Home Affairs proposes cyber regulations and legal immunities to respond to threats

The Department of Home Affairs has fleshed out some of the initiatives from the recently released 2020 Cyber Security Strategy in a discussion paper released on Wednesday.
Skirting what the government itself will do to lift its cyber capability, the paper instead focuses on critical infrastructure across the economy, explicitly calling out a list of sectors including: Banking and finance, communications, data and cloud operators, defence industry, education and research, energy, food and grocery, health, space, transport, and water.
Among the operators deemed to have critical infrastructure, there will be a subset that will be regulated with a sector-specific positive security obligation that has to be met, and an even larger set of cyber requirements for "entities running systems of national significance". Home Affairs said it would work with industry to map out which entities should be categorised where.
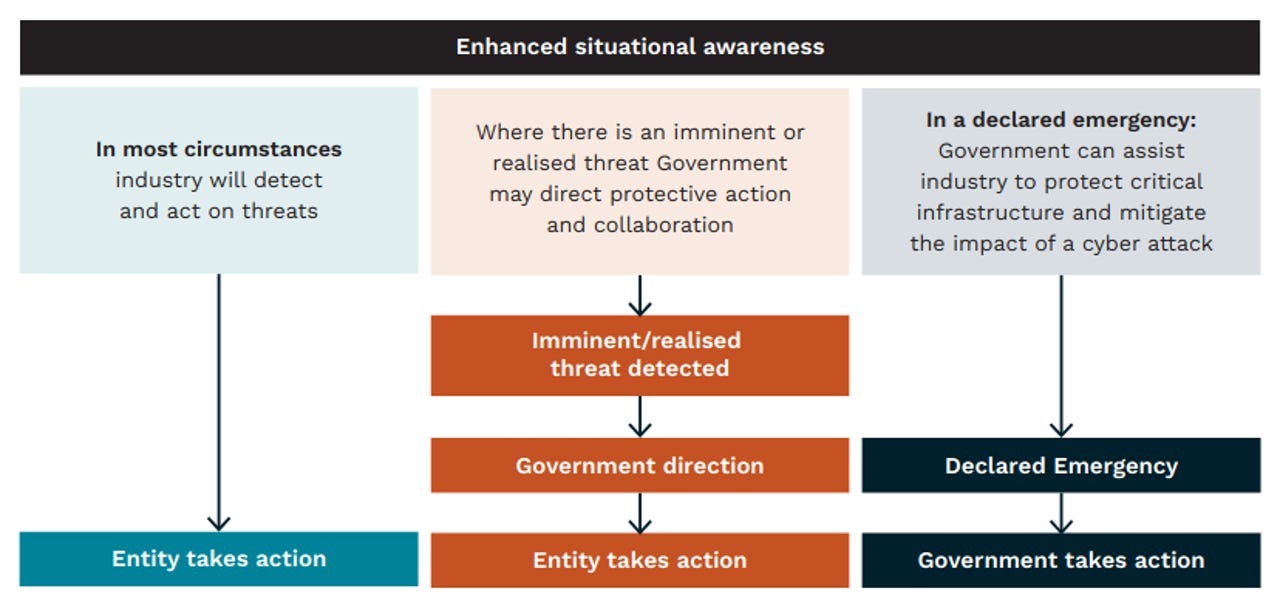
All critical infrastructure entities will have the ability to call on the government to help respond to attacks on Australian systems.
"The primary objective of the proposed enhanced framework is to protect Australia's critical infrastructure from all hazards, including the dynamic and potentially catastrophic cascading threats enabled by cyber attacks," the paper states.
Under the positive security obligation, companies will need to "take an all-hazards approach" to identifying and understanding risks, including in their supply chain. They will also have to mitigate those risks, have "robust procedures" in place to recover as quickly as possible from an attack, and have tested its compliance.
Key to this approach will be sector regulators who will be taking on cyber responsibilities. Home Affairs said it does not want to duplicate existing regulatory frameworks as regulators in sectors such as banking, finance, aviation, and communications are "already equipped" to supervise and assist.
