Jaff ransomware demanding $4,000 to unlock your files? Now you can get them back for free

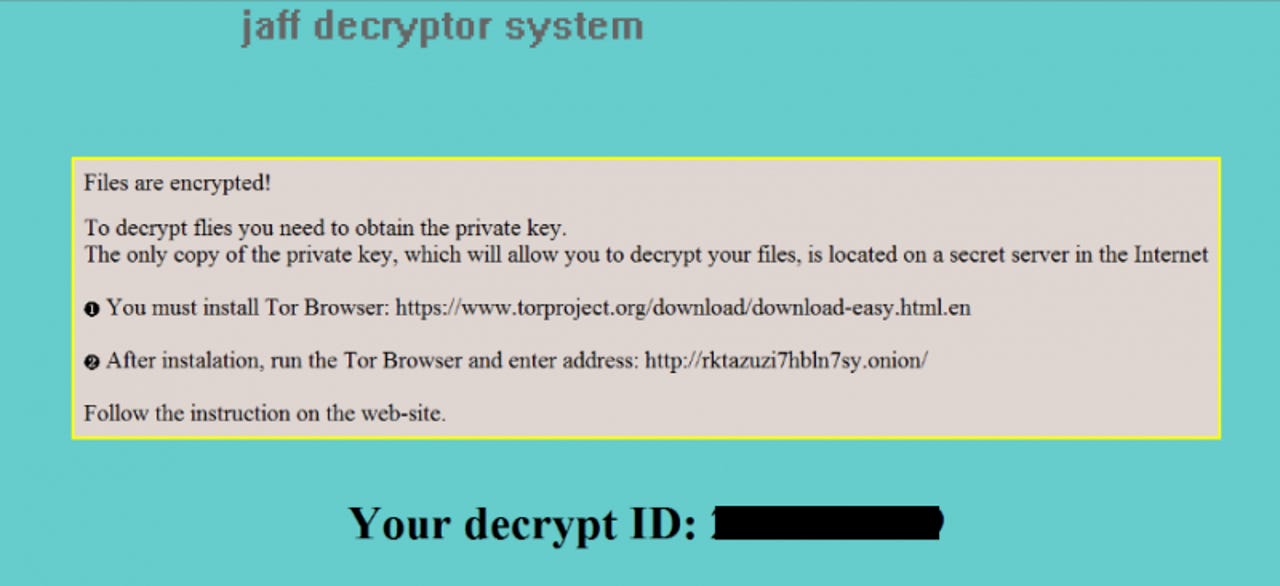
Jaff ransomware demands thousands in exchange for unlocking files.
Victims of a form of ransomware that demands a huge payment to unlock files can now do so for free, thanks to a newly released decryption tool.
that exploits a vulnerability in its malicious code.
Jaff ransomware appeared in May, harnessing the power of the infamous Necurs botnet -- previously used to distribute Locky -- to indiscriminately target millions of PCs around the world.
One particular element that marked Jaff out from other forms of ransomware is that it demands a much higher fee for releasing encrypted files, demanding 1.79 Bitcoins, a figure currently equivalent to almost $4,000, and far more than the $500 to $1000 requested by most ransomware campaigns.
While it's not certain who is behind Jaff, researchers have linked it to a much wider cybercrime operation that deals in stolen bank details and hacked accounts from online stores, including PayPal, eBay and Amazon and more.
As is the case with many other ransomware campaigns, the payload is delivered via a malicious attachment in a phishing email, which encrypts files once the compromised PDF is opened.
However, now those who find themselves infected with Jaff can decrypt their files for free, no matter which version of the ransomware they've been compromised by.
"We have found a vulnerability in Jaff's code for all the variants to date. Thanks to this, it is now possible to recover users' files (encrypted with the .jaff, .wlu, or .sVn extensions) for free," Kaspersky Lab's Fedor Sinitsyn said.
Victims simply need to download the RakhniDecryptor tool from Kapersky Lab and run it to decrypt all files affected by Jaff, which has mostly infected victims in China, India, Russia, Egypt and Germany.
As part of No More Ransom - a joint initiative by law enforcement and cybersecurity firms - Kaspersky Lab has previously helped to release decryption tools for various other families of ransomware, including Wildfire, Coinvault, Rannoh, Rakhni and Polyglot.
Ransomware has become one of the biggest menaces on the web: this ZDNet guide contains everything you need to know about it: how it started, why it's booming, how to protect against it, and what to do if your PC suffers an attack.
READ MORE ON CYBERCRIME
- Ransomware: The smart person's guide [TechRepublic]
- After WannaCry, ransomware will get worse before it gets better
- Europol, Intel and Kaspersky team up to crack down on ransomware [CNET]
- Tell Bart and other ransomware families to 'Eat my shorts' with new, free decryption tools
- Hit by ransomware? No More Ransom portal adds 32 more free decryption tools to help you