A new Mirai-style botnet is targeting the financial sector

(Image: file photo)
A botnet made up of hijacked internet-connected televisions and web cameras has a new target, security researchers have found.
Three financial sector institutions have become the latest victims of distributed denial-of-service (DDoS) attacks in recent months. New research by Recorded Future's Insikt Group published Thursday points to what's likely to be the IoTroop botnet, used to pummel financial firms with internet traffic to overload servers and disrupt services.
TechRepublic: Most IoT devices can be hacked into botnets, research shows
The researchers say it's the largest attack since the Mirai-powered cyberattack in October 2016 that took down large swathes of the Western internet.
Botnets appear all the time and can rapidly grow and ensnare thousands of devices. Many lay dormant for months, quietly gathering pace but ready to cause disruption at a moment's notice. Although several botnets have appeared in the past year, none have resulted in any sizable attacks.
But that changed in January, when three DDoS attacks were launched within a few hours of each other.
The first was a DNS amplification attack that peaked at a traffic volume of 30Gbps per second. That may pale in comparison to a recent 1.7 Tbps attack -- some fifty times larger-- but can still cause considerable damage for companies not investing in DDoS mitigation protections.
It's thought that the botnets are built off Mirai's code, which was open-sourced and publicly released just weeks before the October 2016 attacks. Mirai was fairly simple compared to other botnets, which aggressively infected devices by using a list of pre-determined default usernames and passwords.
But the code's release opened the door for other botnets to spring to life.
It's believed that the more aggressive and advanced Reaper malware is thought to be behind the IoTroop botnet targeting financial institutions, said Priscilla Moriuchi, who co-authored the report with Sanil Chohan.
"This botnet is different than Mirai in composition and exploitation vector, likely compromising new bots based on vulnerabilities and not via unchanged administrator credentials," said Moriuchi, in an email.
Unlike Mirai, Reaper has become a large botnet that can run complex attack scripts to exploits flaws in the code of vulnerable devices, making it difficult to detect infections. The botnet exploits over a dozen known vulnerabilities in nine internet-connected products -- including some of the flaws that were originally used in Mirai.
Netlab said that the botnet had about 28,000 infected devices connected to one of the botnet's controllers as of its discovery in October -- and was ballooning in size.
This new botnet targeting financial sector companies has over 13,000 devices -- each with a unique IP address, the report said.
TechRepublic: DDoS attacks increased 91 percent in 2017 thanks to IoT
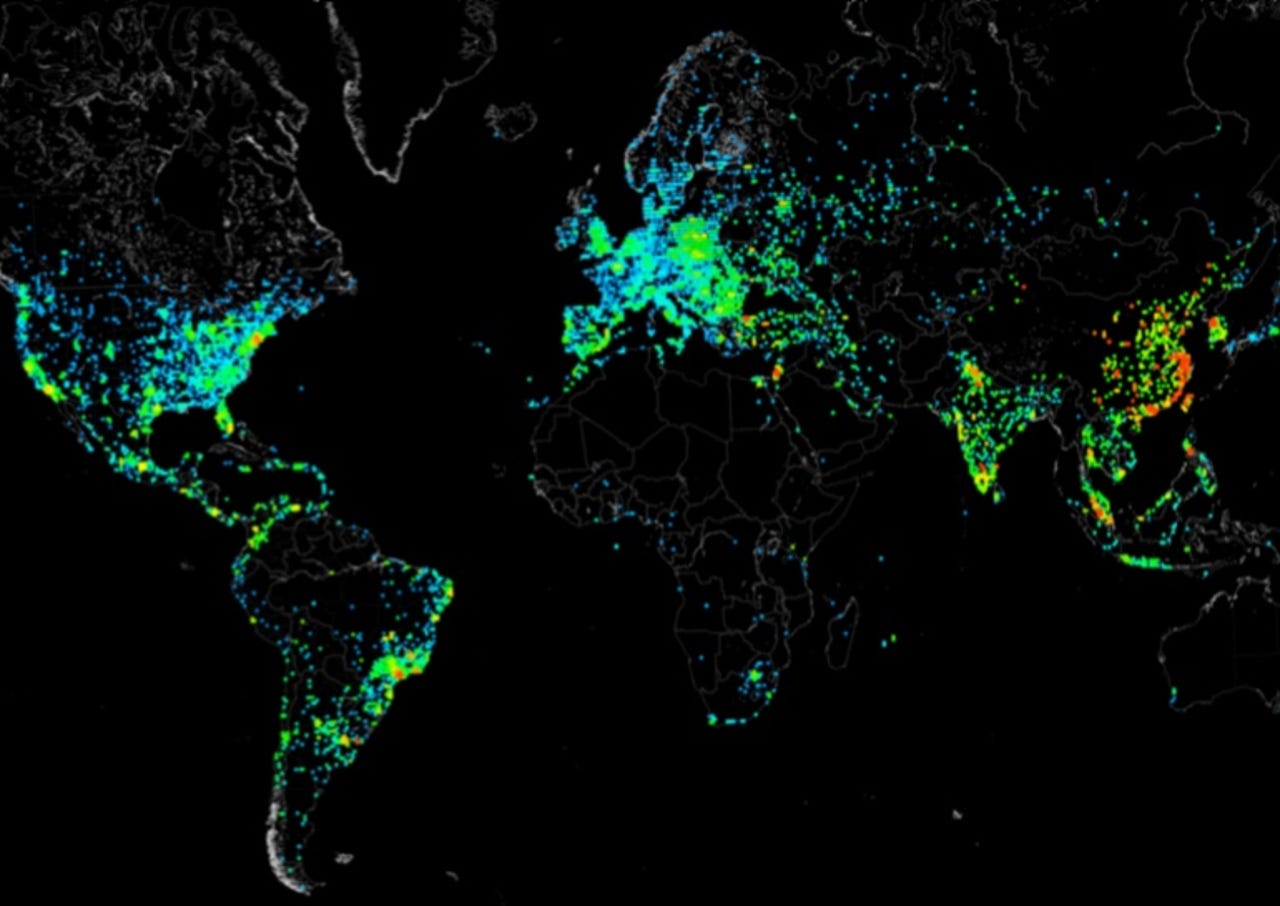
Most of the compromised devices are routers made by MikroTik, a Latvia-based networking company. It's thought that the attackers are leveraging the manufacturer's router bandwidth testing feature. The majority of infected devices were found in Russia, Brazil, and Ukraine -- a point that the researchers said is "likely to just be a reflection of the popularity" of the infected devices.
Moriuchi said that at least one of the companies affected by the attack had its customer services temporarily disrupted, but the extent of the financial or network damage wasn't known.
The researchers would not name the companies targeted by the botnet in their report, but said they were global Fortune 500 firms. It's also not known who is behind the attacks, they said.
But the botnet is likely not done. Although botnet attack activity has been largely quiet since January, the researchers said the botnet will grow in size and may be able to launch larger DDoS attacks against the financial sector in the future.
"It will become increasingly important to monitor the potential controllers and identify new IoT devices being added to the botnet in preparation for further attacks," the researchers said.