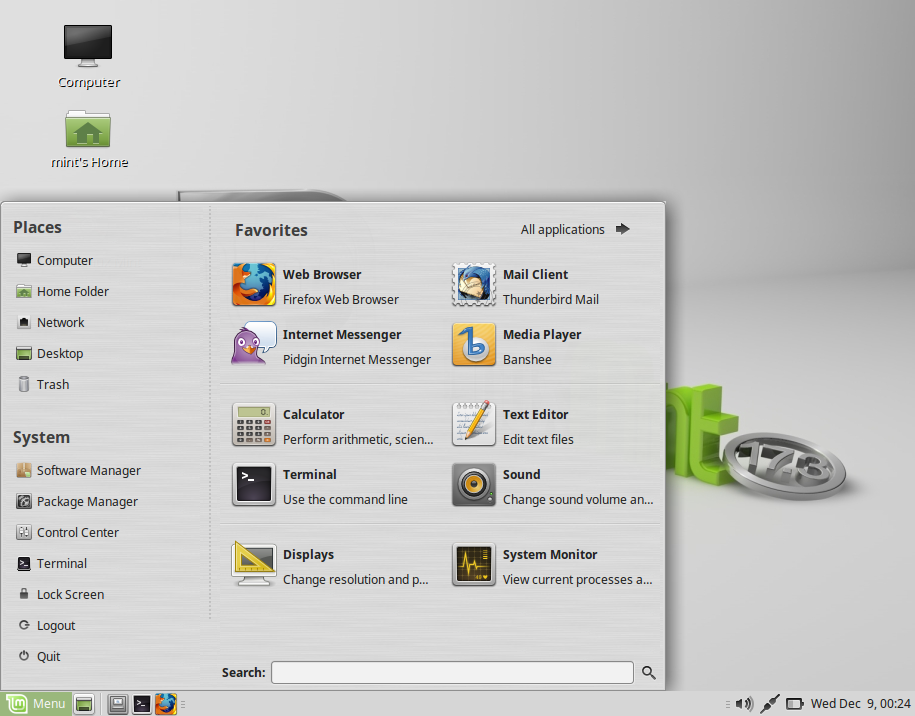
"As far as we know, the only compromised edition was Linux Mint 17.3 Cinnamon edition," he added. "If you downloaded another release or another edition, this does not affect you. If you downloaded via torrents or via a direct HTTP link, this doesn't affect you either."
Lefebvre said only downloads from Saturday were compromised.
Shortly after the announcement, the project's website was pulled offline.
Lefebvre said the hacked download image files -- used to install the Linux operating system -- were hosted on a server based in Bulgaria. Micah Lee, security engineer and reporter at The Intercept, posted on his blog with more details, saying that the hacker loaded the Tsunami botnet malware on the disk image. Tsunami allows an attacker remote access to an infected machine.
Lefebvre said in this case the backdoor connects to "absentvodka.com," which at the time of writing does not appear to be online.
It's thought the Linux distro's website and forum was stolen in the breach.
CSO's Steve Ragan found an ad on a dark web site claiming to have a "full forum dump" of the site, with a going rate of about 0.197 bitcoin, or about $85 per download. (We were able to verify the listing exists, but could not speak to its authenticity.)
Lefebvre confirmed the site was hacked through its outdated WordPress installation, but he denied that using HTTPS site encryption would have mitigated the attack.
"You'd be served the exact same hacked information via HTTPS," he said.
Lee also criticized the site's lack of encryption, arguing that the checksums on the site could easily be modified by an attacker to trick the user into downloading a verified build.
"If a hacker can hack the website to modify the download link, they can modify the checksum at the same time to match their malicious download," he said.
"Verifying is PGP signatures is more complicated and harder to explain than comparing checksums, but it's actually secure. It's the only way to be sure that a Linux installer ISO you download hasn't been tampered with since the image was built by the developers," he added.