Metel APT hacking group rolls back ATM transactions to dupe banks

TENERIFE, SPAIN: The banking sector is a target for cybercriminals looking to cash in on the industry's valuable assets and data deposits -- and as cybersecurity increases, so do novel ways used by hackers to swindle companies through digital means.
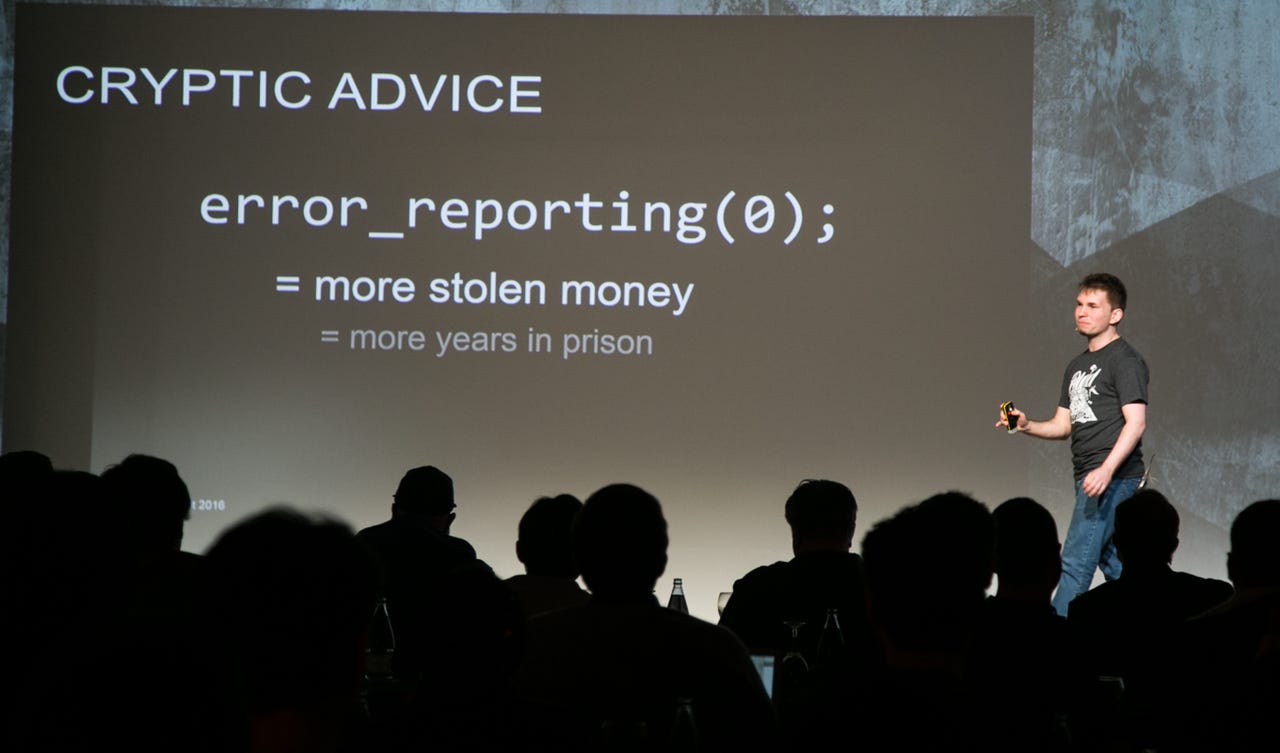
Speaking at the Kaspersky Security Analyst Summit held in Tenerife, Spain, Sergey Golovanov, Principal Security Researcher at Global Research & Analysis at Kaspersky Lab and Vladislav Roskov told attendees on Monday that while cybercriminals are adopting new tactics to circumvent tougher controls and defenses, advanced persistent threats (APTs) remain a critical problem.
To make matters worse for banks and financial institutions across the globe, cybercriminals are now adopting both the tools and methods used by advanced, state-sponsored APT groups for their own ends.
Carbanak is one such threat. First discovered in 2015, the malware struck banks in over 30 countries over two years, granting attackers the opportunity to steal at least $1 billion -- often due to the poor network configuration and security of ATM machines.
The APT has now returned in a new-and-improved form, Carbanak 2.0. The new APT not only targets banks, but also the budget and accounting departments of victims, which may have smaller investment rates in security and defense and therefore barriers which are easier to crack.
In one example of a recent and somewhat outrageous attack launched by the Carbanak 2.0 APT group, a financial institution was compromised in order for the ownership credentials of a large company to be compromised. The group was able to change these details, name a mule as a shareholder of the company and gain access to additional ID data as the consequence.
A recently discovered copycat group dubbed Metel targets financial institutions through APT-style spying missions and custom malware -- along with "legitimate software and new, innovative schemes to cash out," according to Kaspersky. A new tactic, particularly of note, is the ability to gain control over bank machines which have access to transactions -- such as support center PCs -- in order to automate the rollback of ATM transactions.
This scheme is particularly clever as rollbacks help to cover the tracks and patterns of fraudulent transactions conducted by the hacking group. Once a PC has been compromised, pushing through rollbacks on a compromised machine ensures that debit card balances remain the same no matter how many ATM withdrawals have taken place.
To date, the researchers say the group has been detected "driving around cities in Russia at night and emptying ATM machines belonging to a number of banks," and they often repeat the process using the same debit cards issued by a victim bank.
In a short period of time, Metel was able to cash out "millions of dollars," according to Golovanov, through the use of only a "magic card number" and an accomplice clicking away to wipe transaction data.
Before heading into the sunset with a proverbial wad of stolen cash, Metel first needs to compromise a bank's support systems. The group undertakes this task through spear phishing emails which are tailored specifically for the target bank. These malicious emails are loaded with virus-bearing attachments that target vulnerabilities in browsers through the Niteris exploit pack.
Metel contains at least 30 known modules, according to Roskov, and includes keyloggers, browser injection tools, form grabbers and a remote access and control installer.
Once a system has been compromised, the hacking group uses a mixture of legitimate and underground penetration testing tools to source flaws, hijack local domain controllers and gain access to systems which deal with payment processing.
Security
Metel remains active in Russia. While the investigation into Metel's activities is ongoing, however, the security researchers believe there is evidence the infection may be "much more widespread."
"Nowadays, the active phase of a cyberattack is becoming shorter," Golovanov said. "When the attackers become skilled in a particular operation, it takes them just days or a week to take what they want and run."
Another cybercriminal group exposed by Kaspersky, known as GCMAN, uses stealth as its signature. According to the security researchers, GCMAN does not rely purely on malware, but often uses only legitimate penetration testing tools to poke through an organization's defenses. The legitimate Putty, VNC, and Meterpreter security tools have been used to move through a network until machines are discovered which could be used to transfer cash to e-currency services without alerting other businesses.
In one attack, the cybercriminals squatted on a network for a year and six months before making their move. Money was then transferred in $200 sums, which is the limit for anonymous payments in Russia. Every minute, the compromised system fired off a malicious script which transferred additional funds to an e-currency account owned by a mule -- and as they were sent directly, did not appear on the bank's internal systems and avoided both detection and shutdown.
Golovanov commented:
"The Carbanak gang was just the first of many: cybercriminals now learn fast how to use new techniques in their operations, and we see more of them shifting from attacking users to attacking banks directly.
Their logic is simple: that's where the money is. [...] In the case of Carbanak, we advise protecting the database that contains information about the owners of accounts, not just their balances."
Disclaimer: Kaspersky Labs sponsored the trip to the summit in Tenerife, Spain.