8% of all Google Play apps vulnerable to old security bug

Around 8% of Android apps available on the official Google Play Store are vulnerable to a security flaw in a popular Android library, according to a scan performed this fall by security firm Check Point.
The security flaw resides in older versions of Play Core, a Java library provided by Google that developers can embed inside their apps to interact with the official Play Store portal.
SEE: Meet the hackers who earn millions for saving the web, one bug at a time (cover story PDF) (TechRepublic)
The Play Core library is very popular as it can be used by app developers to download and install updates hosted on the Play Store, modules, language packs, or even other apps.
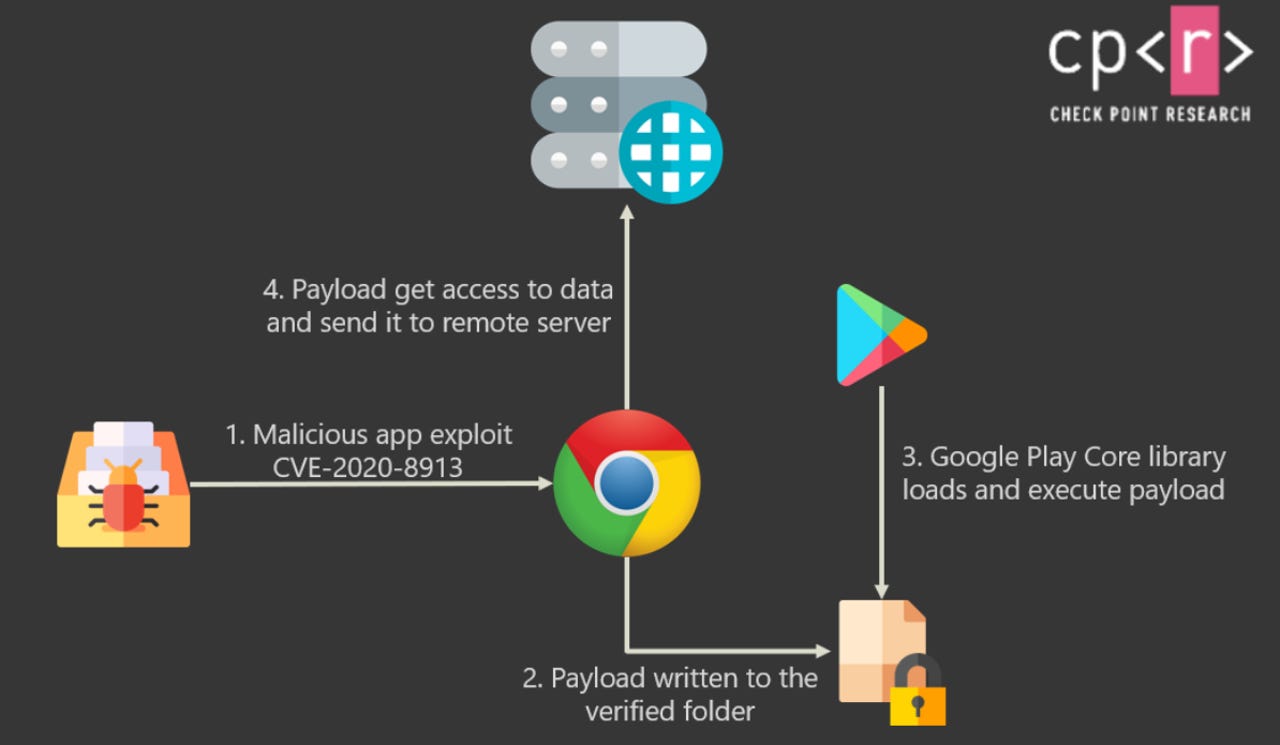
Earlier this year, security researchers from Oversecured discovered a major vulnerability (CVE-2020-8913) in the Play Core library that a malicious app installed on a user's device could have abused to inject rogue code inside other apps and steal sensitive data — such as passwords, photos, 2FA codes, and more.
A demo of such an attack is available below:
Google patched the bug in Play Core 1.7.2, released in March, but according to new findings published today by Check Point, not all developers have updated the Play Core library that ships with their apps, leaving their users exposed to easy data pilfering attacks from rogue apps installed on their devices.
According to a scan performed by Check Point in September, six months after a Play Core patch was made available, 13% of all the Play Store apps were still using this library, but only 5% were using an updated (safe) version, with the rest leaving users exposed to attacks.
Apps that did their duty to users and updated the library included Facebook, Instagram, Snapchat, WhatsApp, and Chrome; however, many other apps did not.
Among the apps with the largest userbases that failed to update, Check Point listed the likes of Microsoft Edge, Grindr, OKCupid, Cisco Teams, Viber, and Booking.com.
Check Point researchers Aviran Hazum and Jonathan Shimonovich said they notified all the apps they found vulnerable to attacks via CVE-2020-8913, but, three months later, only Viber and Booking.com bothered to patch their apps after their notification.
"As our demo video shows, this vulnerability is extremely easy to exploit," the two researchers said.
"All you need to do is to create a 'hello world' application that calls the exported intent in the vulnerable app to push a file into the verified files folder with the file-traversal path. Then sit back and watch the magic happen."
This research shows, once again, that while users may be using an up-to-date version of their apps, that doesn't necessarily mean all of an app's inner components are up-to-date as well, with software supply chains often being in complete disarray, even at some of the world's biggest software/tech firms.