Home Affairs report reveals deeper problems with Australia's encryption laws

Australian law enforcement agencies used their controversial new powers under the Telecommunications and Other Legislation Amendment (Assistance and Access) Act 2018 just seven times in seven months, and all were voluntary Technical Assistance Requests (TARs).
That's five times by the Australian Federal Police (AFP) and twice by the NSW Police from the time the laws came into effect in early December 2018 through to the end of June 2019. No other cops chose to play.
After all, cops hate paperwork. If direct observation and interviews don't produce enough evidence for a prosecution, then stored telco metadata might. That's an internal request, and it might well deliver enough to seal the deal.
During a murder investigation, several hundred people's metadata might be pulled depending on the case. The vast majority of those people would then immediately be eliminated from the inquiry.
Far fewer individuals actually move to the stage of having their communications intercepted. That requires reasonable suspicion for a warrant to be issued. And for only some of those intercepted communications would the cops need external assistance to access the contents.
That's not a lot, especially when you set it against the 3,561 interception warrants issued over the full year, the 1,252 stored communications warrants, or the 295,691 authorisations for access to retained telecommunications data, or "metadata".
So all this boils down to is seven TARs being used across six cybercrime offences, two so-called "organised offences", five telecommunications offences, one theft, one homicide, and one illicit drug offence. That seems reasonable to me.
While we don't know how many times the spooks used the encryption laws, then again, we never do. Based on the law enforcement figures then, your writer has trouble seeing these first few TARs as being the main problem.
That's not to say there aren't still problems with the encryption laws however, as ZDNet has continued to report.
The definitions are unclear, and although Labor hopes to fix that that in the next session of Parliament, there are further significant concerns.
And there's still confusion over whether employees can be dragooned in secret to assist.
But far more worrying, I think, is the number of telecommunications interception warrants that are approved not by judges, but by members of the Administrative Appeals Tribunal (AAT).
As The Saturday Paper reported a year ago, more than three-quarters of the 3,524 interception warrants obtained in 2017-2018 were authorised by AAT members, not by judges.
In recent years, AAT members have increasingly been political appointees. Some of them have no legal qualifications.
"The Saturday Paper asked various agencies why they chose the AAT over other authorities. Some suggested the skew towards the AAT simply reflected the availability of the various authorities to hear warrant applications, with some AAT members more accessible at short notice than a judge," they wrote.
"What is not clear is whether AAT members are also considered more likely to readily approve the applications than judges."
