Windows kernel 'zero-day' found in Duqu attack

The mysterious Duqu malware attack exploited a zero-day vulnerability in the Windows kernel, according to security researchers tracking the Stuxnet-like cyber-surveillance Trojan.
Researchers at the Laboratory of Cryptography and System Security (CrySyS) in Hungary confirmed the existence of the zero-day vulnerability and exploit in a brief note posted to its web site.
Our lab, the Laboratory of Cryptography and System Security (CrySyS) pursued the analysis of the Duqu malware and as a result of our investigation, we identified a dropper file with an MS 0-day kernel exploit inside. We immediately provided competent organizations with the necessary information such that they can take appropriate steps for the protection of the users.
The vulnerability has since been reported to Microsoft. However, the company has not yet issued a security advisory to provide pre-patch mitigation guidance to Windows users.
One version of the attack was triggered by a rigged Microsoft Word .doc that probably included some social engineering and required the target to open the booby-trapped file. However, since this is a kernel vulnerability, it is possible that other attack vectors have been/could be used.
Here's more information on the zero-day component from Symantec:
Once Duqu is able to get a foothold in an organization through the zero-day exploit, the attackers can command it to spread to other computers. In one organization, evidence was found that showed the attackers commanding Duqu to spread across SMB shares. Interestingly though, some of the newly infected computers did not have the ability to connect to the Internet and thereby the command-and-control (C&C) server. The Duqu configuration files on these computers were instead configured not to communicate directly with the C&C server, but to use a file-sharing C&C protocol with another compromised computer that had the ability to connect to the C&C server. Consequently, Duqu creates a bridge between the network's internal servers and the C&C server. This allowed the attackers to access Duqu infections in secure zones with the help of computers outside the secure zone being used as proxies.
While the number of confirmed Duqu infections is still limited, using the above techniques we have seen Duqu spread across several countries. At the time of writing, Duqu infections have been confirmed in six possible organizations in eight countries.
Symantec also reported the recovery of a new Duqu sample that communicates with a different C&C server. All previously analyzed samples were configured to contact a server hosted in India. This particular Duqu file was configured to communicate with a server in Belgium with the IP address '77.241.93.160'.
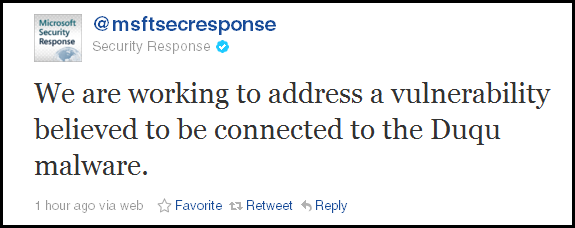
UPDATE: Still no formal security advisory from Microsoft but we now have a confirmation via the Microsoft Security Response Center's Twitter account.
"We are working to address a vulnerability believed to be connected to the Duqu malware."
Here's a direct quote from Microsoft's Jerry Bryant:
"Microsoft is collaborating with our partners to provide protections for a vulnerability used in targeted attempts to infect computers with the Duqu malware. We are working diligently to address this issue and will release a security update for customers through our security bulletin process."
ALSO SEE: