This cheap and nasty ransomware will try to encrypt files across your network and removable drives

Stampado threatens to delete all files after 96 hours.
One of the cheaper forms of ransomware that crooks can buy on the dark web has evolved worm-like capabilities which enable it to move across networks and external drives, and even to re-encrypt files which have already been encrypted by other ransomware.
The Stampado ransomware is available to buy on the dark web for just $39, and is described by the seller as 'cheap and easy to manage ransomware' and offers buyers a 'full lifetime license'.
While it might be expected that cheap ransomware offers wannabe cybercriminals very little bang for their buck, cybersecurity researchers at Zscaler have analysed Stampado and have found it to contain self-propagating features which make it extremely effective -- it can spread across multiple devices and drives connected to the infected system.
Typically infecting victims via a spam email or drive-by download, the malware installs itself in the %AppData% folder with the name scvhost.exe, in an effort to pass itself off as the genunie Windows executable process svchost.exe.
Once Stampado starts running, it'll stealthily attempt to make copies of itself on the local network and on any removable devices attached to the infected machine. Stampado won't even spare the victim if their system is already infected with other ransomware, instead re-encrypting encrypted files.
This means the victim has to pay a ransom twice over -- once to each ransomware deliverer -- in order to get their files back. Ransomware variants which Stampado can re-encrypt include Locky, Cerber, Cryptowall, and more.
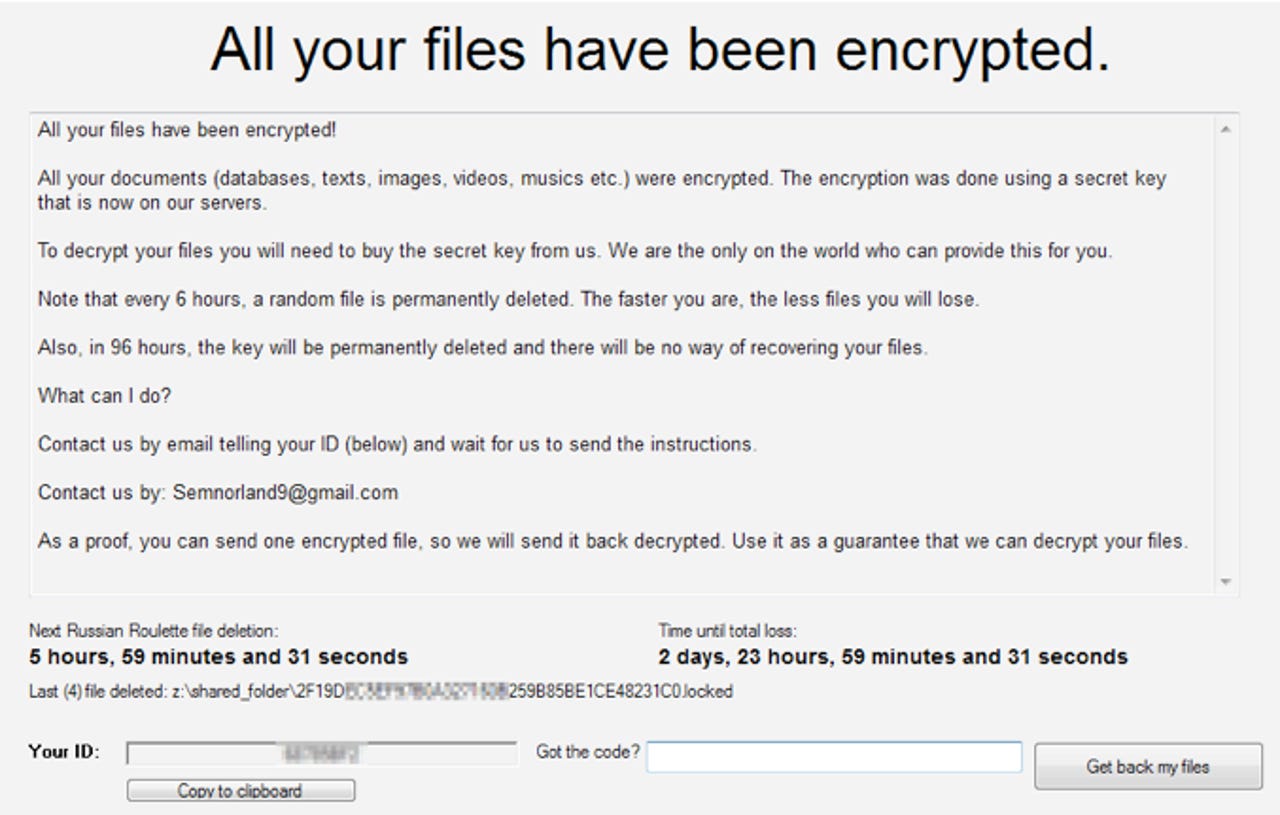
Once Stampado has encrypted all the target files, it'll only then display a ransom note, threatening users that if they don't pay, all their files will be deleted after 96 hours. It also threatens to delete a random file every six hours in order to scare victims into paying up.
Unlike other forms of ransomware, it doesn't demand a ransom in Bitcoin, but rather asks victims to contact an email address with the 'ID' that represents their infected system.
Zscaler cybersecurity researchers advise victims not to pay the ransom, stating that it's possible to decrypt files infected by Stampado on their own.
Ransomware has surged this year, recently becoming one of the three most common malware threats. The total cost of damages related to these attacks is set to top $1 billion before the end of 2016.