This ransomware is now one of the three most common malware threats

Locky made up 6 percent of all malware attacks during September
The threat of ransomware attacks continues to grow. One particular strain of the cryptographic file-locking malicious software has now risen to become one of the top three most prevalent forms of malware used by hackers and cybercriminals.
Ransomware has exploded in 2016 and is increasingly targeting business networks instead of individual users. The total cost of damages related to these attacks is set to top $1 billion this year.
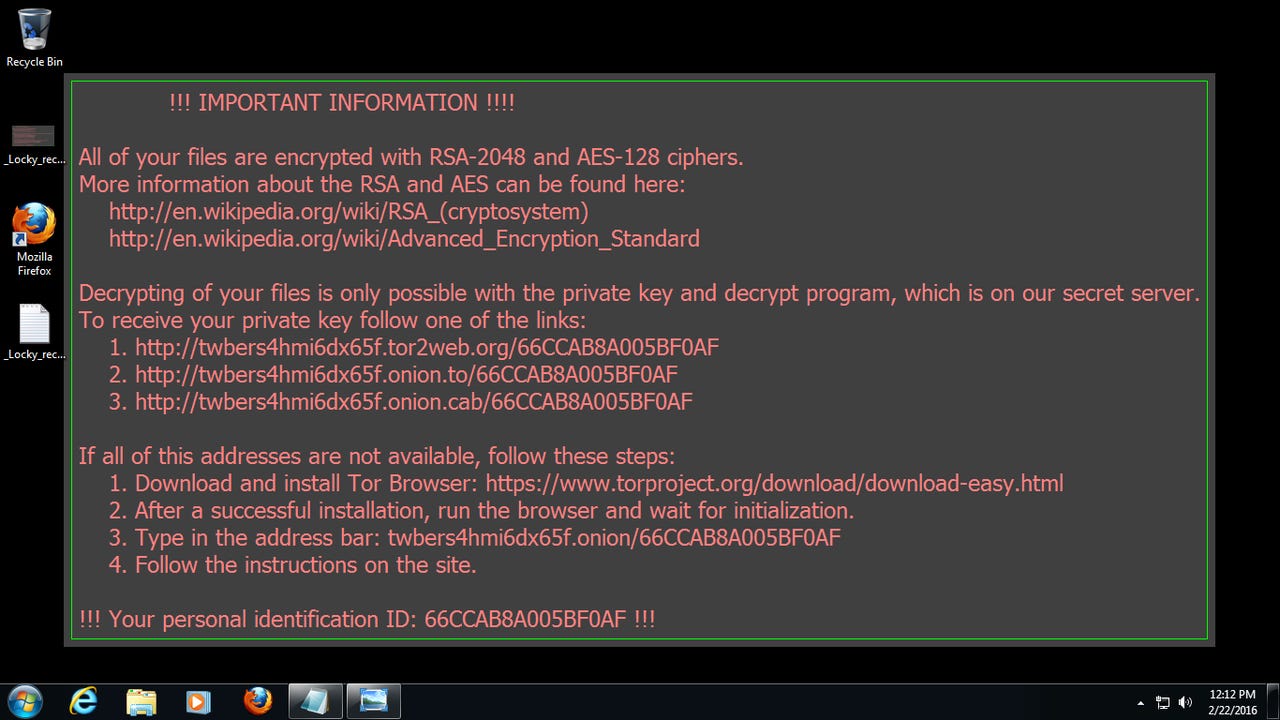
It's the Locky family which is currently most prevalent family of ransomware. The malware infamously took down the network of a high-profile Los Angeles hospital in February, and its notoriety has led to it entering the top three most common forms of malware.
According to the latest Global Threat Index by cybersecurity researchers at Check Point Software, Locky accounted for 6 percent of all recognised malware attacks during September, while the total number of ransomware attacks across the globe rose by 13 percent.
Why has Locky and other ransomware become so successful? It's simply because the attacks are easy to carry out and victims are willing to pay to get their data back.
"The continued growth in ransomware is a symptom of the number of businesses simply paying ransoms to release critical data, making it a lucrative and attractive attack vector for cybercriminals," said Nathan Shuchami, head of threat prevention at Check Point.
Locky -- which is mainly spread via emails containing a malicious attachment disguised as a Word or Zip file -- was less common than only two other forms of malware during the month of September.
Sality, a virus which allows remote operations and downloads of additional malware to infected systems in order to deliver furthers malicious payloads to others, accounted for slightly more infections than Locky, but, like Locky, accounted for 6 percent of all malware attacks during September.
Despite being eight years old, the Conficker worm, which recruits infected machines into remotely controlled, malware-downloading botnets, accounted for the most malware attacks in September (14 percent of all attacks).
In total, the top ten most prevalent malware families were responsible for half of all recognised attacks during September, say Check Point researchers, who've previously warned that new malware hits an enterprise network every four seconds.
New entries to the top ten include Chanitor, a downloader for malicious payloads; the Blackhole exploit kit, which has returned despite its creator being in prison; and the Nivdort bot.
Check Point's Global Threat Index also details the most significant malware threats to businesses via mobile devices, with the HummingBad Android malware representing the most common delivery from cyberattackers.
Second to HummingBad during September was Triada, a backdoor for Android which grants super-user privileges to downloaded malware and spoofs URLs, and Ztorg, a Trojan which downloads and installs applications on the phone without the user's knowledge.
With so many threats attacking businesses from all directions, organizations and users must remain vigilant in order to avoid infection.
"With the number of active malware families remaining high, combined with the range of attack methods used by the different families, it is clear to see the scale of the challenge organizations face in securing their network against exploitation by cybercriminals," said Shuchami.
The bad news is that ransomware doesn't show any signs of slowing down and it's likely to only become a bigger problem during 2017.