Windows' disk encryption could be easily bypassed in 'seconds'

BitLocker, Microsoft's disk encryption tool, could be trivially bypassed prior to last week's patches, according to recent security research.
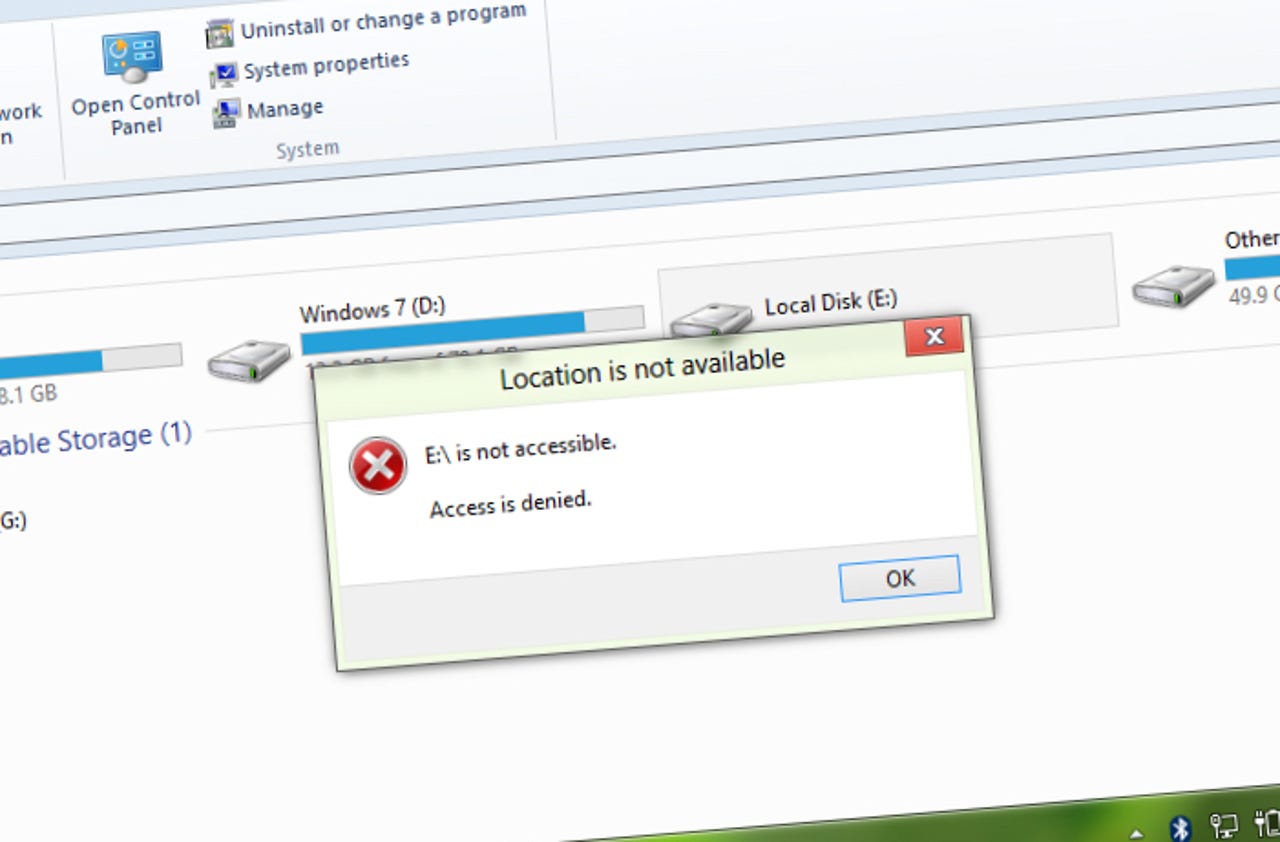
The feature, baked into Windows Vista and later, allows users to lock down their Windows PC with full-disk encryption, making it difficult or near-impossible for an attacker to gain access to data.
THIS IS STILL A THING?
Prior to BitLocker, an attacker could simply boot up a live Linux operating system and tap into a user's files stored on the hard drive. Now, thanks to the full-disk encryption feature, any potential attacker has to let the boot process run to prevent BitLocker's protections kicking in.
One researcher, Ian Haken, a researcher at security firm Synopsys, said in a paper published late last week that the security feature could be bypassed, and "does not require a sophisticated attacker."
PCs connected to domains -- in most cases, enterprise machines -- were most at risk from the flaw. If an attacker took a laptop off the network and the domain server couldn't be reached, the PC falls back to a local username and password stored in its cache.
Haken found a way to change the cached password -- which isn't known to the attacker -- allowing that unauthorized user in, a process that could take "seconds" if the process is automated.
By setting up a fake domain server with identical name, the attacker only had to create a user account with a password created years in the past to trigger a policy-based password change. Once the user changed the password, they could log in to the PC using the password now set in its cache.
Microsoft fixed the flaw last week during its bumper round of monthly security updates.
In its MS15-122 security bulletin on Tuesday the company downplayed the bypass, saying it could only happen if a number of events fall into place.
As the flaw was reported privately, it was not thought to have been exploited in the wild.
"As usual, the most important security procedure is to make sure you have applied all security updates to your effected systems," the researcher wrote.