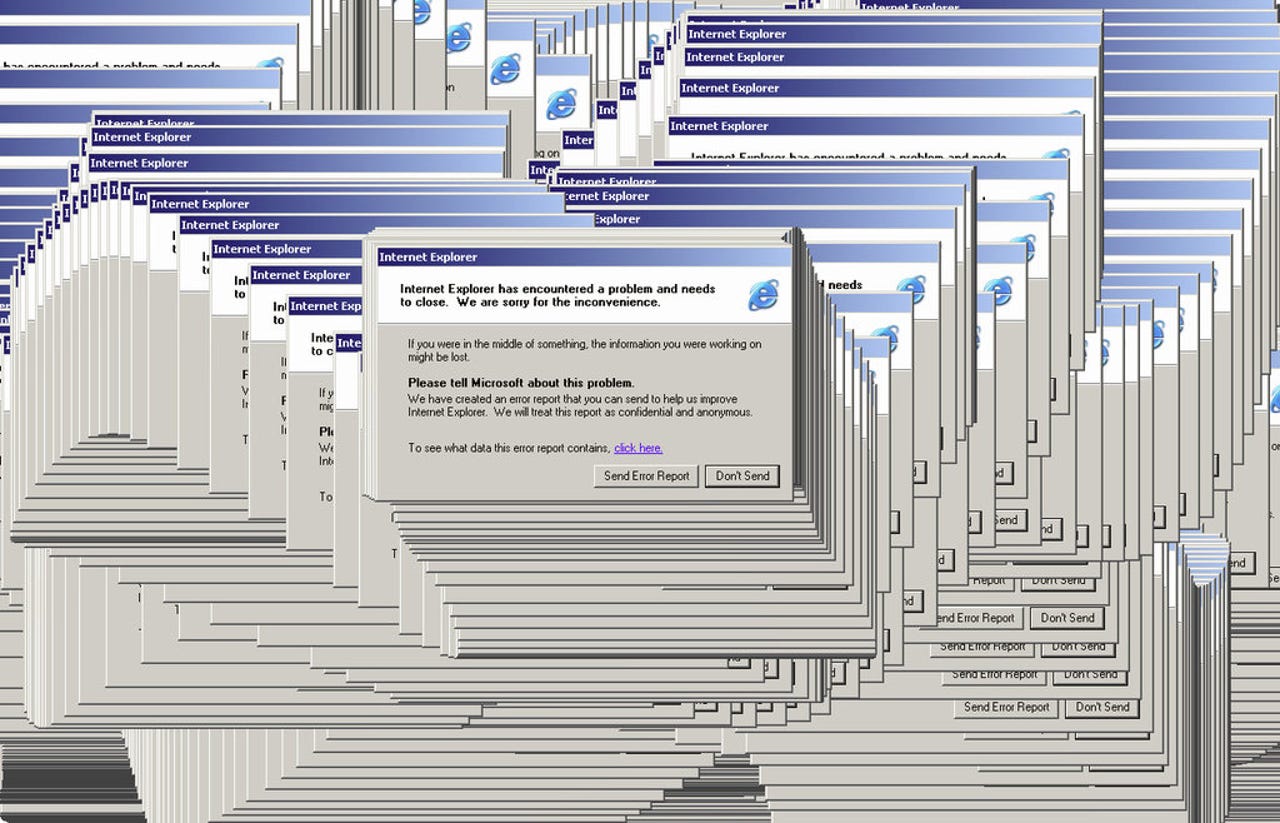
Exploit code released for unpatched Internet Explorer flaw

Researchers at computer giant HP have published exploit code that can be used to attack a weakness in Internet Explorer, after Microsoft refused to issue a patch.
In a blog post, Dustin Childs, HP senior security content developer, said the move to publish the flaw was not out of "spite or malice," but was in accordance with its own disclosure policy.
"Microsoft confirmed in correspondence with us they do not plan to take action from this research, we felt the necessity of providing this information to the public," said Childs. That's in spite of Microsoft earlier this year awarding the team $125,000 -- which was later donated -- for discovering the flaw.
The bug allows an attacker to bypass Address Space Layout Randomization (ASLR), which acts as one of the many lines of defense in the popular browser. But the flaw only affects 32-bit systems, which the HP researchers said still affects millions of systems, even if many systems nowadays are 64-bit.
Childs, who used to work at Microsoft, said the statement was "technically correct," but chastised the company's decision not to patch the flaw.
In response, the team released a proof-of-concept exploit for Windows 7 and Windows 8.1.
"We disagree with that opinion and are releasing the PoC information to the community in the belief that concerned users should be as fully informed as possible in order to take whatever measures they find appropriate for their own installations."
The researchers justified the move, arguing that in order to effectively protect a system they must "fully understand the threat."
"We feel it's important to let everyone know about the threat so that they could better understand the actual risk to their network," wrote Childs.
We've reached out to Microsoft but did not hear back at the time of writing.