Avast and Emsisoft release free decrypters for BigBobRoss ransomware

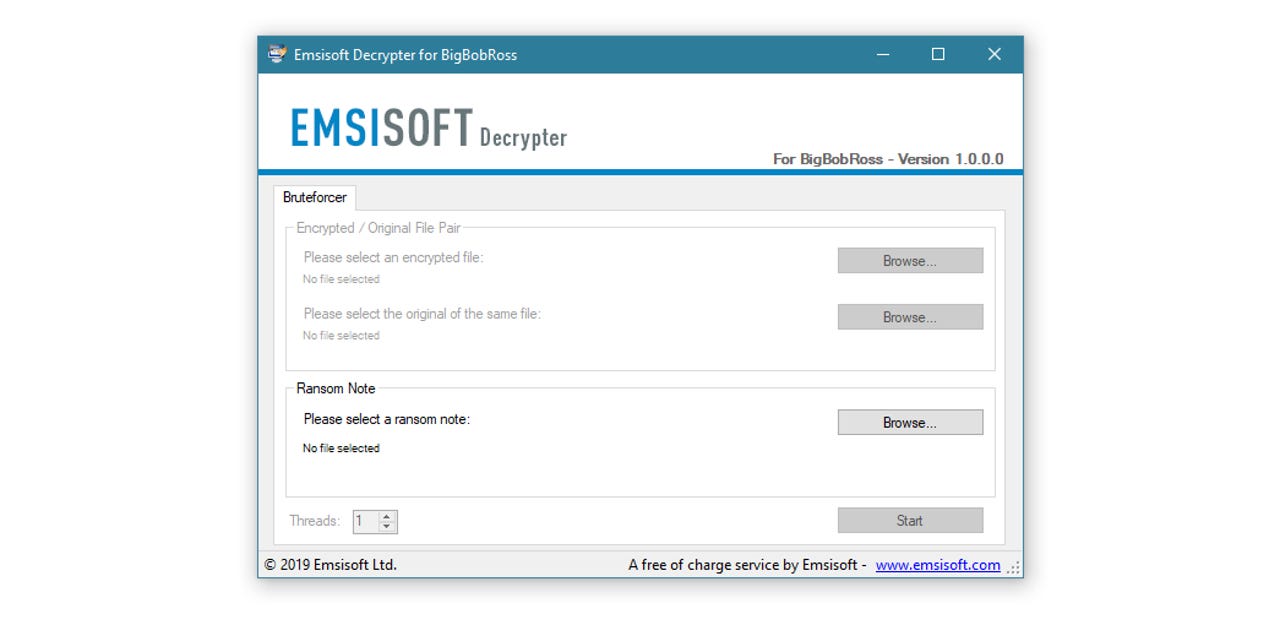
Avast and Emsisoft, two cyber-security firms known for their antivirus products, released today free decrypters that can help victims of the BigBobRoss ransomware recover their files without paying the ransom demand.
The two decrypters are available for download from the Avast and Emsisoft sites, respectively.
The ransomware is one of the smaller strains that has been silently infecting victims for the past two months while larger ransomware operations like GandCrab, Ryuk, BitPaymer, SamSam, or Matrix have been grabbing all the headlines.
Emsisoft security researcher Michael Gillespie told ZDNet that the first sighting of BigBobRoss was on January 14, when some victims tried to identify the ransomware via ID-Ransomware, a service Gillespie built years ago to help victims determine the name of the ransomware that infected their systems.
Gillespie said he received 35 submissions from users across six countries that were later identified as BigBobRoss victims. But not all victims know to use this service, so the number of infected victims could be much higher.
It is unclear how the BigBobRoss crew operates to spread the ransomware or infect victims, at the time of writing.
"At least one victim on BleepingComputer did mention a server was hacked, but I've not heard anything else from victims about the infection vector, unfortunately," Gillespie said.
Besides using the ID-Ransomware service, victims can easily determine if they've been infected by the BigBobRoss ransomware based on some visual queues.
First and foremost, once a victim is infected, most of its files will be encrypted and prepended with the ".obfuscated" file extension. For example, image.png will become image.png.obfuscated.
The ransom note is stored in a file named "Read Me.txt," embedded below as a visual reference.
The ransomware's name comes from the email address found in this ransom note that hackers tell victims to reach out for additional information --BigBobRoss@computer4u.com.
Despite using the .obfuscated file extension, the ransomware --written in C++ using QT-- doesn't actually obfuscate files, and actually encrypts them, with an AES-128 ECB algorithm.
Nevertheless, the Avast and Emsisoft BigBobRoss decrypters work around this encryption to help victims recover their files.
With news breaking this week that officials from Jackson County, Georgia paid $400,000 to recover from a Ryuk ransomware infection, it's good to remember the work some companies do to help ransomware victims, when possible. Also, this is probably the best time to set up some offline backups of your most important data, just in case.
More ransomware coverage:
- Georgia county pays a whopping $400,000 to get rid of a ransomware infection
- Ransomware: An executive guide to one of the biggest menaces on the web
- Ransomware warning: GandCrab gang just changed tactics again
- Bitdefender releases third GandCrab ransomware free decrypter in the past year
- Ransomware attack on Israeli users fails miserably due to coding error
- Matrix has slowly evolved into a 'Swiss Army knife' of the ransomware world
- New ransomware demands payment over WeChat Pay in China CNET
- Ransomware: A cheat sheet for professionals TechRepublic