Under malware attack: Smart cards used by U.S. government agencies

Security researchers have nabbed a new variant of an well-known backdoor Trojan called Sykipot targeting the smart cards used by U.S. government employees to access restricted servers and networks.
According to a warning from Alienvault Labs, the latest strain of Sykipot is linked to the kinds of extremely targeted attacks originating in China and aimed at U.S. government agencies.
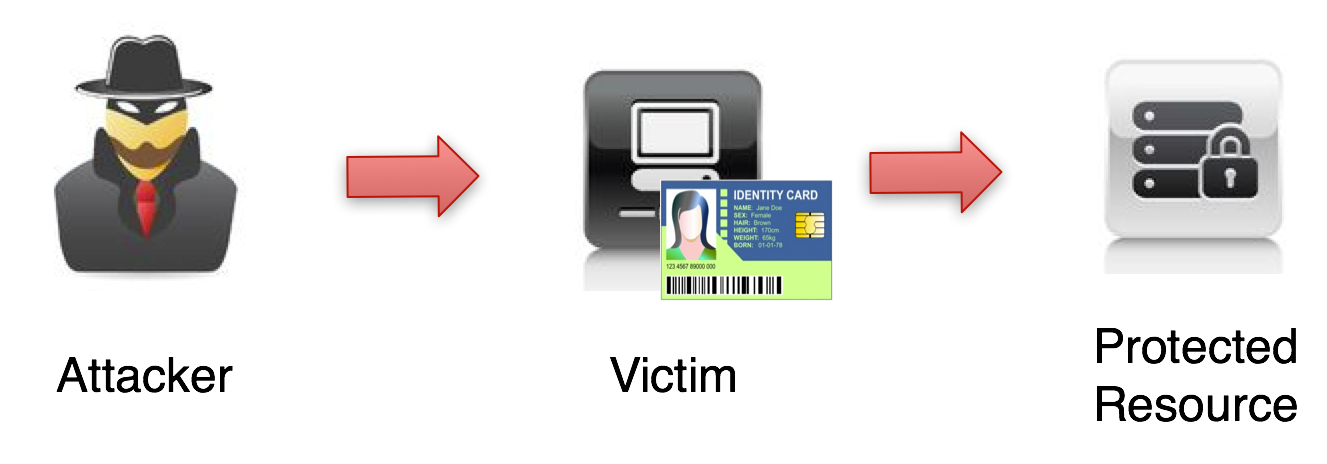
We have seen how the attackers are implementing different techniques to bypass two-factor authentication with smartcard/PIN to access protected resources on the victim?s network. By capturing the PIN for the smartcard and binding the certificate, malware can silently use the card to authenticate to secure resources, so long as the card remains physically present in the card reader.
"While trojans that have targeted smart cards are not new, there is obvious significance to the targeting of a particular smart card system in wide deployment by the US DoD and other government agencies, particularly given the nature of the information the attackers seem to be targeting for exfiltration," Alienvault said.
The company said this attack is targeted at smart card readers made by ActivIdentity, a company that provides authentication software to several high-profile agencies and businesses around the world. The New York Times reports that ActivIdentity’s smart cards are used by employees at the Defense Department, Department of Homeland Security, Coast Guard, Social Security Administration, Treasury Department and other government agencies, along with businesses including Monsanto, BNP Paribas and Air France.
In this latest Sykipot malware run, Alienvault said the modus operandi of the attackers is to list the certificates present on the victim's computer (including the smart cards) and to steal the PIN using a keylogger module. THis information is then used to log onto remote resources protected with certificates and smart cards.
In the past the Sykipot malware has been seen exploiting zero-day vulnerabilities in Adobe Reader. Over on Threatpost, Paul Roberts has a really good story on the intricacies of these high-end espionage attacks.