It's no different this year.
The AFP obtained 557 interception warrants through AAT members, compared with 77 through the various species of Federal Court judges.
NSW Police obtained 1,512 interception warrants through AAT members, compared with 101 through Federal Circuit Court Judges. That's 94% of them.
Across all law enforcement agencies, 76% of the interception warrants were obtained through AAT members.
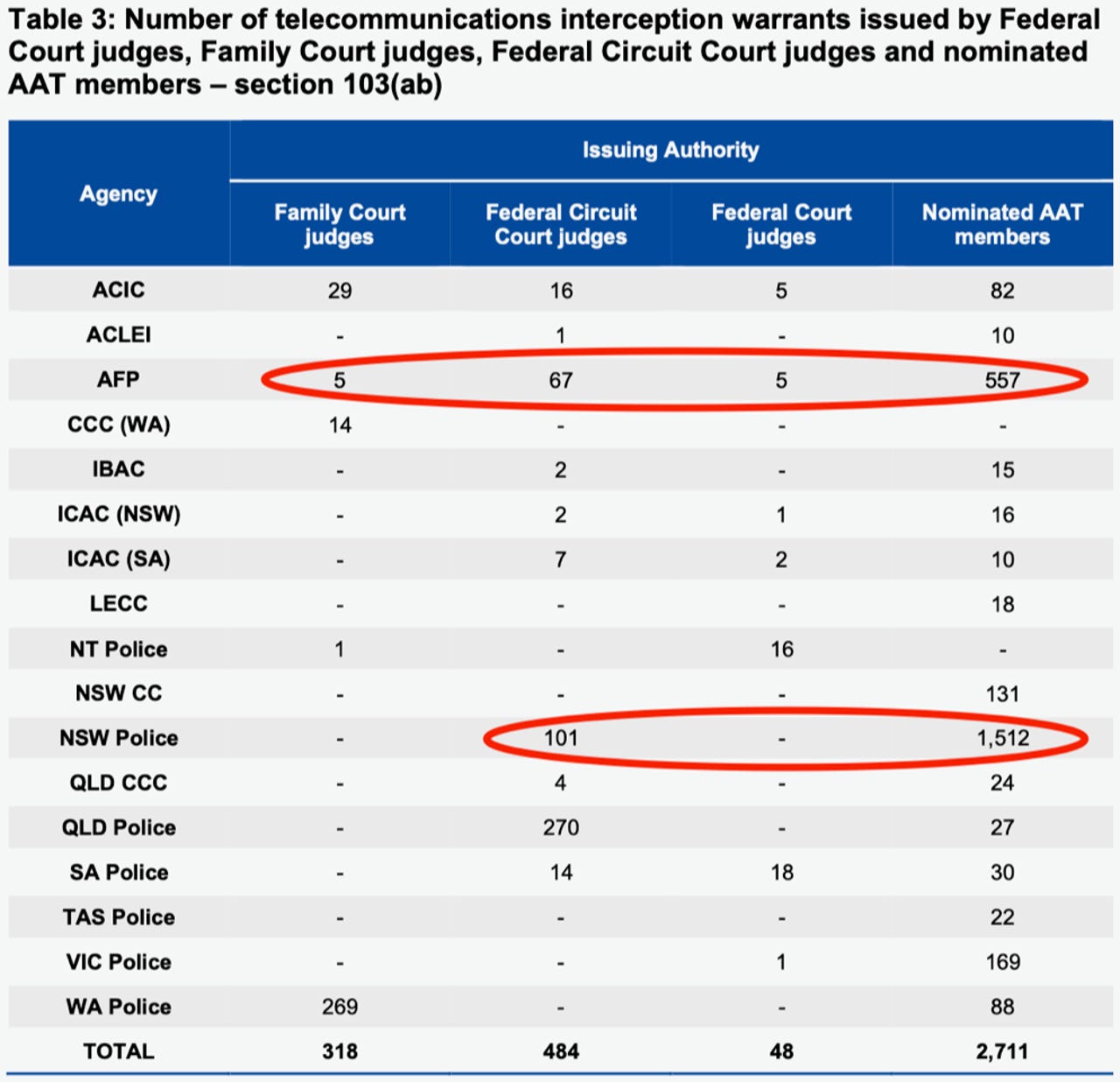
Issuing authorities for telecommunications interception warrants 2018-2019.
In addition to TARS, the Assistance and Act also creates Technical Assistance Notices (TANs) and Technical Capability Notices (TCNs), which are compulsory notices to compel communications providers to use or create a new interception capability, respectively.
A TCN can only be issued by the Attorney-General with the approval of the Minister for Communications, but the Act has been widely criticised for allowing agencies themselves to issue a TAR or TAN.
A TAR or TAN only requires underlying telecommunications interception warrants for the communications in question.
And what these figures show is that the process will more than likely lead to communications being accessed without any independent advanced scrutiny by someone who's actually trained in the law or experienced in jurisprudence.
Is that good enough? I think not.
With only the cops and spooks, government ministers, and political appointees in the loop, well, history shows us how quickly that can turn into something quite oppressive.
The Assistance and Access Act will, however, continue to be scrutinised by two inquiries this year.
The Independent National Security Legislation Monitor (INSLM) is due to report by June 30. That analysis will feed into the ongoing review by the Parliamentary Joint Committee on Intelligence and Security (PJCIS), which is due to report by September 30.
The PJCIS is also due to report somewhat sooner, on the effectiveness of the mandatory telecommunications data retention regime, by April 30.
Related Coverage
AFP and NSW Police used Australia's encryption laws seven times in 2018-19
Seven Technical Assistance Requests made with no Technical Assistance Notices or Technical Capability Notices issued.
End-to-end encryption means Huawei bans are about availability, not interception
Former Prime Minister who brought in Australia's anti-encyption laws says the technology can prevent potential tapping by telco equipment manufacturers.
Labor says it will fix encryption laws it voted for last year
Better late than never for agreeing to judicial authorisation, but legislation is unlikely to pass the House of Representatives.
Biometric ID a worry but still acceptable to Australians: AIC
Australians are concerned about the risks of biometric identification, but still find its use acceptable in a wide range of scenarios.
Twitter bots and trolls promote conspiracy theories about Australian bushfires
Research from QUT shows that 'some kind of a disinformation campaign' is pushing the Twitter hashtag #ArsonEmergency. There is no arson emergency.