The sorry state of security software

Over the years, I’ve made no secret of my distrust of the Windows security software industry. With the security tools in Windows XP Service Pack 2 and Windows Vista, an alert Windows user is protected from the overwhelming majority of security threats and has to actually participate in any plot to infect his or her PC. That’s bad news for the ringleaders of the security software racket, who want to keep you afraid so you’ll buy more stuff from them.
In 2005, I wrote this:
On a healthy computer with multiple layers of security, most threats should be blocked or neutralized before the user ever sees them. Getting lots of warnings is a sign that one of those layers isn’t working as well as it should. But that’s exactly the opposite of what motivates developers of security software today.
Three recent experiences convince me it’s even more true today.
Problem #1: Too much security software. Three weeks ago, when I was in Arizona, I stopped by a friend’s house in response to a desperate plea to check her computer’s performance: “It’s so freaking slow, it takes more than a lifetime to do anything, even open an e-mail. I’m beyond frustrated with this thing.”
It took me about 20 seconds to confirm that she had a problem. Opening a browser of any kind took minutes. It took another 20 minutes to find and fix the problem. Her resident computer expert, no doubt trying to be helpful, had loaded this computer with no fewer than six security programs – three antispyware programs, two system cleaners, and an all-in-one security suite. The culprit in this case was Webroot Software’s Window Washer. I removed it and four other redundant programs, leaving behind only Norton Internet Security. After a reboot, the machine was back to its snappy self.
The moral: Adding more security software does not make your system more secure, but it sure can make it less stable.
Problem #2: Overaggressive security software. Microsoft developer Aaron Stebner reported this one. If you’re running Tenebril SpyCatcher, it can interfere with your ability to install the .NET Framework components used by dozens of different applications. As Aaron notes:
[I]n the cases I've seen so far, closing or disabling Tenebril SpyCatcher is not enough to resolve this issue. The customers I have talked to have had to fully uninstall Tenebril SpyCatcher in order to get the .NET Framework to install successfully.
Even worse was this report from a few months ago that a routine scan by Spybot Search And Destroy could wipe out crucial system files on a Tablet PC.
Problem #3: False positives. Is Apple’s QuickTime some sort of high-risk parasite? The good folks at Trend Micro think so. Yesterday, I installed Trend Micro’s PC-Cillin Internet Security 2007 here. It’s an excellent antivirus program and firewall, but as I’ve documented in the past, its antispyware capabilities leave something be desired.
Sure enough, after I gave in to its nagging to perform a full scan, it reported back to me that my system was infested with “118 dangers.” Good heavens!
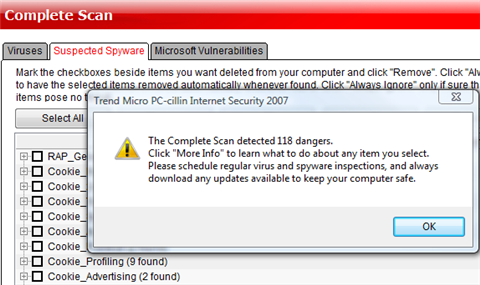
A closer look revealed that maybe things weren’t so bad after all. At least four of those “dangers” were multiple sightings of Apple’s Quick Time tray icon, Qttask.exe. Following the link for more info took me to a page that simply described the qualities of a generic “remote access program” (i.e., a Trojan horse) with no indication of why this one had been flagged.
The scan also turned up a handful of password-cracking utilities I keep on hand for testing, and for some reason it flagged the Keyfinder utility, which you can use to retrieve your Windows and Office product keys from the registry. The developer of the Keyfinder utility is none too happy about this:
Another thing I'd like to address is all of the emails I've been receiving saying the Keyfinder is infected with a virus. No... it's not. Your virus scanner, essentially, is being overprotective. It's trying to do more than scan for viruses. With today's wonderful world of spyware, it seems that a lot of scanners out there are identifying software that "can be used by a malicious user for malevolent purposes." (That is a direct quote from the Trendmicro write-up for the Keyfinder.)
In this case, too, the More Info links didn’t provide any useful information to help me make a better, more informed trust decision.
The remainder of the threats were simply cookies. Security software companies love to pick on cookies from advertising companies, because it allows them to appear to be aggressively fighting dangerous things that they can clean up for you. The more they find, the more valuable they appear to be.
I wrote about this two years ago in a discussion of a post by Joe Wilcox, who was feeling relieved because Norton Antivirus had apparently saved him from a nasty Trojan horse program.
And it illustrates everything that is wrong with the commercial security software business. Joe feels good because the software told him it had protected him, even though the likelihood that this was an actual attack is microscopic. The lesson that Joe is unwittingly sending to the vendors in question is, “Give me more false positives, because the more times you tell me you’ve protected me from something, the more I’ll feel like I’ve gotten my money’s worth from your software.” If he had a better security program, it would have realized that this outgoing connection was just fine and would not have given him any warning at all.
If your burglar alarm goes off 12 times a day, does it make you feel more secure? The best security system is one that does its job silently and effectively.