.ANI attack update: Rootkits, 'Hot Britney pics' spam

The ongoing Windows animated cursor (.ani) flaw attack just keeps getting worse.
The latest reports indicate that an e-mail spam run promising hot photographs of Britney Spears is the latest lure to infect Windows users with backdoor Trojans and keystroke loggers.
An alert from Websense Security Labs offers the latest:
We are actively tracking more than 450 unique websites which have been compromised. Most of the sites have ALL pages infected within the site which add up to tens of thousands of pages with exploit code links on them.
[Users] who visit one of the thousands of pages will be infected with a generic password stealer that will run without any user-interaction.
Assuming users connect to the sites they will be redirected to two unique locations which are hosting exploit code which in turn downloads and installs a file called "ad.exe". The file includes a generic password stealer and is not detected well by most Antivirus companies.
Now comes word of an e-mail spam run, which is even more dangerous since, with the e-mail attack vector, the user does not have to click to visit a rigged Web site. Simply opening an e-mail could trigger an infection. In this case, however, the user is being lured to malicious Web sites:
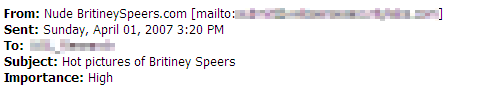
Users receive an email with the subject line "Hot Pictures of Britiney Speers" that is written in HTML and has anti-spam avoidance text within the HTML comments.
Users who click on the links are redirected to one of several websites that we are tracking. The sites contain obfuscated JavaScript. The decoded JavaScript sends all users to the same website, which is hosting the exploit code.
...The main server that hosts the exploit code is hosted in Russia and has been used by groups that have installed rootkits, password stealing Trojans, and other nefarious code in the past.
Roger Thompson, CTO at Exploit Prevention Labs, says a stealth rootkit is also being used in the spam attack:
It downloads a 36k progam called 200.exe. When run, 200.exe writes itself back out as Winlogon.exe, and adds itself to HKCU... CurrentVersion\Run to ensure it gets into the execution cycle on reboot.When it runs, it emails out to a hotmail account, presumably to announce that the victim has been 0wned, and then calls out to a different server on port 80 every five minutes, presumably looking for commands. In other words, it's a bot / backdoor. Oh, and it's a rootkit.
If you haven't applied the MS07-017 patch yet, go do it now. Christopher Budd, on the MSRC blog, confirms that Patch Tuesday on April 10, 2007, is still very much on schedule.