Bogus movie subtitles could let hackers take over your device, warn security researchers

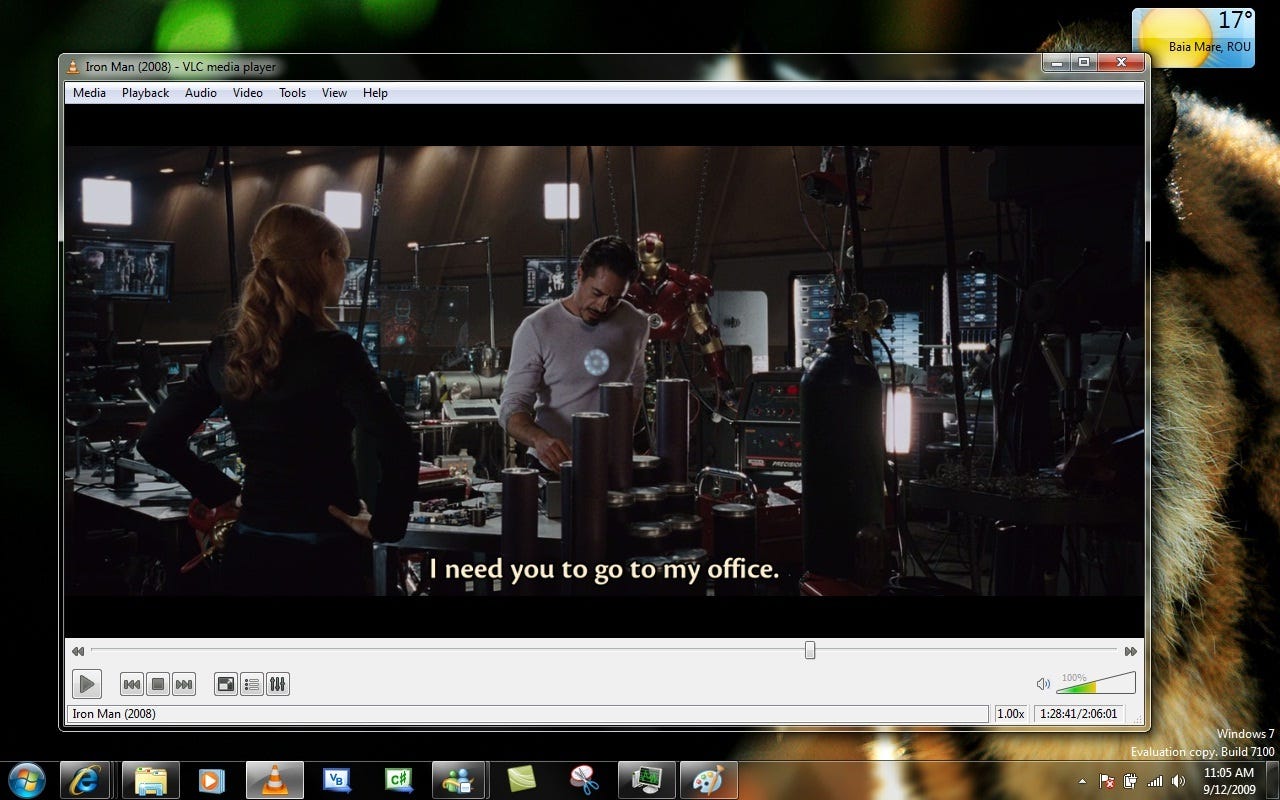
Hackers can manipulate the algorithms which popular video players such as VLC use to download subtitles.
A newly discovered attack could allow hackers to take control of devices by exploiting vulnerabilities in video players when installing subtitles.
A researcher behind the discovery told ZDNet this exploit represents "the most severe category of vulnerability".
Four of the most popular media players --VLC, Kodi (XMB), Popcorn Time, and Stremio -- could all be attacked in this way by exploiting newly discovered vulnerabilities in platforms which are estimated to be used by a combined total of over 200 million users each month.
Vulnerabilities in these four popular media platforms were discovered by cybersecurity researchers at Check Point Software.
By crafting malicious subtitles, hackers could bypass antivirus software and potentially take control of an entire device, the company said.
Subtitles for films and TV shows come in a wide variety of formats and are created by a wide range of authors, making it difficult to fully police what's uploaded and what's contained in software.
"The supply chain for subtitles is complex, with over 25 different subtitle formats in use, all with unique features and capabilities. This fragmented ecosystem, along with limited security, means there are multiple vulnerabilities that could be exploited, making it a hugely attractive target for attackers," said Omri Herscovici, vulnerability research team leader at Check Point.
"We have now discovered malicious subtitles could be created and delivered to millions of devices automatically, bypassing security software and giving the attacker full control of the infected device and the data it holds," he added.
Writers upload subtitles for films and TV shows to online databases, where they're indexed and ranked, a system which in theory should allow the most useful and reliable creations to be presented to the user.
However, researchers have discovered that cyberattackers can manipulate the algorithm behind repositories, enabling the malicious subtitle packages to be automatically downloaded by the media player and to infect devices with very minimal interaction.
"Those repositories index and rank these subtitles and we found a way to manipulate this to get your subtitles ranked as the first," Yaniv Balmas, malware research team leader at Check Point told ZDNet.
"A lot of movie players don't use require interaction at all; they just download the first ranked subtitle and display it to you. You just need to choose the language you want."
"A malicious hacker could craft a malicious subtitle, upload it, and make it the first one -- then everyone is exposed," he added.
"The hackers can run code on the computer -- then they have full control. They can remotely do whatever they want: they can run ransomware, steal files. Whatever scenario you can imagine, it can be done. This is the most severe category of vulnerability out there," said Balmas.
Check Point has informed the developers of VLC, Kodi, Popcorn Time and Stremio about the vulnerabilities following responsible disclosure guidelines.
Since the vulnerabilities were disclosed, all four companies have fixed the reported issues. Stremio and VLC have also released new software versions incorporating this fix.
The biggest step users can take to ensure they aren't vulnerable to being hacked via malicious subtitles for their media player is to ensure they're running the latest version.
READ MORE ON CYBERCRIME
- Ransomware: WannaCry was basic, next time could be much worse
- Intel AMT vulnerability hits business chips from 2008 onwards
- Zero day exploits: The smart person's guide [TechRepublic]
- Dozens of popular iPhone apps vulnerable to man-in-the-middle attacks
- Hackers are attacking Word users with new Microsoft Office zero-day vulnerability