Enterprises need to change passwords following ClickStudios, Passwordstate attack

ClickStudios has told its global customer base to start changing passwords following a breach that resulted in a supply chain attack.
The Australian software company, which makes the Passwordstate password manager, suffered a breach between April 20 and April 22. CSIS Security Group, which dealt with the breach, posted the attack details. ClickStudios outlined the attack in an advisory. The company said:
Initial analysis indicates that a bad actor using sophisticated techniques compromised the In-Place Upgrade functionality. The initial compromise was made to the upgrade director located on Click Studios website www.clickstudios.com.au. The upgrade director points the In-Place Upgrade to the appropriate version of software located on the Content Distribution Network. The compromise existed for approximately 28 hours before it was closed down. Only customers that performed In-Place Upgrades between the times stated above are believed to be affected. Manual Upgrades of Passwordstate are not compromised. Affected customers password records may have been harvested.
The supply chain attack was initiated via an update of the Passwordstate app.
In a post, CSIS said its researchers found the attack during an investigation. "As recommended by ClickStudios, if you are using Passwordstate, please reset all the stored passwords, and especially VPNs, Firewall, Switches, local accounts or any server passwords etc," said CSIS, which dubbed this incident/malware "Moserpass".
ClickStudios' letter to customers was posted on Twitter via Polish news site Niebezpiecznik (via The Record).
Aside from the obvious hassle of changing enterprise passwords on Friday and the weekend, Passwordstate touches multiple key areas of a company including:
- Auditioning and compliance reporting.
- Local admin accounts on your network.
- Active Directory.
- Credentials management and remote sessions.
- API integration.
- Access control.
- And two-factor authentication among others.
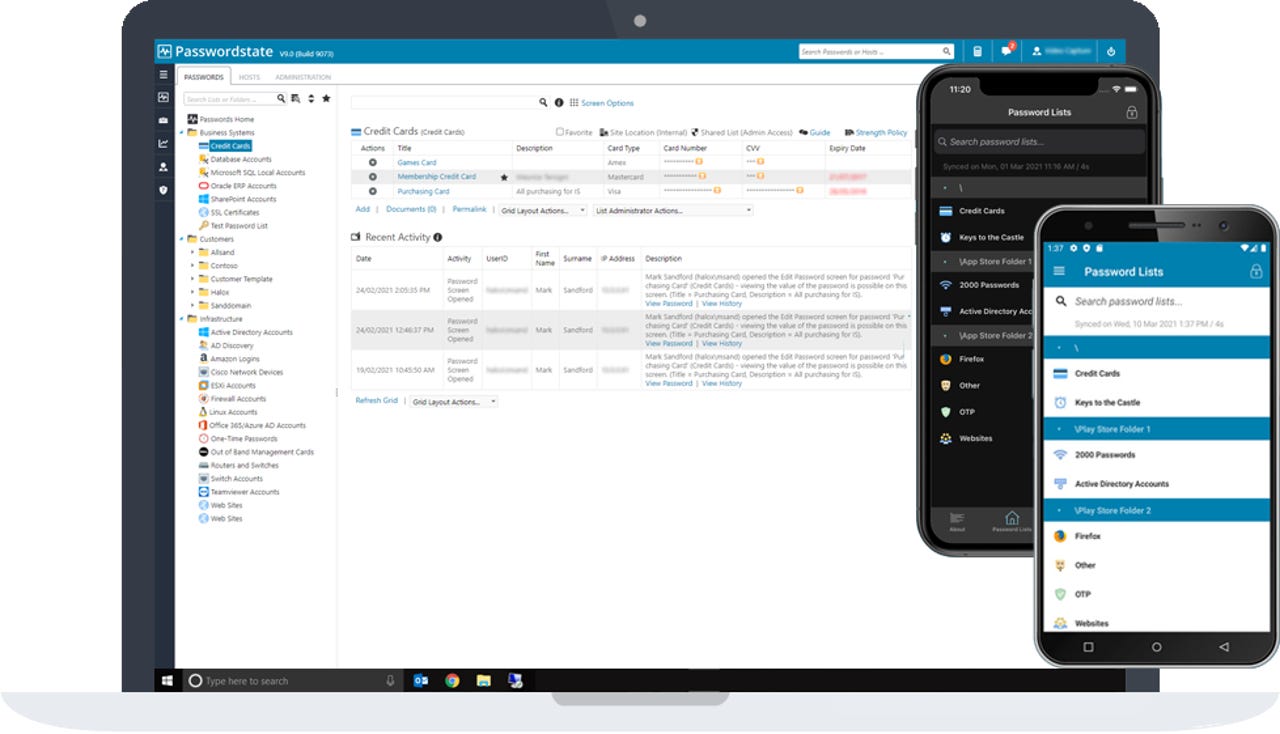
Passwordstate from ClickStudios
Add it up and Passwordstate made for a nice target because it has multiple touch points in an enterprise.
As for the remediation for Passwordstate customers, ClickStudios outlined the following:
Customers have been advised to check the file size of moserware.secretsplitter.dll located in their c:\inetpub\passwordstate\bin\ directory. If the file size is 65kb then they are likely to have been affected.
They are requested to contact Click Studios with a directory listing of c:\inetpub\passwordstate\bin output to a file called PasswordstateBin.txt and send this to Click Studios Technical Support.
Affected customers are then advised by Click Studios Technical Support via email to;
1. Download the advised hotfix file
2. Use PowerShell to confirm the checksum of the hotfix file matches the details supplied
3. Stop the Passwordstate Service and Internet Information Server
4. Extract the hotfix to the specified folder
5. Restart the Passwordstate Service, and Internet Information Server
Once this is done it is important that customers commence resetting all Passwords contained within Passwordstate. These may have been posted to the bad actors CDN network. Click Studios recommends prioritizing resets based on the following;
1. All credentials for externally facing systems, i.e., Firewalls, VPN, external websites etc.
2. All credentials for internal infrastructure, i.e., Switches, Storage Systems, Local Accounts
3. All remaining credentials stored in Passwordstate