Commonwealth fined $100k for not mandating antivirus software
Despite Commonwealth's brisk reaction which greatly minimized the financial impact of the compromised accounts, the incident took place shortly after a representative contacted the IT Help Desk indicating a malware infection might have taken place without receiving "follow-up" attention:
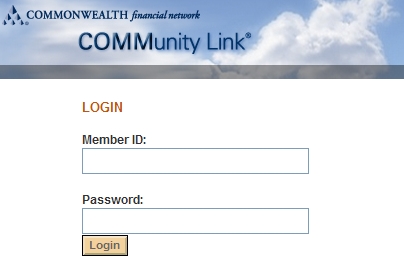
"In or around November 2008, an unauthorized party obtained the login credentials of one of Commonwealth’s registered representatives through the use of a malware/keystroke logger virus. The virus was placed on the registered representative’s computer, which at the time did not have antivirus software properly employed. The intruder ran a search query for the Commonwealth registered representative’s customer accounts with cash balances in excess of a certain amount, generating a list of 368 accounts.
On that same day, the intruder placed or attempted to place eighteen unauthorized purchase orders for the common stock of one publicly-traded company in eight of the 368 customer accounts identified, totaling over $523,000 of unauthorized purchases. Commonwealth immediately canceled the unauthorized purchases and transferred them into its error account, ultimately absorbing a net loss of approximately $8,000, and reported the incident to the Commission staff. Commonwealth also notified the owners of the 368 accounts."
With Commonwealth not offering a DIY online trading platform (Citizens Financial sued for insufficient E-Banking security), which would have allowed them to forward the responsibility for a potential compromise through a "No security software, no E-banking fraud claims for you" contract agreement, lacking security E-banking best practices in general, and actual enforcement of them on the computers of their representatives has been exposing their client's financial assets in the most insecure way possible - having them rely on the common sense security practices whose enforcement they took for granted.
Would the presence of antivirus software have made any difference considering the tactics applied by cybercriminals successfully bypassing signatures-based scanning? Partly, since it would have at least increased the probability of detection, and mitigated the potential of infection with known malware.
The solution? E-banking on Live CD or through alternative operating systems in order to bypass a huge percentage of crimeware and the way it currently works, has always been an alternative. However, until financial institutions themselves start building awareness on the concept, and admit that the current E-banking security process is not just flawed, but has been systematically exploited for years, the concept would remain an enemy to the most advantageous of E-banking's features - convenience that millions of users are used to.