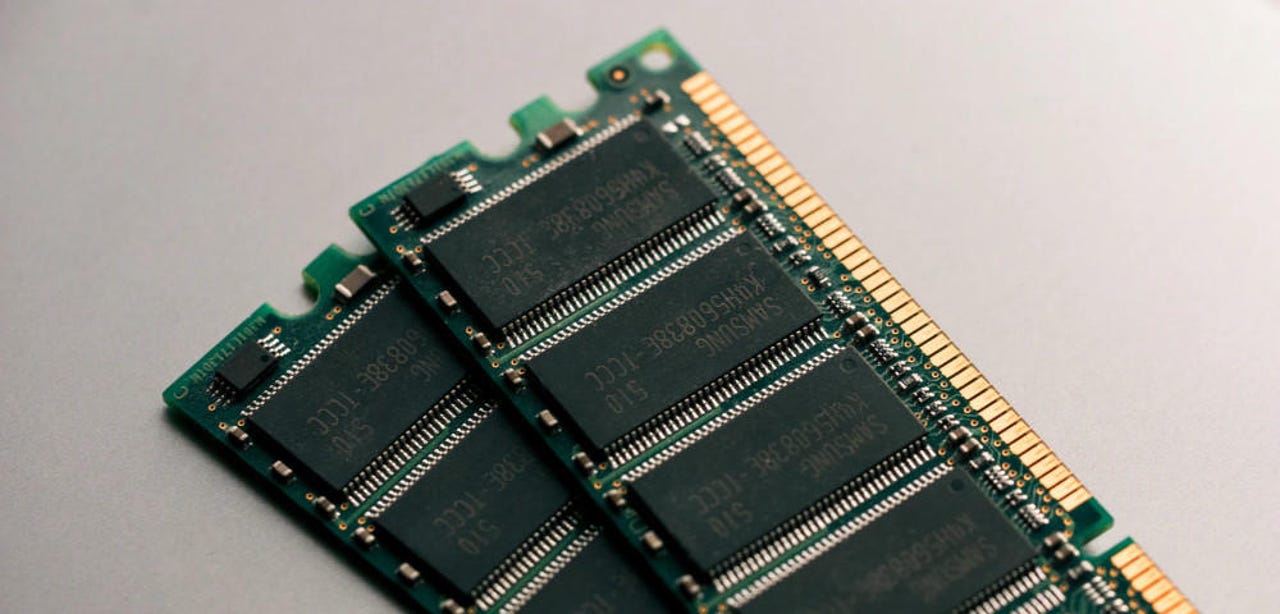
Modern RAM used for computers, smartphones still vulnerable to Rowhammer attacks

According to new research published today, modern RAM cards are still vulnerable to Rowhammer attacks despite extensive mitigations that have been deployed by manufacturers over the past six years.
These mitigations, collectively referred to as Target Row Refresh (TRR), are a combination of software and hardware fixes that have been slowly added to the design of modern RAM cards after 2014 when academics disclosed the first-ever Rowhammer attack.
A short history of Rowhammer attacks
On modern RAM cards, every time your computer handles data inside its memory, the actual data is saved inside memory cells, and each of these memory cells are arranged in a table-like grid pattern on the card's plastic base.
While this neatly-arranged design has helped engineers cram as many memory cells on a RAM card as possible, it has also enabled the possibility of electrical interference between memory cells.
This is, quintessentially, what a Rowhammer attack does. In 2014, academics realized that by performing very rapid read/write operations on a memory row -- "hammering" a memory row -- they could trigger electrical interferences, and eventually corrupt or alter data stored inside the RAM.
Although Rowhammer attacks were only described at a theoretical level, hardware vendors realized that with enough time, scenarios for launching Rowhammer attacks would eventually lead to something that could be exploited in a real-world scenario, and be used to alter data on computers or steal information from cloud servers.
Ever since 2014, the hardware industry has been trying to fix the Rowhammer conundrum, only to be proven wrong by the academic community at each step.
Every time vendors rolled out improvements, researchers would either find a bypass or find a new novel and faster method for launching Rowhammer attacks.
