How one hacker exposed thousands of insecure desktops that anyone can remotely view


(Image: file photo)
Imagine being given the keys to the internet. One minute you could be looking at a building's air conditioning panel, a pharmacist's inventory, and a Windows programmer's console, and the next minute it's a school administrator's email inbox, and a touch-screen toilet customer satisfaction monitor (which, sadly isn't a joke).
Give it time, and you'll likely land on something more sinister, like the desktop belonging to a receptionist in a pediatrician's office, and you're looking at their screen which is packed with patients' names, addresses, dates of birth, and parents' phone numbers.
It's a whole new meaning to the "open" internet, and one you wouldn't want to be on the wrong side of.
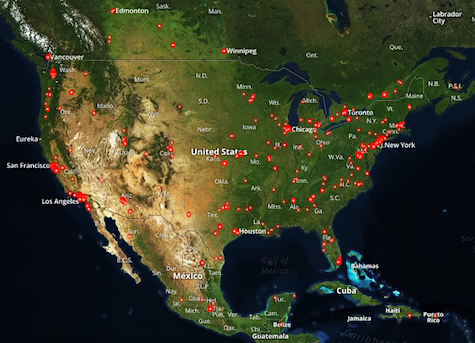
A map from Shodan.io showing where vulnerable VNC servers are located. (Image credit: ZDNet)
It's not only possible, but it's been happening for a while. Thousands of screenshots have been collected and uploaded to a website called VNC Roulette, which shows a snapshot in time of a random internet-connected desktop.
All these desktops have something in common: they're running VNC, an open-source software that allows users to remotely access and control a desktop from anywhere else in the world. But if VNC is set up without a password, anyone can scan the web and access an unsecured computer.
One hacker set out to see how many insecure computers were out there. Revolver, the moniker he goes by (and not his real name), is a Morocco-based grey-hat hacker who got more than he bargained for.
"This is deep f**k," he said in a message on Monday. "We had access to sysadmins boxes, big machines with sensitive data. There is no security at all."
Revolver created a script that cycled through IP addresses and select ports on his own server, which tries to connect to unsecured servers through a web-based VNC viewer. If the script finds an available connection without any authentication, it will connect and grab a screenshot, otherwise the script will kill the session and move to a different IP address.
After thousands of successful connections, he now has about 23 gigabytes of screenshots saved. Not all have been posted to VNC Roulette -- some were taken down so he won't "get in trouble," he said.
Revolver quickly realized he had thousands of desktops -- Windows, Macs, and even Linux machines -- and hundreds of screenshots of potentially highly-sensitive supervisory control and data acquisition (SCADA) systems, which are typically used in industrial facilities.
He explained that his unfettered access to thousands of desktops is "not a configuration issue" or a flaw or vulnerability in how VNC is designed. It's the result of users' utter disregard for using a basic security setting.
"Once you install a VNC server, it will pop a f**king big interface or message saying you should make a password for security. And [most people] don't make that password," he said.
Perhaps surprisingly, collecting screenshots of thousands of remotely-accessible desktops isn't a new idea, and it isn't difficult for the low-grade hacker to do, either.
Shodan.io, a search engine for internet-connected things, brings internet webcams and open-port servers and other computers onto a single page. It's criticized by some, but others have said it's the "absolute example" of what can happen when devices with poor security enter our daily lives.
One cursory search of a common VNC port (5900 or 5901) can throw back hundreds if not thousands of different screenshots -- and you can map them by geo-location.
Revolver would "start a f**king internet revolution" behind the people who leave their VNC-enabled machines unsecured. The risks to those systems and the after-effects of causing damage, he said, are palpable.
All it takes, he said, is to "focus on the SCADA systems, and [you can] start a new war against a country."