127 million user records from 8 companies put up for sale on the dark web

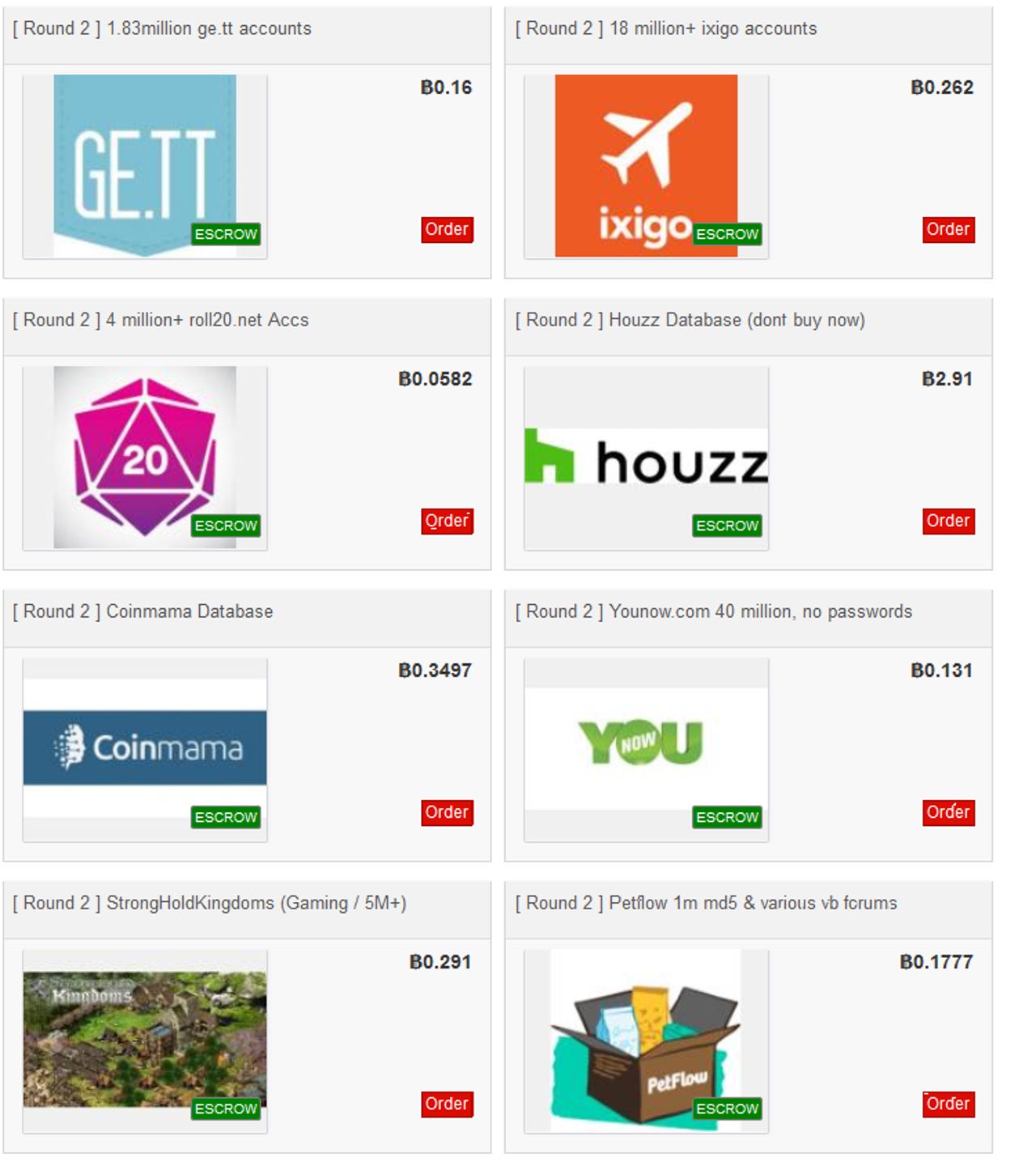
An individual who earlier this week was selling 620 million user records stolen from 16 companies has now put up a second batch of hacked data totaling 127 million, originating from eight companies.
The data is currently being sold on Dream Market, a dark web marketplace where crooks sell an assortment of illegal products, such as user data, drugs, weapons, malware, and others.
The individual selling the data goes by the name of Gnosticplayers, and it's currently unclear if they're the one/ones who hacked the 24 companies, or just a third-party who purchased the data from the real hacker and is now re-selling it for a bigger profit.
According to tech news site TechCrunch, who first reported this new batch of hacked accounts going for sale on Dream Market, Gnosticplayers is asking for roughly four bitcoin, which is about $14,500 in fiat currency. Prices vary depending on the quality of the user data and the difficulty in cracking password hashes.
