Lockerpin ransomware steals PINs, locks Android devices permenantly

[Update 12/9: ESET clarification on biometric locks]
A new strain of Android malware is the first true example of ransomware able to permanently lock a smartphone or tablet.
While mobile malware isn't a very common threat, code which strikes mobile operating systems is slowly gaining traction -- unsurprising when you consider how much sensitive data is often stored on our devices and how much we have learned to rely on them.
Ransomware is software which locks a victim's system and encrypts files to prevent retrieval. If a victim wishes to unlock their system, they are usually faced with a demand for payment in virtual currency, which is then sent to the cybercriminals controlling the malware. Keys are then sent to the victim to unlock their PC and decrypt their files.
This particularly nasty strain of malware is most often seen on standard PC systems but over the past year examples of ransomware tailored for mobile systems have been detected in the wild.
Simplocker, detected last year, was the first registered strain of ransomware able to encrypt user files across a mobile device or tablet. However, a new type which sets the phone's PIN lock reveals how mobile ransomware is rapidly evolving to snare more victims.
See also: The ransomware guide: protection and eradication
Detected as Android/Lockerpin.A, ESET researchers say the new strain is the first known example of Android ransomware setting this kind of lock, which makes the device incredibly difficult to unlock without losing data.
Featured
In previous ransomware samples, the screen-locking functionality was achieved by pushing the ransom window to the foreground in an infinite loop. While annoying, the ransomware could be easily eradicated through uninstalling the malicious application which contained the malware through Safe Mode, or alternatively through Android Debug Bridge (ADB).
Unfortunately, Lockerpin is more advanced, leaving "no effective way" to regain access without root privileges or security software already installed on a device -- unless victims elect to perform a factory reset which would wipe out all the information and apps stored on the device.
"Moreover, this ransomware also uses a nasty trick to obtain and preserve Device Administrator privileges so as to prevent uninstallation. This is the first case in which we have observed this aggressive method in Android malware," the researchers say.
The malicious app containing the ransomware Trojan is dubbed "Porn Droid" and masquerades as an adult video streamer. The majority of infected devices detected are within the United States, although infections have been spotted worldwide.
After the app has been downloaded and installed, the malware attempts to gain administrator rights through a fake "Update Patch Installation" window shown to the victim. If the victim falls for the ploy and clicks through, they unknowingly grant the app Device Administrator privileges thanks to a hidden underlying window.
Once clicked, it is too late -- as the malware locks the device and sets a new PIN for the lock screen. ESET researchers did not include biometrics as part of the testing, and told ZDNet they did not want to speculate.
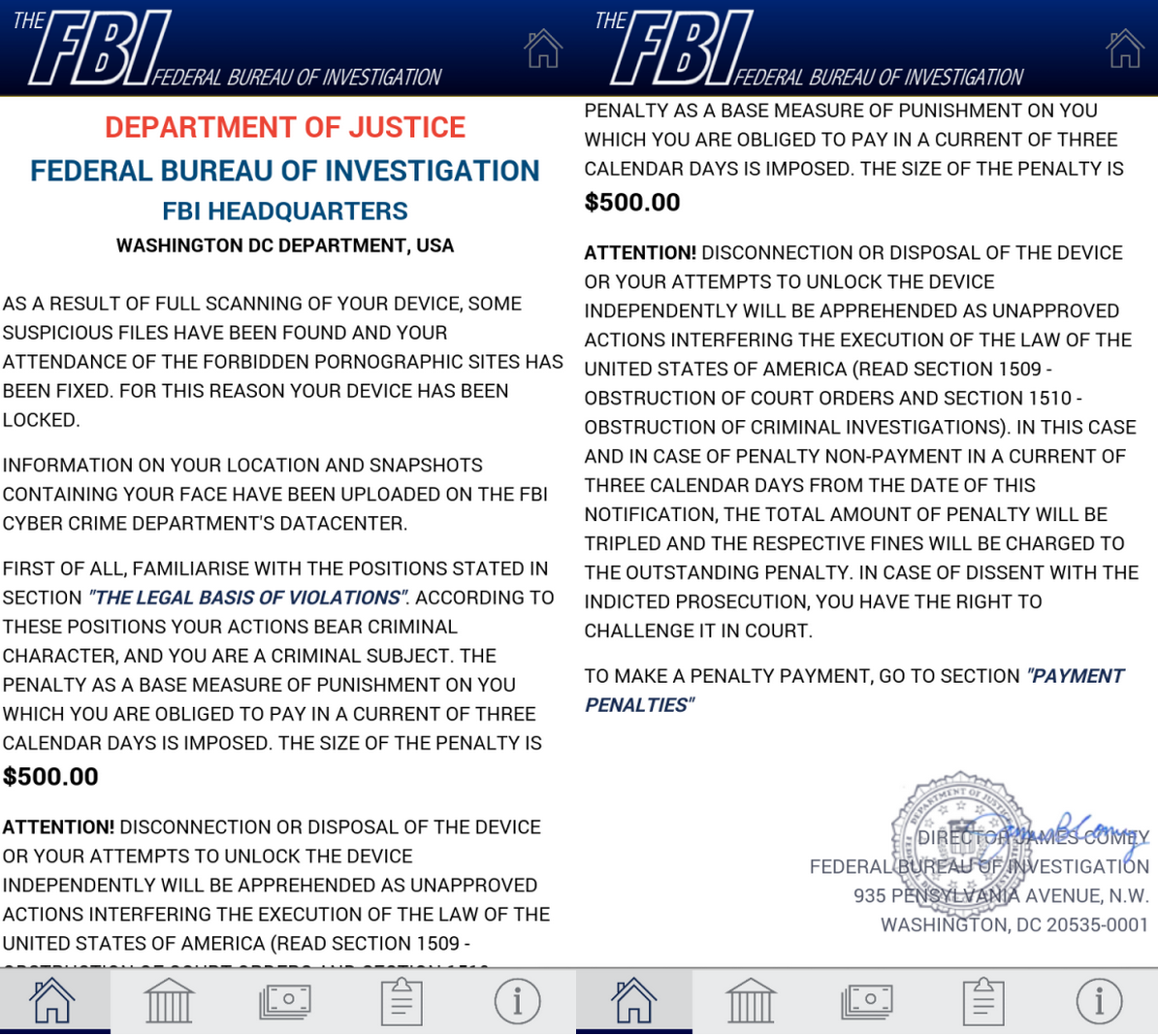
Once a mobile device is firmly locked, the user is given a demand to pay $500 for allegedly viewing illegal pornographic material.
If a user attempts to rescind administrator rights, a call-back function set within the malware reactivates the privileges by forcing the victim back to the fake update screen. In addition, if antivirus software from ESET, Avast or Dr.Web is detected, the Trojan attempts to kill these processes.
While the app can then be uninstalled through Safe Mode or ADB, there is a problem. The PIN code is generated randomly and neither attacker nor victim has access to this -- and so the only way to unlock a device properly is to perform a factory reset.
The saving grace for users is that the malicious application cannot be downloaded from the Google Play Store. If you choose to download apps from other sources -- such as third-party markets or through torrent software -- you run the risk of becoming infected as apps have not been passed through Google's security systems.
10 steps to erase your digital footprint
Read on: Top picks
- How to access Wi-Fi anonymously from miles away
- Flic: The wireless button which brings the connected world into your home (hands-on)
- Adblock Plus Google Play exile ends, launches iOS, Android browser
- One password gifts hacker with hundreds of Firefox bugs, vulnerabilities
- Fiat Chrysler recalls 8,000 extra Jeeps over remote control hacking worries