Ransomware: Now cybercriminals are stealing code from each other, say researchers

The code for the highly successful Petya ransomware has been stolen.
Ransomware is already one of the easiest forms of online extortion for hackers to carry out but one cybercriminal group has come up with a new way to make as much money as possible with the least effort: by stealing ransomware code from others, according to researchers.
The Petya ransomware family is particularly vicious, not only encrypting the victims' files using one of the most advanced cryptographic algorithms, but also encrypting the entire hard drive by overwriting the master reboot record, preventing the computer from loading the operating system.
Like other forms of ransomware, Petya extorts a Bitcoin ransom from the victim in exchange for unencrypting the system.
Petya was one of the first types of ransomware to gain major success by spreading itself via a ransomware-as-a-service scheme, in which the creators offered their product to users on demand, in exchange for a cut of the profits. In an effort to ensure their creation wasn't exploited by others, Petya was equipped with measures to prevent the unauthorised use of samples.
However, the authors of a new form of malware dubbed PetrWrap have managed to crack the Petya code and are using it to perform ransomware attacks, apparently without paying the creators of Petya, according to researchers at security company Kaspersky Lab.
It said the PetrWrap Trojan has been active since February this year and uses its own cryptographic keys to lock victims' files, rather than using those which come with the 'stock' version of Petya -- and waits for an hour and a half after the initial compromise before striking.
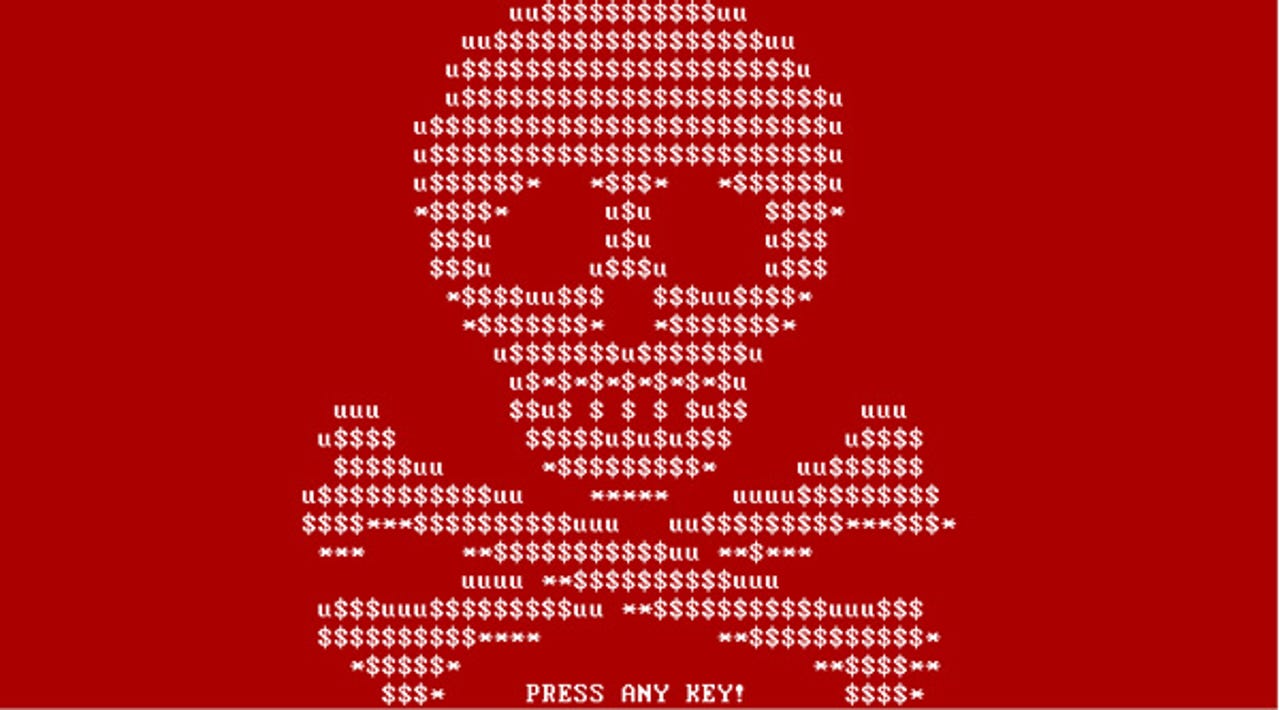
PetrWrap ransom note.
Currently, it's unknown who the group distributing PetrWrap is or how it's being distributed. However, the very fact it exists appears to demonstrate competition and rivalries in the cybercriminal underground, with the potential that gangs will get distracted by fighting for dominance.
"We are now seeing that threat actors are starting to devour each other. From our perspective, this is a sign of growing competition between ransomware gangs," says Anton Ivanov, senior security researcher at Kaspersky Lab
"Theoretically, this is good, because the more time criminal actors spend on fighting and fooling each other, the less organised they will be, and the less effective their malicious campaigns will be."
However, that doesn't mean that you should take their eye of the ball when it comes to protecting against ransomware.
"We urge organisations to pay as much attention as possible to the protection of their networks from this kind of threat, because the consequences can be really disastrous," Ivanov added.
Indeed, getting infected with PetrWrap could be very dangerous for a company because the cryptography of this ransomware is so strong that there currently are no decryption tools available.
READ MORE ON CYBERCRIME
- Ransomware: An executive guide to one of the biggest menaces on the web
- Europol, Intel and Kaspersky team up to crack down on ransomware [CNET]
- Ransomware: What would you do? One in three infected organisations pay hackers to get data back
- Tech support scams evolve, borrow tricks from ransomware creators
- I infected my Windows computer with ransomware to test RansomFree's protection [TechRepublic]