Tor Project works on boosting encryption for next release

The Tor Project hopes to boost the security of the Tor onion router and network through the introduction of a distributed random number generator.
In a blog post on Wednesday, the non-profit revealed that Tor researchers and developers met as part of a hackfest in Montreal, Canada, to share ideas on how to bring Tor to a new level of personal security.
The Tor network, otherwise known as The Onion Router, relies on nodes and relays to disguise traffic flowing in and out, concealing original IP addresses and making surveillance more difficult to accomplish. However, no system is 100 percent secure, and as a recent case where the FBI used an exploit to compromise the network highlights, Tor must stay ahead of the game and boost privacy as and when it can -- albeit by relying on donations and sponsors.
The purpose of the Montreal trip was to push forward the development of next-generation security features. The Tor network team said:
"Our main goal with this meeting was to accelerate the development of the Next Generation Onion Services project (aka proposal 224). We have been working on this project for the past several months and have made great progress.
However, it's a huge project! Because of its volume and complexity, it has been extremely helpful to meet and work together in the same physical space as we hammer out open issues, review each other's code, and quickly make development decisions that would take days to coordinate through mailing lists."
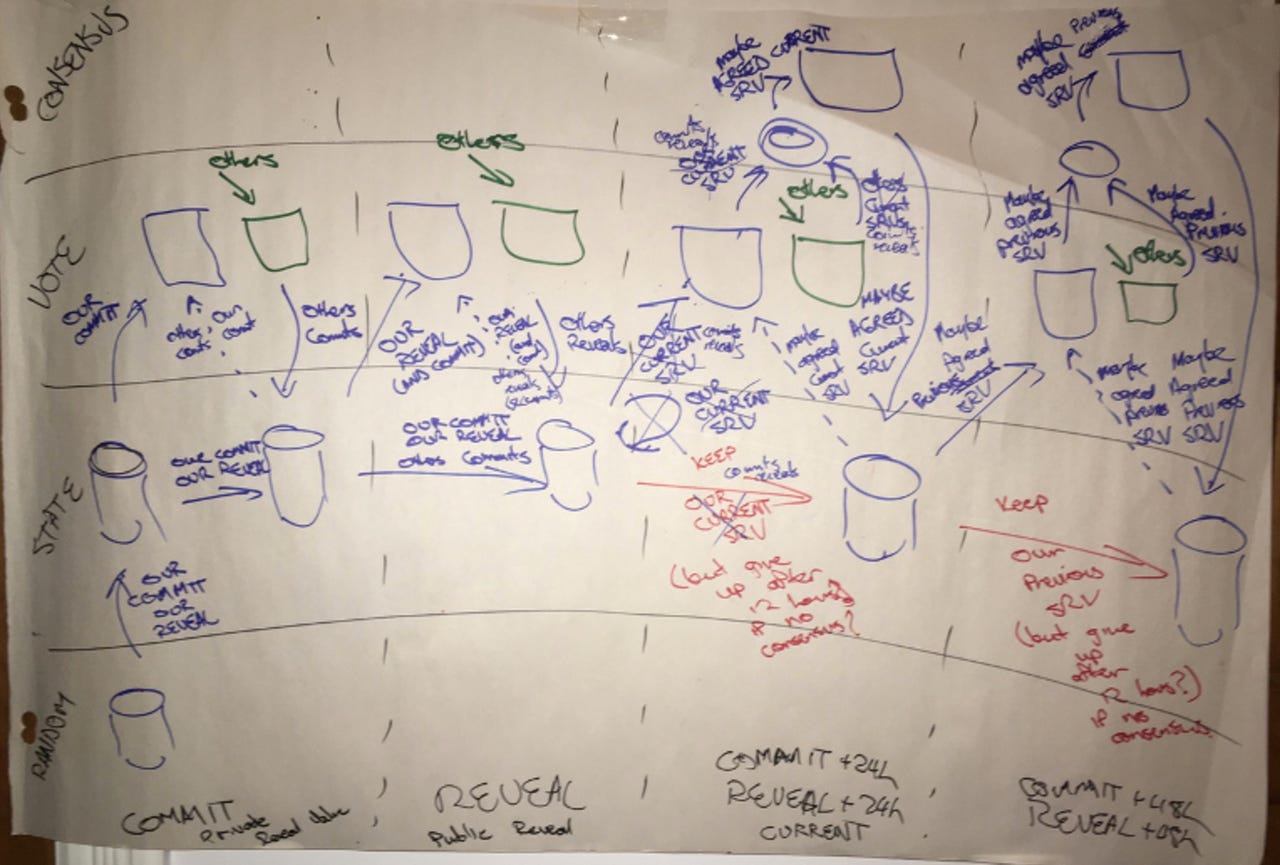
One of the main features to be worked on is a "distributed random number generator" which is important for encryption, The generator is a system which connects up different PCs which communicate and generate a single random number which cannot be predicted through analytics. These numbers act as the backbone for encryption key generation, and so the more unpredictable they are, the more secure encrypted channels are.
By introducing this level of unpredictability into the Tor network, the team says user privacy will be enhanced.
The distribution system's protocol was implemented into Tor several months ago, but is still undergoing reviews, audits and tests, and the team believes the system can be improved further.
In the future, Tor developers hope to introduce 55-character-long onion addresses for websites, instead of today's 16-character-long limits.
"While no concrete design has been specified yet, we identified the need for a checksum and version field on them," the team says. "We also discussed modifications to the Tor Browser Bundle that could improve the user experience of long onion addresses."
The team will not throw away the current system, however. Instead, when the next version of Tor is deployed, the network will support both types of onion services. During testing, the team also found that the new system will still work even in the case of network failure.
The latest deployment is still months away from release and the team have their hands full refining and polishing up the protocol. However, for Tor users -- whether they are the privacy-conscious, activists, journalists, fighting censorship or other parties -- the Tor upgrade is welcome news.
You can check out proposal 224 here.
10 things you didn't know about the Dark Web
Read on: Top picks