Over the years, there's been a lot of back-and-forth between the two camps. The list below summarizes the most important papers and advances in Rowhammer attacks:
- Academics showed how a Rowhammer attack could alter data stored on DDR3 and DDR4 memory cards alike
- Academics showed how a Rowhammer attack could be carried out via JavaScript, via the web, and not necessarily by having access to a PC, physically, or via local malware
- Academics demoed a Rowhammer attack that took over Windows computers via the Microsoft Edge browser
- Academics demoed a Rowhammer attack that took over Linux-based virtual machines installed in cloud hosting environments
- Academics used a Rowhammer attack to get root permissions on an Android smartphone
- Academics bypassed Rowhammer protections put in place after the disclosure of the first attacks
- Academics showed how an attacker could improve the efficiency of a Rowhammer attack by relying on local GPU cards
- Academics developed a technique to launch Rowhammer attacks via network packets
- Academics developed a Rowhammer attack that targets an Android memory subsystem called ION, and which broke the isolation between the OS and local apps, allowing data theft and total device control
- Academics developed a Rowhammer attack named ECCploit that works even against modern RAM cards that use error-correcting code (ECC)
- Academics discovered RAMBleed, a Rowhammer attack variation that can exfiltrate data from attacked systems, not just alter it.
- Academicsdeveloped a technique to speed up Rowhammer attacks with the help of field-programmable gate array (FPGA) cards, in an attack named JackHammer.
In all of this, TRR was supposed to be the ultimate patch for all the Rowhammer variations. It was meant to combine both software patches and hardware fixes by reengineering the actual RAM cards to prevent Rowhammer-induced interferences. It was exactly what Rowhammer creators wanted -- a redesign of the RAM hardware.
DDR4 memory cards were the first ones to receive TRR protections, and, for a few years, vendors thought they've finally plugged the Rowhammer issue.
Enter TRRespass
But in a new research paper titled today and titled "TRRespass: Exploiting the Many Sides of Target Row Refresh," a team of academics from universities in the Netherlands and Switzerland said they developed a generic tool named TRRespass that can be used to upgrade the old Rowhammer attacks to work on the new-and-improved TRR-protected RAM cards.
"In this paper, we demystify the inner workings of TRR and debunk its security guarantees," researchers started their paper.
"We show that what is advertised as a single mitigation is actually a series of different solutions coalesced under the umbrella term Target Row Refresh."
Researchers say that after studying all the different ways TRR was implemented by different vendors, they created TRRespass, a tool that can identify new row patterns that can be "hammered" like before.
"TRRespasss hows that even the latest generation DDR4 systems with in-DRAM TRR, immune to all known RowHammer attacks, are often still vulnerable to new TRR-aware variants of RowHammer that we develop," researchers said.
All in all, the research team said it tested 43 DIMMs (Dual In-line Memory Module; another name for laptop/PC/server RAM), and found that 13 DIMMs from the three major DRAM vendors (Samsung, Hynix, and Micron) are vulnerable to new Rowhammer variations generated via the TRRespass tool.
Mobile memory cards also vulnerable
"In addition to DDR4, we also experiment with LPDDR4(X) chips and show that they are susceptible to RowHammer bit flips too," researchers said.
LPDDR4, also known as Low-Power DDR, is the type of memory card used with smartphones and smart devices.
According to the research team's tests, TRRespass was able to successfully find new Rowhammer attacks against LPDDR4 memory cards used inside Google, LG, OnePlus, and Samsung smartphones.
The research team, made up of academics from ETH Zurich and Vrije University in Amsterdam, say they notified all affected vendors in November 2019.
"This triggered an industry-wide effort in addressing the issues raised in this paper," they said. "Unfortunately, due to the nature of these vulnerabilities, it will take a long time before effective mitigations will be in place."
Currently, this new TRR-bypassing Rowhammer attack is being tracked under the CVE-2020-10255 identifier. RAM products that receive software or hardware fixes for this vulnerability code will most likely take a few years to roll out from factory assembly lines.