Microsoft: Here's how to fix the Group Policy mess caused by our security update

A late June Microsoft security update for Group Policy ended up breaking Group Policy for more than a few Microsoft customers.
Microsoft basically blamed affected users for the issue, which, as one might expect, went over like a lead balloon. (The more nuanced explanation was problems arose due to how some companies were implementing Group Policy security. Its June update was meant to close security loopholes.)
On July 5, Microsoft officials posted a detailed blog post to the Microsoft "Ask Premier Field Engineering Platforms" blog about the issue, entitled "Who broke my user GPOs?".
Microsoft patch MS 16-072 (also known as KB 3163622), released June 14 for older versions of Windows, Windows Server, and Windows 10/Server 2016, was the source of the issue. The patch was meant to block possible man-in-the-middle attacks between the PC and the domain computer (DC).
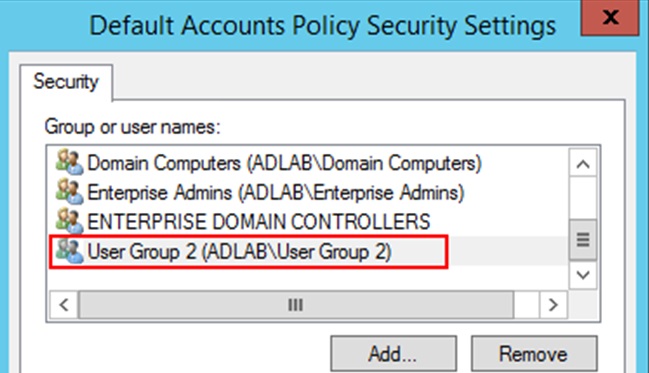
A couple of days later, Microsoft officials posted a resolution for the problem, which involved adjusting read permissions. But yesterday's Ask PFE post goes into a lot more granular detail about why things broke and the options admins have to fix them.
"The official guidance from Microsoft is to ensure the computer accounts have 'Read' access to the user policies you wish to have applied, says post author Sean Greenbaum, offering up a variety of ways admins could make this happen.
Windows IT Pro has been following the twists and turns on this one. Their Patch Tuesday RSS feed is worth a follow, in my opinion.