Hackers steal card data from 201 online campus stores from Canada and the US

A group of hackers has planted malicious JavaScript code that steals payment card details inside the e-commerce system used by colleges and universities in Canada and the US.
The malicious code was found on 201 online stores that were catering to 176 colleges and universities in the US and 21 in Canada, cyber-security Trend Micro said in a report released on Friday.
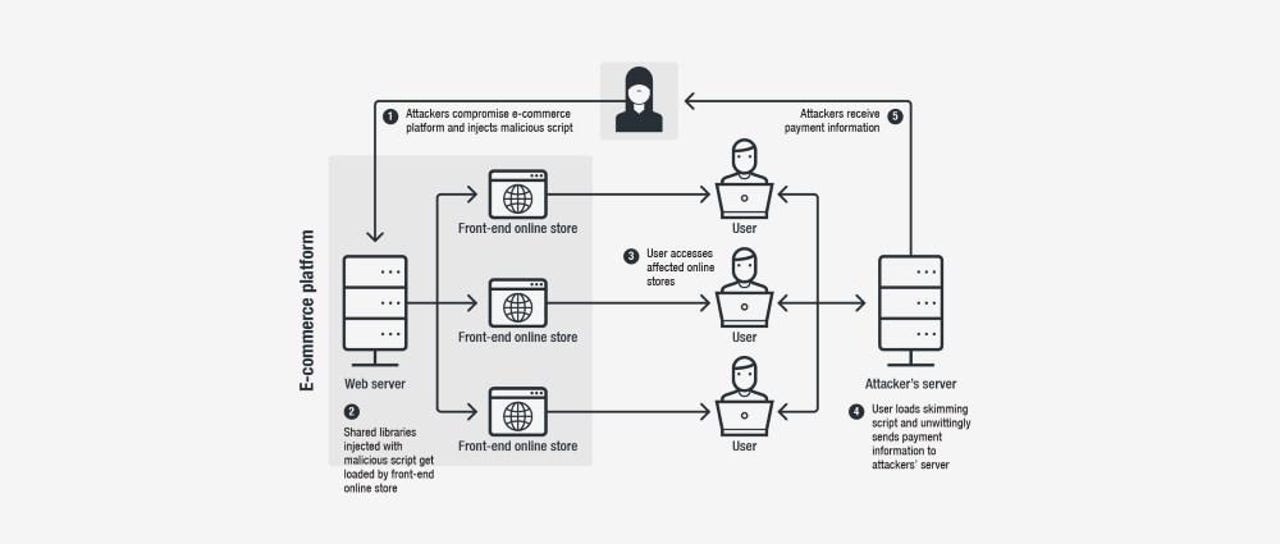
The attack is what security researchers call a Magecart attack --which consists of hackers placing malicious JavaScript code on the checkout and payment pages of online stores to record payment card data, which they later upload to their servers, and re-sell on underground cybercrime forums.
Hackers breached PrismRBS
This particular Magecart attack was detected on April 14, according to Trend Micro, and impacted PrismRBS, the company behind PrismWeb, an e-commerce platform (a-la Shopify) sold to colleges and universities in North America.
Trend Micro said hackers breached PrismRBS and modified the PrismWeb platform to include a malicious JavaScript file that got loaded on all active PrismWeb deployments.
The script, modeled to look like a file part of the Google Analytics service, was active until April 26, when Trend Micro notified the vendor, which took action to remove the card skimmer code.
In a statement released to Trend Micro, PrismRBS formally acknowledged the hack and said it was notifying impacted colleges, as well as engaging with an external IT forensic firm to look deeper into the incident.
Magecart attacks expanding
There have been quite a few hacker groups that have started carrying out Magecart (JS card skimming, JS card sniffing) attacks over the past few months, and the number is now in the tens.
According to Trend Micro, this group's infrastructure did not have any overlap with any known Magecart cybercrime groups.
Yonathan Klijnsma, lead threat researcher at RiskIQ, and one of the people tracking Magecart groups since their first attacks told ZDNet that one of the reasons security firms are now having a hard time tracking individual groups is because many are buying and using the same Magecart skimming kits from hacking forums, making attacks look more and more generic.
Earlier this week, RiskIQ released a report warning companies that Magecart attacks are now spreading to other e-commerce platforms, and are not taking place only on Magento-powered stores, as they have initially. Other e-commerce platforms that are being targeted include OpenCart, OSCommerce, WooCommerce, and Shopify.
Another rising trend --and which also took place here, in the case of the PrismRBS hack-- is that Magecart groups don't attack the stores/companies directly, but go after one of their components, in a classic supply-chain attack.
In this case, hackers targeted the PrismWeb e-commerce platform, but in the past, other Magecart groups have also gone after providers of chat and support widgets that are sometimes loaded on e-commerce stores.
Cybercrime and malware, 2019 predictions
More data breach coverage:
- Amnesty International says 'state sponsored' hackers targeted Hong Kong base
- FTC gives two companies a slap on the wrist after appalling hacks
- Microsoft discloses security breach that impacted some Outlook accounts
- Docker Hub hack exposed data of 190,000 users
- Facebook admits to storing plaintext passwords for millions of Instagram users
- Cartoon Network websites hacked to show Arabic memes, male stripper videos
- Facebook passwords by the hundreds of millions sat exposed in plain text CNET
- Facebook data privacy scandal: A cheat sheet TechRepublic