Amazon denies Sony used AWS for denial-of-service counter-attack


Amazon has denied its cloud service was used to conduct counter-attacks against sites offering data said to be stolen in the Sony hack last week.
Struck by a group known only as the "Guardians of Peace," which claimed responsibility for the hack, the media giant was suddenly thrust into the spotlight, as a treasure trove of valuable information was made available for the consumption not only of the public, but also its rivals.
Sweden ddos pinbox
Personal emails from Sony's board allegedly exchanging pithy remarks about actors and movie deals could prove to be a PR disaster -- such as an email sent between Scott Rudin and Sony Pictures co-chairman Amy Pascal allegedly labeling actress Angelina Jolie a "minimally talented spoiled brat" with a "rampaging ego."
The ongoing saga, however, becomes even more complex.
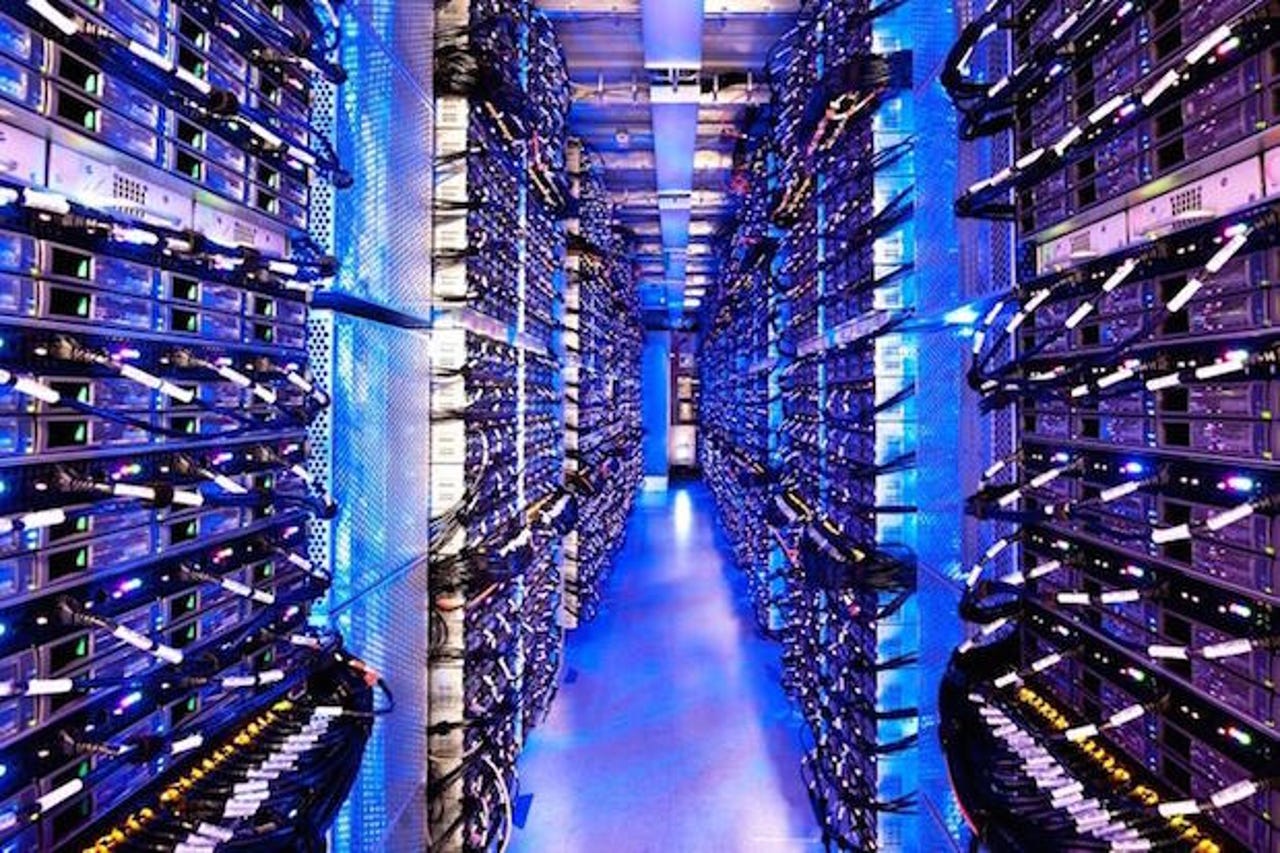
On Wednesday, tech site Recode reported that Sony had used hundreds of computers in Asia to initiate denial-of-service attacks on websites offering Sony's stolen data to the public. The sources of these attacks were allegedly Amazon Web Services data centers based in Tokyo and Singapore.
A spokesperson for Amazon Web Services told ZDNet the alleged activity is "not currently happening" on the service.
"AWS employs a number of automated detection and mitigation techniques to prevent the misuse of our services. In cases where the misuse is not detected and stopped by the automated measures, we take manual action as soon as we become aware of any misuse," the spokesperson added.
Here's how AWS' systems would work in the Sony counter-hack scenario. AWS has automated systems and measures to stop denial of service attacks from being launched. These attacks are monitored across AWS network so an exact customer wouldn't be identified immediately. In the event an attack was launched, there are measures in place to shut it down quickly. In the Sony scenario, the company could have launched an attack that was shut down just as quickly. Or Sony could have been stopped at the gate before anything started.
If AWS resources were used to initiate these attacks, Sony would not only be in breach of Amazon's terms and conditions agreement, but also the law.
Within the agreement signed by AWS users, the tech giant stipulates that network abuse is not tolerated. Among a list of prohibited activities including crawling, open proxy operation and unauthorized monitoring.
"Inundating a target with communications requests so the target either cannot respond to legitimate traffic or responds so slowly that it becomes ineffective," the agreement states under the "denial of service" paragraph.
"It's illegal for companies to counter-attack," Jennifer Stisa Granick, Director of Civil Liberties at the Stanford Center for Internet and Society told ZDNet in an email. "That line will be fuzzy depending on the tech used, but the law is clear, no unauthorized access except for lawfully authorized government activity."
CloudFlare, which offers denial-of-service protection and network monitoring, said it has not seen anything that would suggest Sony had conducted a counter-attack. The company said it would continue monitoring the situation.
ZDNet has reached out to Sony and will update if we hear back.
Updated at 11:55am ET: with comment from CloudFlare and again at 5:40pm ETwith clarity paragraph after Amazon statement.
Read on: In the world of security
- Sony Pictures corporate files stolen and released in cyberattack
- Amnesty's Detekt tool wants to help you thwart government spying
- Snapchat issues outright ban on third-party apps following 4chan hack
- Hackers infiltrate White House network
- Teen hackers charged with stealing $100 million in Army, Microsoft tech
- Analysis casts doubt on FBI claims over Tor website seizures
- High volume DDoS attacks rise in Q3 2014
- Apple iOS Masque flaw dangers: Communication app infiltration discovered
- UK hires hackers, convicts to defend corporate networks