After LinkedIn heist, here's how Microsoft is tightening password security

The dynamically-banned passwords feature is live in Microsoft Account Service for consumers and in a private preview for Azure Active Directory.
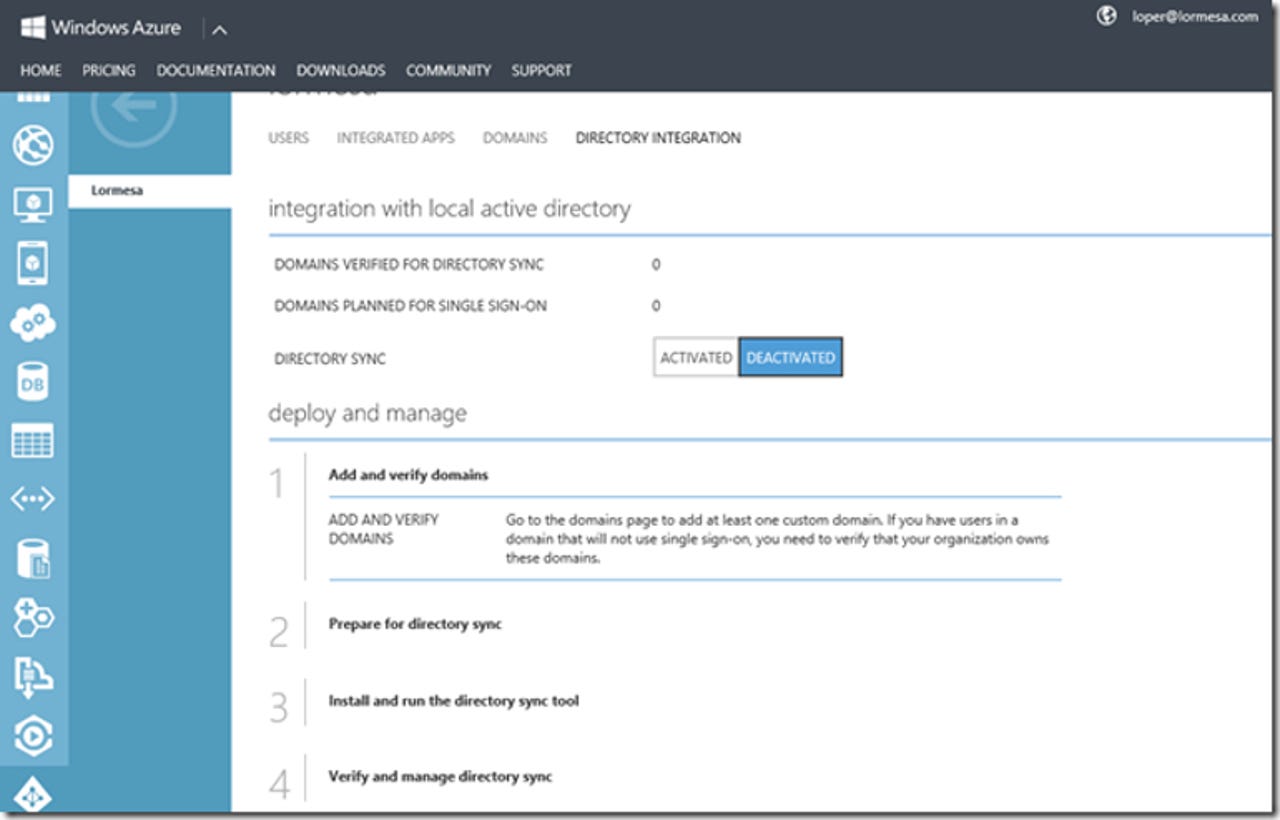
Microsoft will soon launch a new Azure Active Directory (AD) feature that will let admins stop users from picking easily-guessed passwords.
Following last week's leak of 117 million LinkedIn credentials, Microsoft has detailed how it's using the leaked list and others like it to prevent Microsoft Account users from picking passwords that appear frequently in stolen data.
Each time Microsoft becomes aware of a new password leak, it updates its list of common passwords to block any that match or come close to matching the current attack list.
The dynamically-banned passwords feature is live in Microsoft Account Service for consumers and in a private preview for Azure AD. Microsoft will roll out the feature to over 10 million Azure AD tenants in coming months.
Another password feature, currently in public preview in Azure AD, addresses password reuse.
IT admins will have the ability to lock down corporate email accounts automatically if the username and password for those accounts match credentials in a newly-leaked list.
When Microsoft discovers a new list of compromised credentials, it runs them through a system that compares hashes of the passwords with those stored with live accounts.
If it identifies an at-risk account, Microsoft locks it and prompts the user to verify their identity and reset their password. This same capability will soon be available to Azure AD users, allowing the enterprise to lock down accounts before leaked credentials are abused.
Microsoft's Identity Protection Division also released a new password best practice paper yesterday, urging admins to stop using policies that require users to pick long, complex passwords that need to be changed frequently. Humans tend to work around the obstacles and end up choosing worse passwords, Microsoft notes.
The UK GCHQ's info-sec arm CESG last month also came out against frequent password changes because it often results in weaker passwords.
Instead, Microsoft says the policies should encourage users to create unique passwords, hence the ban on commonly-used passwords. Admins should also discourage their users from reusing passwords for corporate accounts on external sites