Apple hack exploited with new phishing campaign

In order to make sure a phishing campaign works, the victim has to believe an email is legitimate. It's no surprise that the Apple security breach is the latest event to be taken advantage of.
Phishing attacks are a relatively simple way to steal data. Users click on an email they believe to be legitimate, allowing malware to be installed or submitting login details for a service, whether it be a fake bank email, service, or the Spanish lottery. Perhaps if you're particularly lucky, there is a wealthy gentlemen in Africa who wants to transfer millions of dollars to your account -- but only if you forward along some of the costs in advance, of course.
Phishing campaigns have advanced from the days of poorly-written English and laughable stories. Now, some scammers take pains to make sure the email looks legitimate, from including a PayPal logo to the typical disclaimer of a bank at the bottom. Once clicked on, users are often directed to legitimate-looking websites set up to store the credentials you input.
In a new campaign, the recent service outage of Apple's Dev Center has prompted a flood of phishing emails asking users to change their passwords -- and short as the email is, to the average user, it may be viewed as legitimate.
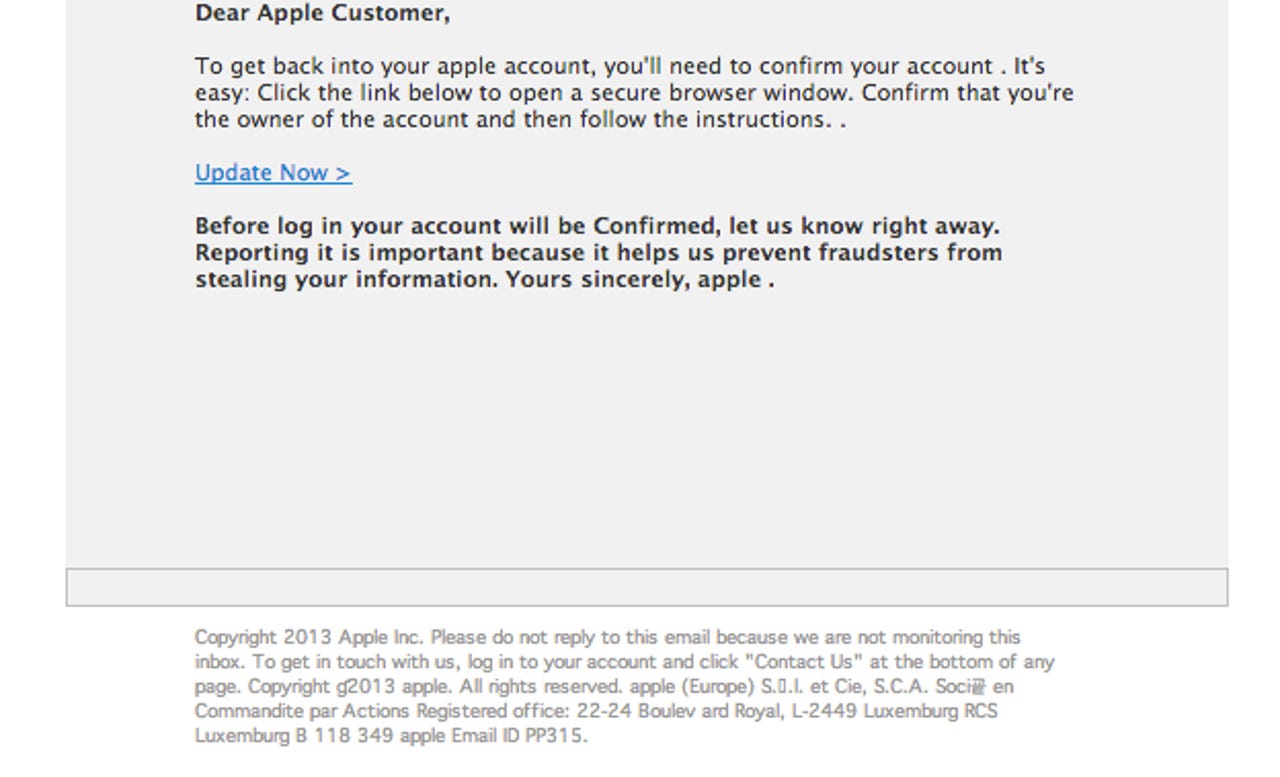
As well-done as the email is, the grammar mistake in the title is a dead giveaway -- not to mention the missing capital letter in 'Apple' -- and the site that it points to is not a legitimate Apple domain.
Users have taken to Twitter to warn others of the phishing attacks, and security firm Kasperky Lab has found that Apple-related phishing scams have skyrocketed in the last six months, with scammers focused on stealing login credentials and financial data.
The lesson here? Scammers often use emotional response or threats to remove a service in a specific time frame to induce panic in a user -- which in turn may make them less likely to double-check a domain before frantically inputting their login details.
Apple's recent breach is simply the latest example in such tactics.
The original reason that Apple's developer portal was taken offline may not have been malicious, but it has opened the floodgates for others with just these intentions.
This month, Apple's Dev Center went down for "maintenance for an extended period," leading users to wonder whether the iPad and iPhone maker's website had suffered a security breach. Apple later admitted that "an intruder attempted to secure personal information of our registered developers from [the] developer website."
Ibrahim Balic, a London-based researcher, then took to Twitter to claim responsibility for the issues, stating that his intentions were not malicious, and the the tech giant had been informed of a total of 13 flaws. To prove his claims, Balic posted a YouTube video explaining the process, which was later removed. However, you can still view an embedded version here.
The home page is now accessible, but the members-only area remains shut. Apple is currently working to make sure every security vulnerability is removed and you can check the current status here.