Apple failed to fix "rootpipe" backdoor flaw, researcher warns

A bug that Apple said it fixed in the latest release of its OS X desktop operating system continues to plague every Mac owner, after a researcher found a way to exploit the flaw again.
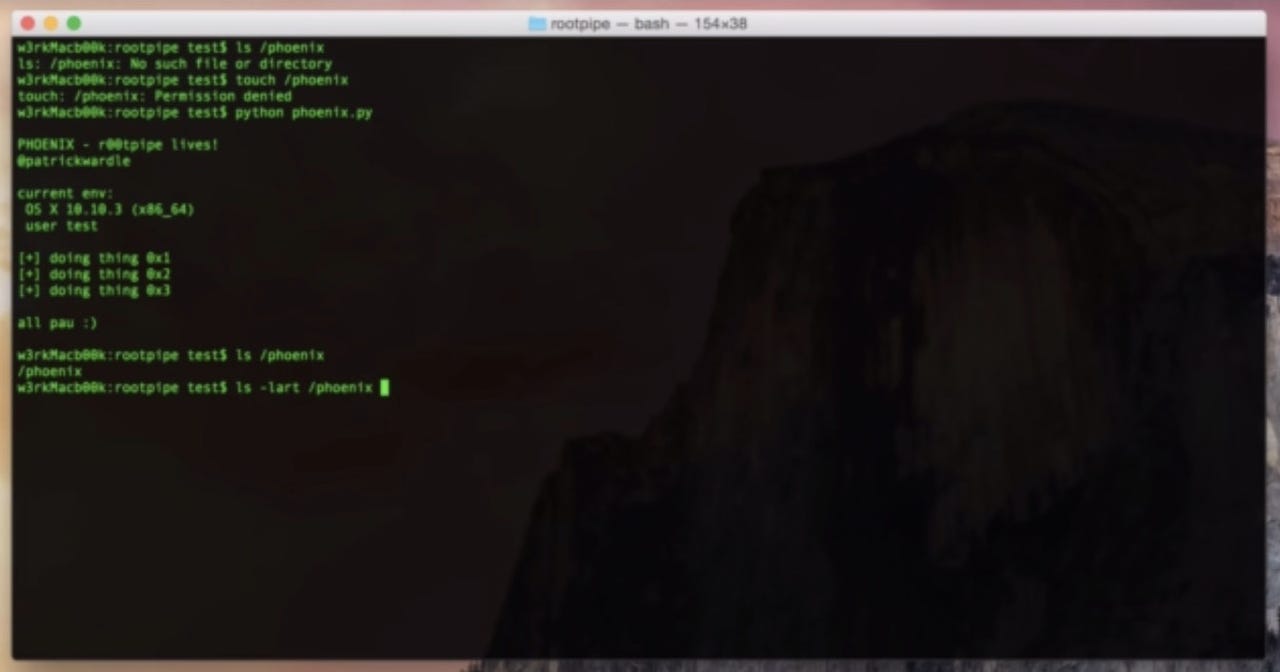
Dubbed "rootpipe," researchers claimed the vulnerability allows hackers or malicious actors to escalate a user's privileges, making it easier to spread system-wide malware or take over an entire machine.
Apple indicated that the bug would only be fixed in the latest version of its software, OS X Yosemite, effectively forcing every older operating system user to upgrade in order to be patched.
But, one researcher took a second attempt at exploiting the vulnerability on a patched machine, and succeeded.
Patrick Wardle said he was on a flight home when he found a "novel, yet trivial way" for any user to exploit the vulnerability for a second time -- even on a patched machine -- allowing the user to become the highest user privilege level, known as "root."
Wardle said he informed Apple of the technical details behind the attack, but did not release further details in the spirit of responsible disclosure.
It's not the first time Apple is said to have slipped up in issuing security updates. In iOS 7, a bug now known as the "goto fail" flaw allowed devices to be hit with man-in-the-middle attacks.
We reached out to Apple but did not hear back at the time of writing.