Windows malware: are you safer today than you were 10 years ago?

They don’t make malware like they used to.
That’s not a setup for a joke—it’s a fact. As I was researching some recent columns on malware outbreaks for PCs and Macs, I found myself reading old articles about computer security from the beginning of the 21st Century. Some of those articles and the threats they describe seem downright quaint in retrospect, while others were positively prescient.
During my research, I bookmarked a lot of web pages and made copious notes about threats that gave IT professionals ulcers and PC support staffs headaches in their time. And it struck me that the cat-and-mouse game between malware authors and their targets has evolved dramatically during that time.
In depth: Ten years of Windows malware and Microsoft's security response
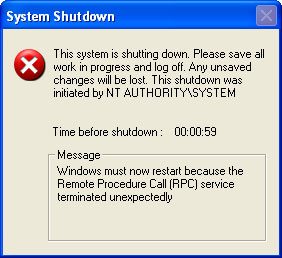
Take a trip down bad memory lane and revisit some of the worst offenders of the last decade. from primitive but effective early efforts like Blaster (2003) and Zlob (2005), to more deadly modern threats like the Zeus botnet and the Alureon (aka TDL4/TDSS) rootkit. During that same time, Microsoft was introducing its Patch Tuesday update program, the Malicious Software Removal Tool, and a variety of legal and technical efforts that effectively neutralized some threats. My timeline puts the bad guys’ work and Microsoft’s response into perspective. Here, for example, are the telltale marker of the Blaster worm and the XP SP2 Security Center, side by side:
My decision to go back 10 years is no accident. One of the watershed events in the ongoing battle between the white hats and black hats of PC security happened exactly a decade ago.
In January 2002, after a series of widespread, high-profile, and highly embarrassing security incidents that affected Windows customers and Microsoft itself, Bill Gates wrote his now famous “Trustworthy Computing” memo. Although it was viewed with some skepticism at the time, it really did represent a turning point for Microsoft and for Windows users.
Until that point, security was literally an afterthought. As a result of the Trustworthy Computing initiative, Microsoft introduced a massive change in the way it develops software. The Security Development Lifecycle has paid off hugely over the last 10 years and has been widely praised and copied.
The bad guys and their products have changed during the same time. At the beginning of the century, the most noteworthy attacks were calculated to wreak havoc and garner worldwide attention. Over the past 10 years, malware authors have gotten more skilled at monetizing their work, and they’ve also learned the benefits of stealth.
In addition to building a more disciplined process for writing secure code, Microsoft has improved its update infrastructure and worked closely with outside security experts and third-party developers to improve the way their products work. Over time, Microsoft has built its own antivirus and network intrusion software; now that the 2001 antitrust agreement has officially ended, that software will finally appear in Windows itself.
Microsoft’s record on security is far from perfect. In Windows XP, for example, it introduced an effective firewall and then chose to leave it turned off by default. That mistake was corrected in XP Service Pack 2. One of the most brutally effective vectors for malware over the past four years has been a feature called AutoRun, which made every USB flash drive a delivery vehicle for the Conficker worm. AutoRun was disabled in Windows 7 by default, but Windows XP and Vista users had to wait until 2011 for a Critical update that blocked that dangerous vector.
There is no question that you are more secure using a modern version of Windows than you were in 2002 using the initial release of Windows XP. At the same time, attackers are more sophisticated and more focused on financial gain.
To learn how we got here, please continue reading: Ten years of Windows malware and Microsoft's security response…