This second batch of hacked accounts includes data from the following companies:
| Company | DB size | Breach date | Price | Content |
|---|---|---|---|---|
| Ge.tt (file sharing service) | 1.83 Mil | 2017/12 | ฿0.16 | firstname, lastname, password hash (SHA256), Facebook ID, referer |
| Ixigo (travel and hotel booking) | 18 Mil | 2019/01/01 | ฿0.262 | password hashes (MD5), full name, Facebook URL, IP address, username, email, and, for some users even the passeport ID number, passeport name etc |
| Roll20.net (gaming) | 4 Mil | 2019/01/01 | ฿0.0582 | name, email, passwords (bcrypt), nickname, gaming data, some redacted financial data, server log data |
| Houzz (interior design) | 57 Mil | 2018/07 | ฿2.91 | email, password (SHA256), registration date, name |
| Coinmama (cryptocurrency exchange) | 0.42 Mil | 2017/08/02 | ฿0.3497 | email, password (PHPASS), other unspecified |
| Younow (live streaming) | 40 Mil | 2017/10 | ฿0.131 | full name, profile ID, IP addresses, email, Facebook email and ID, Instagram ID, Google ID, Twitter ID |
| StrongHoldKingdoms (gaming) | 5 Mil | 2018/09 | ฿0.291 | username, email, password (HMAC-RIPEMD160), profile stats, gaming data, SteamID |
| Petflow (pet food delivery) | 1 Mil | 2017 | ฿0.1777 | email, username, password (MD5), other undisclosed data |
Of the companies listed above, Houzz had already come clean about its data breach last week. The other seven companies did not publicly reveal any security breaches before the publication of today's ads.
This new batch of stolen databases comes after earlier this week, the same Dream Market user was selling the following user databases from 16 other companies:
| Company | DB size | Breach date | Price | Content |
|---|---|---|---|---|
| Dubsmash (video sharing) | 161.5 Mil | 2018/12 | ฿0.549 | user ID, password (SHA256), username, email, language, country, more |
| 500px (image hosting) | 14.8 Mil | 2018/07 | ฿0.217 | username, email, password (MD5, SHA512, or bcrypt), first and last name, birth date, gender, city, country |
| EyeEm (image hosting) | 22.3 Mil | 2018/02 | ฿0.289 | email and password (SHA1) |
| 8fit (fitness app) | 20.1 Mil | 2018/07 | ฿0.2025 | email, password (bcrypt), country, country code, Facebook token, Facebook profile picture, name, gender, and IP address |
| Fotolog (photo app) | 16 Mil | 2018/12 | ฿0.52 | email, password (SHA256), security question and answer, name, location, various profile data |
| Animoto (video editing service) | 25.4 Mil | 2018 | ฿0.318 | username, password hash (256), email, country, full name, and date of birt |
| MyHeritage (family genealogy service) | 92 Mil | 2017/10 | ฿0.549 | email, password hash (256), account creation date |
| MyFitnessPal (UnderArmor's fitness app) | 150 Mil | 2018/02 | ฿0.289 | user ID, username, email, password hash (SHA1) with a fixed salt, IP address |
| Artsy (art sharing portal) | 1 Mil | 2018/04 | ฿0.0289 | email, name, IP addresses, location, and password (SHA256) |
| Armor Games (online gaming) | 11 Mil | 2018/12 | ฿0.2749 | username, email, password (SHA256), date of birth, gender, location, and profile data |
| Bookmate (e-book and audiobook app) | 8 Mil | 2018/07 | ฿0.159 | username, email, password (SHA512 or bcrypt), gender, date of birth, and profile data |
| CoffeeMeetsBagel (dating app) | 6 Mil | late 2017 to mid-2018 | ฿0.13 | full name, email, age, registration date, and gender |
| DataCamp (coding platform) | 0.7 Mil | 2018/12 | ฿0.013 | email, password (bcrypt), location, and profile data |
| HauteLook (online shopping) | 28 Mil | 2018 | ฿0.217 | email, password (bcrypt), and name |
| ShareThis (social sharing widegt) | 41 Mil | 2018/07 | ฿0.217 | name, username, email, password (DES), gender, date of birth, and profile data |
| WhitePages (online phone book) | 17.7 Mil | late 2017 | ฿0.434 | name, email, password (SHA1 or bcrypt) |
Animoto, MyFitnessPal and MyHeritage previously disclosed breaches last year. DataCamp, 500px, Dubsmash, EyeEm, Artsy, 8fit, and CoffeeMeetsBagel confirmed this week that they've been breached as well, giving credence to the seller's boast that this is real data and not just a scam.
These 16 databases are no longer available for sale now. Gnosticplayers said he took them down after buyers complained that a prolonged sale would eventually lead to some of these databases leaking online, and becoming available to everyone.
More updates to follow as we're still looking at the data.
Data leaks: The most common sources
More data breach coverage:
- Chinese company leaves Muslim-tracking facial recognition database exposed online
- Hackers wipe US servers of email provider VFEmail
- Dunkin' Donuts accounts compromised in 2nd credential stuffing attack in 3 months
- China hacked Norway's Visma cloud software provider
- Online casino group leaks information on 108 million bets, including user details
- Airbus data breach impacts employees in Europe
- Massive breach leaks 773 million email addresses, 21 million passwords CNET
- Hackers turn to data theft and resale on the Dark Web for higher payouts TechRepublic