Wi-Fi Protected Setup is Busted

I've never trusted Wi-Fi Protected Setup (WPS) on my Wi-Fi access points (AP) and routers. I've always thought that anything that was that easy to set up had to be easy to hack. It turns out my gut was right. The U.S. Computer Emergency Readiness Team (CERT) has confirmed that security researcher Stefan Viehböck has found a security hole big enough to drive a network through WPS.
According to Viehböck, he took a look at WPS and found "a few really bad design decisions which enable an efficient brute force attack, thus effectively breaking the security of pretty much all WPS-enabled Wi-Fi routers. As all of the more recent router models come with WPS enabled by default, this affects millions of devices worldwide." CERT agrees.
How bad is it? CERT states that "An attacker within range of the wireless access point may be able to brute force the WPS PIN and retrieve the password for the wireless network, change the configuration of the access point, or cause a denial of service."
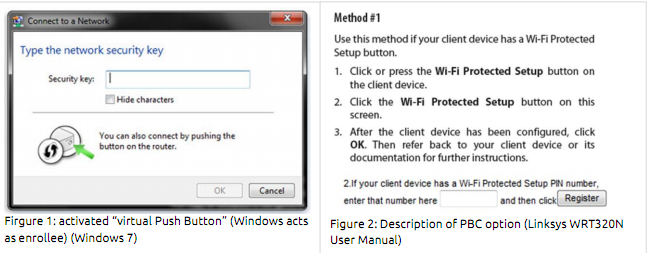
The problem is, as Viehböck explains in detail (PDF Link) is that when the device's personal identification number (PIN), which is usually implemented as a simple physical or virtual push-button, authentication fails the access point will send an Extensible Authentication Protocol-Negative Acknowledgement (EAP-NACK ), which are sent in away that lets a hacker know if the first half of the PIN is right. Then, armed with that information, the attacker will be able to figure out the PIN's last digit of the PIN is known since it's is a checksum number for the entire PIN. What all that means is that it becomes much easier to work out a PIN. To be exact, with the worse luck in the world it would take a cracker 11.000 attempts to break the code.
Think that sounds safe enough? Think again. It seems most APs and routers from such big name vendors as Buffalo, D-Link, Cisco Linksys, Netgear, Technicolor, TP-Link, and ZyXEL won't stop an automated hack from trying one PIN after another. They'll just let the brute-force attacks continue-in the process quite likely knocking the WI-Fi devices off-line from this de facto denial of service attack-until they get the right PIN.
After that your network security goes out the window. A cracker can read your e-mail, grab your credit card passwords and on and on.
What's the fix for this? There isn't one. To quote, CERT, "We are currently unaware of a practical solution to this problem."
So what can you do? You need to log-in to your wireless device and disable WPS. Next, you'll need to reset your Wi-Fi network to manually use at WPA2 with Counter Mode with Cipher Block Chaining Message Authentication Code Protocol (CCMP), aka Advanced Encryption Standard (AES), Other, older WI-Fi security methods, such as Wi-Fi Wired Equivalency Privacy (WEP) and WPA (Wi-Fi Protected Access), with the built-in Temporal Key Integrity Protocol (TKIP) have long been broken.
Unfortunately, since WPS was expressly designed to be used by people without a clue about network security, the people who are going to need to implement these security fixes are the ones who are least able to make them.
The real fix is going to need to come from the vendors with firmware updates. Until that's done, many home and small office Wi-Fi networks must be considered about as safe as a house with an unlocked front-door.
Related Stories:
Firesheep's Real Lesson: Take Wi-Fi Security Seriously
FaceTime calls are encrypted; and HIPAA compliant when using proper encryption
How to keep your Wi-Fi location out of Google
Finding and cleaning out your smartphone's Carrier IQ poison