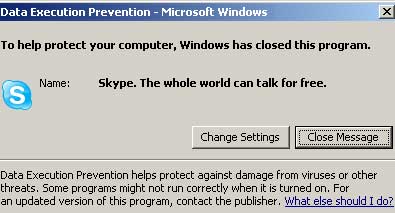
Alert: Skype 2.0 triggers Data Execution Prevention Warning

Our own George Ou has found that Skype 2.0 seems to trigger a Data Execution Prevention warning on his new PC.
Data Execution Prevention, or DEP for short, is a new feature built into Windows XP Service Pack 2 that harnesses the NX and ND (No Execute and Execute Disable) functionality built into newer Intel and AMD processors that seeks to block common security exploits from rolling into action.
But when George ran Skype 2.0, DEP swung into action and showed him an alert that looked like what I showed you at the top of this post.
George fixed it by clicking on the "Change Settings" button in the warning box. When the Performance Options box came up, he revised his settings to mark Skype as an exception to the "Turn on DEP for all programs and services except those I select."
Here's what George did:
Even though George fixed the problem he is not happy about it.
"While this may seem simple enough, it isn't always so obvious to the novice user who may not even be an administrator with the necessary privileges to modify the DEP settings," he writes. "This is certainly out of character for an application that prides itself in ease-of-use. For all the user knows, Skype just looks like any other malicious code trying to infect their computer."
Consider yourself warned, Skype users.
"With the DEP exception in place, an even bigger concern is the security implications of turning off DEP protection for Skype. Skype is an application that interacts with the wild and public Internet and Skype has had its share of vulnerability issues in the past so turning off a critical protection mechanism like DEP is the last thing I want to do," George points out. "Having DEP enabled on Skype will at least give users some protection if Skype has any future vulnerabilities."
George and I think that Skype really needs to fix whatever is causing the problem ASAP.