Phishers targeting Facebook users, fake logins spammed through hacked accounts
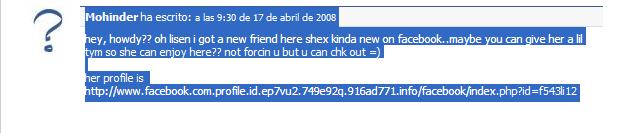
A currently active phishing campaign is circulating across Facebook end users' walls, using already compromised accounts to post the phishing links, tricking the user into thinking it's a legitimate friend sending the message in order to redirect them to a fake login page. The campaign is taking advantage of multiple typosquatted domains which are in a fast-flux state, namely, they respond to multiple IP addresses and change them automatically every three minutes in this particular attack.
Sample phishing URLs used look like the following :
facebook.com.profile.id.ep7vu2.749e92q.916ad771.info facebook.com.profile.id.mgt9fr5n.mg6qdo.e77c98037.com facebook.com.profile.id.bvbu38.krpz.dortos.net facebook.com.profile.id.10g10th3.7q342k8.31dd6db6.com
This is not the first, and definitely not the last time Facebook's been under attack by phishers and malware authors. For instance, at the beginning of the year, a malware serving phishing attack that was originally targeting MySpace, switched to Facebook "in between" two months later. What's "the instant nature of social networking" to some, is real-time spamming capabilities to others, who based on the number of accounts hacked, would be able to efficiently spam any social network.
Sometimes, your hacked friends are not to be trusted but warned, so that they get the chance to change their passwords and no longer participate in phishing attacks through their accounts.