SonarSnoop attack can steal smartphone unlock patterns

Academics from universities in Sweden and the UK have come up with a new technique that turns a smartphone's built-in speaker and microphone into a crude sonar system to steal phone unlock patterns from Android devices.
The general idea behind this technique --named SonarSnoop-- is to use sound waves to track a user's finger position across a screen.
The technique consists of using a malicious app on the device to emit sound waves from the phone's speakers at frequencies inaudible to the human ear --between 18kHz and 20kHz.
What is malware? Everything you need to know about viruses, trojans and malicious software | Security 101: Here's how to keep your data private, step by step
Just like in the case of a submarine's sonar, the malicious app uses (the device's) microphones to pick up the sound waves bouncing back off nearby objects, which in this case is the user's finger(s).
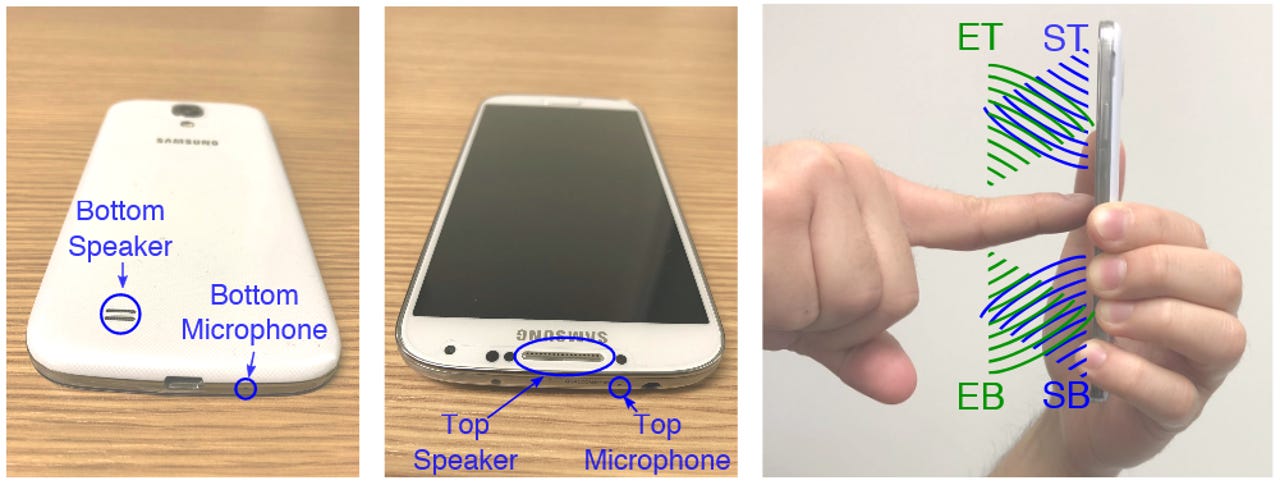
Depending on the placement of speakers and microphones on a device's case, machine learning algorithms can be built to read the collected data and determine possible unlock patterns.
In a research paper published last week, academics from Lancaster University in the UK and Linköping University in Sweden detail tests of SonarSnoop on a Samsung Galaxy S4 smartphone running Android 5.0.1.
The research team says it was able to reduce the number of possible unlock patterns by 70% using data obtained with SonarSnoop.
In its current form, SonarSnoop does not yield results as you might see in the hacking scene of Hollywood movies and does not spew out a 100% accurate unlock pattern.
SonarSnoop is in its early stages of experimentation. Work on this technique is underway, and accuracy is expected to improve.
The use of sound for user tracking is still a novel concept in the realm of cyber-security research. In past years, academics have explored the idea of using smartphone sensors such as accelerometers, gyroscopes, and proximity sensors to record and steal PINs and unlock patterns from smartphones[ 1, 2], but never sound waves.
The idea of using a sonar-like system for tracking users and their actions is slowly becoming a reality, ever since it captured the world's imagination after being featured in the 2008 Batman movie The Dark Knight.
A first attempt to replicate that system and use sound to track users in a room was attempted with the CovertBand research published in August 2017.
But the SonarSnoop research team credits FingerIO as the primary source of inspiration for their work. FingerIO is a novel concept published in March 2016, when academics created a sonar-like system to improve interaction with smartwatches.
With FingerIO, users could draw lines and shapes with a finger on their hand, near the smartwatch, and the smartwatch would use high-frequency sound waves to pick up the finger motions and translate them to touchscreen interactions. SonarSnoop is the evil version of FingerIO, where attackers use the same concept but to steal touchscreen interactions.
Researchers also point out that despite their experiment focusing on smartphones, SonarSnoop is "is applicable to many other kinds of computing devices and physical environments where microphones and speakers are available."
More details on the SonarSnoop technique are available in the research paper entitled "SonarSnoop: Active Acoustic Side-Channel Attacks."