Microsoft's URL detonation: Now Office 365 can zap key spear-phishing tactic

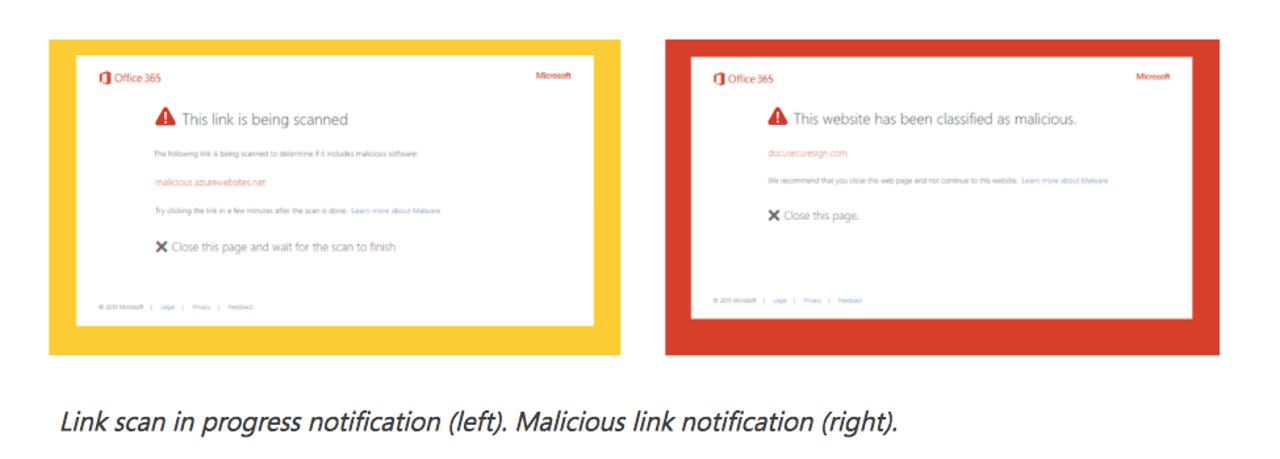
Microsoft's Office 365 URL detonation feature displays a yellow pop-up window while links are scanned.
Microsoft has rolled out a new 'URL detonation' feature in Office 365, which aims to neutralize one of the key tactics used by advanced hackers to breach a network.
Spear-phishing might not be technically sophisticated, but it works, as last year's DNC hacks demonstrated. The Russian hacking group widely blamed for those attacks emailed their targets bit.ly links that led to domains spoofing users' real web-mail page to snag credentials.
Similar hacking groups send emails with links to a malicious file that, once executed, downloads a remote access tool.
Microsoft's new Office 365 URL detonation service should help mitigate the second type of phishing attack, targeting malicious files, such as a PDF or webpages, linked to by URLs in an email. The feature was released to some users last year as part of Office 365 Advanced Threat Protection (ATP) and on Thursday was made available to all users.
ATP will now run a URL reputation check and analyze URLs in email for malicious behavior. When the URL is being scanned, users will see a yellow pop-up window with a message that says, "This link is being scanned". If Microsoft identifies the link as fraudulent, the user will see a red message box stating, "This website has been classified as malicious".
Admins can also set a SafeLink policy to track which of their users click through to the link, allowing them to respond if a user ignores the warning.
In addition Microsoft has announced the public preview of ATP Dynamic Delivery with Safe Attachments, which is designed to minimize disruptions as it scans emailed attachments.
Recipients can read the email body while the attachment is being scanned. If Microsoft detects it as malicious, it will automatically filter the attachment. It will reinsert an attachment it has deemed safe. This feature was available in a private preview last year.
"Dynamic Delivery delivers emails to the recipient's inbox along with a 'placeholder' attachment notifying the user that the real attachment is being scanned, all with minimal lag time," Microsoft said.
Microsoft has published a walkthrough for admins who want to enable the two security features.
Read more about spear-phishing
- Obama, Feds outline technical, spear phishing details, sanctions vs. Russia over cyber attacks
- The hackers that never went away: Brace for more state-backed attacks, leaks and copycats this year
- Spearphishing and how to stop it: Some lessons from AusCERT
- Simple eBay security flaw exposed millions of users to spear phishing campaigns