New Cryptowall ransomware makes locked files even harder to recover

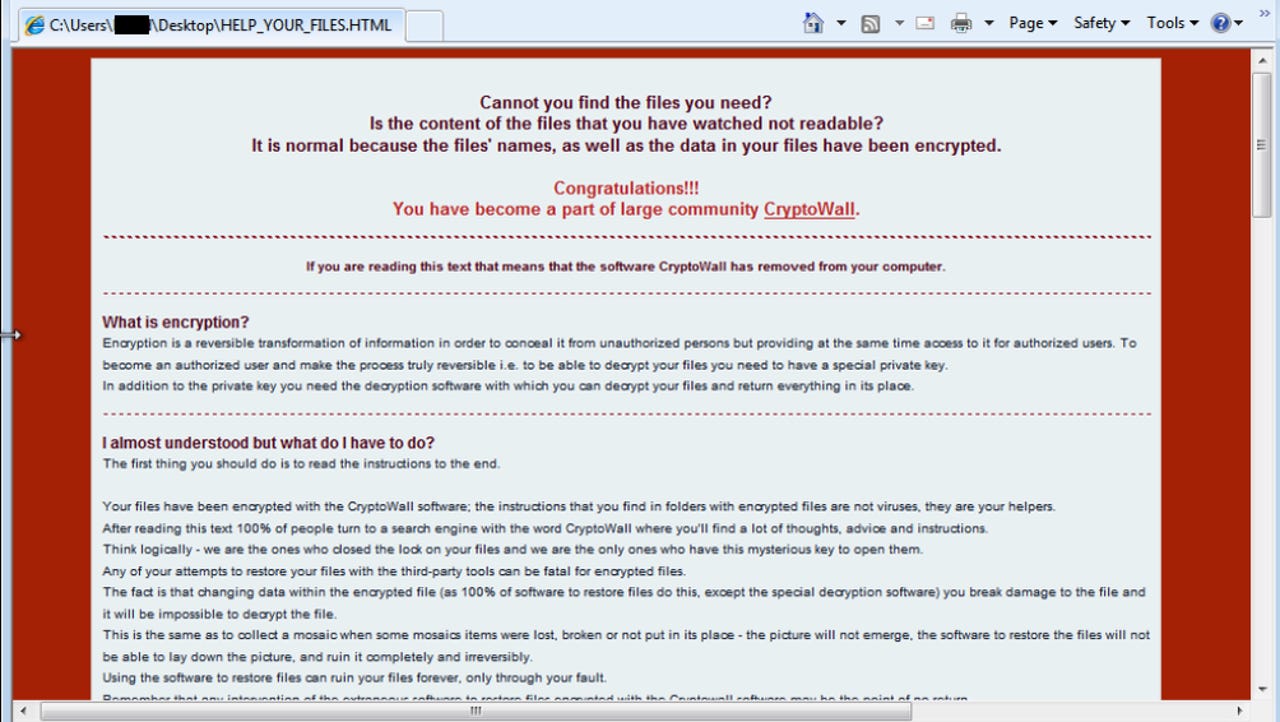
Cryptowall, the now-infamous encryption malware that locks files for ransom, has been updated.
The ransomware, which upon install encrypts files making it almost impossible to regain access, now scrambles file names making it even harder for victims to know which files are which. System restore points are also erased, taking away the option of returning to a previously saved state.
Adding insult to injury, the malware also mocks the user, congratulating the user for becoming [sic] "part of large community," according to BleepingComputer, which first detailed the changes.
The ransomware continues to use bitcoin as the means of payment, which like in previous versions is handled by a centralized Tor-based command-and-control server to store decryption keys, making the attackers almost impossible to trace.
Users are tricked into opening a zipped attachment from a spam campaign, which contains a malicious file, triggering an executable payload.
Ransomware hits thousands every week, and costs users $18 million in losses, according to estimates from the FBI. Other figures suggest the Cryptowall family alone has generated about $325 million in bitcoin ransoms.
While Cryptowall remains by far one of the most common families of the malware, its success has given rise to new families and variants.
But not all malware is created equally, nor is coded correctly, which in some cases can cause devastating data loss.
New ransomware discovered late last month uses a single same master encryption key to encrypt files, making it easier for victims to share keys and regain access to files without paying the ransom. But analysis showed that badly-written code would destroy a victim's data because, when the files were encrypted, the key wasn't saved.
Storing a backup can mitigate the damage done by file-encrypting ransomware.