"We recognise that there will be a regulatory impost in delivering these reforms," the department said.
"We will work with critical infrastructure entities to ensure that these reforms are developed and implemented in a manner that secures appropriate outcomes without imposing unnecessary or disproportionate regulatory burden, in accordance with guidance from the Department of the Prime Minister and Cabinet's Office of Best Practice Regulation."
Those under regulation will be responsible for "engaging with the regulator" to see that risks are identified and mitigations proportionate to the risk are in place "while also considering the business, societal, and economic impacts".
Regulators will be able to issue "reasonable requests" for information, access to inspect, and audit powers; issue security notices that entities "would need to take into account and evidence in their reporting"; provide guidance on how entities can be compliant; issue direction in case of "significant national security concerns that cannot be addressed through other means"; and also have the ability to issue fines and penalties.
As outlined in the strategy released last week, the government is looking to establish a threat-sharing platform between government and industry. Dubbed in the discussion paper as a "near real-time national threat picture", Home Affairs said that information be sourced from industry, incident reporting, open-source information, government intelligence, and international feeds.
See also: The disappointment of Australia's new cybersecurity strategy
Initially, the government is looking to ask for information from entities, but this will be scaled up to be prescriptive and mandatory.
"In the longer term, owners and operators of systems of national significance will be obligated (under amendments to the Act) to provide information about networks and systems to contribute to this threat picture if requested," the paper said.
"When a request is issued, it will include the format the information is required in (up to and including near real-time), as well as a specified timeframe to work with the government to provide the information. At present, we do not anticipate that all owners and operators of systems of national significance will be requested to provide such information."
Systems of national significance will further have a number of preparatory activities conducted, ranging from independent cyber assessments, vulnerability scanning, and the government working with entities to "detect and isolate threats that have evaded existing security solutions".
Additionally, Home Affairs wants the creation of playbooks to respond to certain attack scenarios.
"This will provide owners and operators of systems of national significance with important information on 'what to do' and 'who to call' to keep their business (and customers) safe when facing a cyber attack," the paper said.
"Development of these playbooks will require partnership between government and individual entities to ensure arrangements are tailored to each entity's needs and can be activated on a 24/7 basis. This will provide certainty to owners and operators of systems of national significance by outlining roles and responsibilities in the event of a significant incident, especially when a cyber attack is beyond their capability."
Should an attack on critical infrastructure occur, Home Affairs said government could be involved, and should that occur, it will provide "immunities to entities to conduct mitigations that may otherwise open them up to a civil suit".
"Critical infrastructure entities may face situations where there is an imminent cyber threat or incident that could significantly impact Australia's economy, security, or sovereignty, and the threat is within their capacity to address," Home Affairs said.
"In these cases, we propose that government be able to provide reasonable, proportionate and time-sensitive directions to entities to ensure action is taken to minimise its impact. Entities may also be able to request that government make such a direction, providing them with the legal authority to conduct any necessary action.
"Entities must be empowered to take necessary, preventative and mitigating action against significant threats. Government recognises that entities require appropriate immunities to ensure they are not limited by concerns of legal redress for simply protecting their business and the community."
The paper explicitly ruled out the option for entities to retaliate against attackers.
"Under no circumstances will entities be directed or authorised to take actions against the perpetrator (including 'hack backs')," it said.
The paper suggested a national cyber alerting system like the National Terrorism Threat Advisory System could be created, and that a two-way secondment program between industry and government be established to deepen links.
The closing date for submissions is 5pm AEDT September 16, the paper said, however, daylight savings does not begin until October 4.
Related Coverage
- New Australian cybersecurity strategy will see Canberra get offensive
- The disappointment of Australia's new cybersecurity strategy
- Singapore, Australia formalise digital economy pact
- Atlassian says encryption-busting law has damaged Australia's tech reputation
- Committee hits roadblock in probing Commonwealth cybersecurity performance
- New South Wales to implement sector-wide cybersecurity strategy