Apple plugs gaping iTunes hole, doesn't tell everyone

Apple today shipped an iTunes software refresh to add support for all its shiny new toys but, unless you're following security announcements closely, you'd never know that iTunes 7.4 contains a fix for a pretty nasty code execution vulnerability.
Here's what Mac users see:
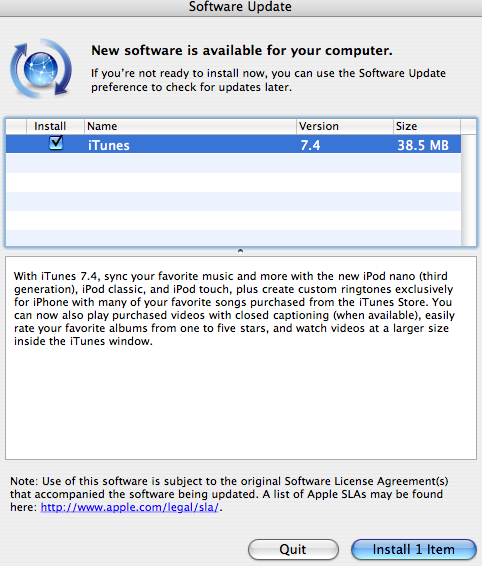
No mention whatsoever of CVE-2007-3752, a buffer overflow vulnerability that puts both Mac and Windows users at risk of arbitrary code execution attacks.
Our own Apple bloggers completely missed the security component of this iTunes update.
To be fair, the company did issue a brief advisory with basic details of this patch but, unless you pay close attention to these things, you just might skip this update because there's no prominent security warning from Apple.
Here's Apple's own explanation of the impact of this flaw, which was reported by David Thiel of iSEC Partners:
A buffer overflow exists in iTunes when processing album cover art. By enticing a user to open a maliciously crafted music file, an attacker may trigger the overflow which may lead to an unexpected application termination or arbitrary code execution. This update addresses the issue by performing proper bounds checking.
Even if you don't have the new iPods and won't be needing support, this is an iTunes update you absolutely should apply. The patch is being delivered via the Mac's automatic software update utility.
Manual download locations: iTunes 7.4 for Mac and iTunes 7.4 for Windows.