Australia 'may do dumb things' with crypto in 2016: EFF

Australia will probably do something dumb with cryptography in 2016, according to Nate Cardozo, staff attorney with the Electronic Frontiers Foundation (EFF). I think he's right, and there are several possibilities to choose from.
Cardozo was speaking about the state of the law relating to cryptography at the Real World Cryptography Conference at Stanford University on Thursday.
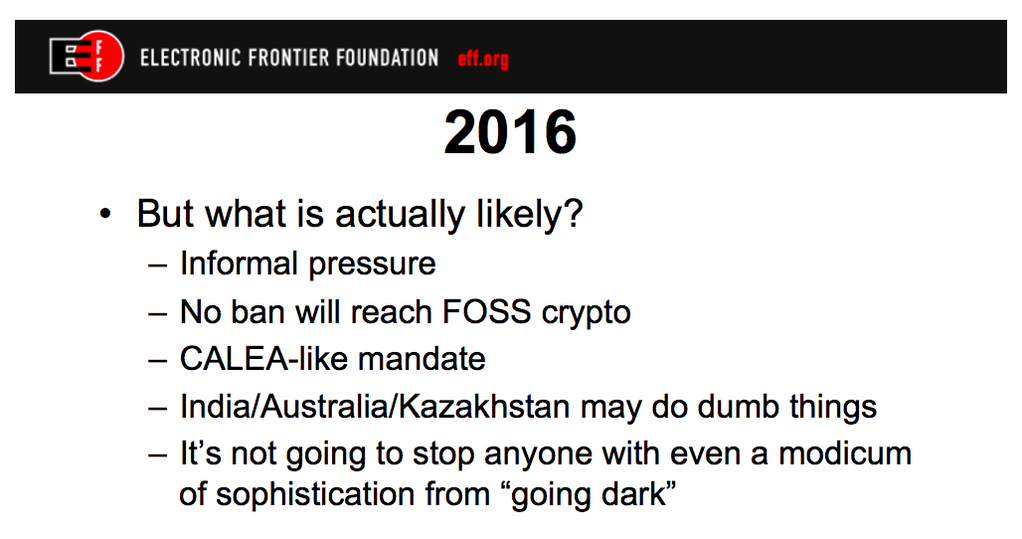
He noted that in the US, President Obama "will not -- for now -- call for legislation requiring companies to decode messages for law enforcement", and mandated key escrow is unlikely to happen. No laws are likely to come after crypto tools in free and open source software (FOSS), he said.
Cardozo thinks it's more likely that the government will put informal pressure on vendors and service providers to make unencrypted communications available somehow. Or perhaps they'll mandate it with something like the Communications Assistance for Law Enforcement Act (CALEA), which requires telecommunications equipment vendors to provide a mechanism for lawful interception.
But "India/Australia/Kazakhstan may do dumb things," read one of Cardozo's slides [PDF].
"And for the record, India/Kazakhstan/Australia were just examples of countries that are being dumb," Cardozo tweeted to ZDNet. Yes, there's plenty of dumb in the world.
Sticking to Australia, what could go wrong?
Well, I doubt Australia will mimic the UK's rhetoric that essentially calls for a ban on encryption. Turnbull knows how banks work, and knows they need encryption. Anyway, banning crypto would turn Turnbull into a Wickr criminal.
Turnbull's more flexible approach to communications technology, such as using a commercial email vendor for routine communications, demonstrated a modern risk-based approach to information security that was praised by a senior officer of the Australian Signals Directorate.
Turnbull has even taken a hands-on approach to the government's Cyber Security Review, as noted in the Department of Prime Minister and Cabinet's Cyber Blog.
"The Prime Minister recently met with the Department to discuss the Review. He has taken a keen interest in the Review, including providing feedback which has been incorporated," the department wrote.
"The Prime Minister has not asked for a substantial re-write of the Review," they added, rebutting media reports which said he had.
It's certainly possible that Turnbull will get the strategy wrong, but it's unlikely to be international-grade dumb.
No, the dumb will come in the implementation.
One obvious example is Australia's Defence Trade Control Act (DTCA), which controls so-called "dual-use" technology -- that is, technology with both military and civilian uses. That includes computers, electronics, telecommunications, and information security. In its attempts to control the spread of information about dual-use technology, DTCA has the potential to jail academics and stifle research.
"All it takes is for such an ambiguously-written regulation to be re-interpreted or over-enforced, and a country with an apparently positive approach to strong encryption could quickly morph into a state that silences or even prosecutes its own security researchers. While such regulations exist on the statute books, statements by politicians declaring their intent to prevent the privacy of encryption contribute to this climate of uncertainty, without any need for a new law," the EFF wrote last July.
"In this case, the planned introduction of criminal provisions to the Defence Trade Controls Act has raised serious questions about the safety of distributing or even teaching encryption among researchers."
Such regulations are drafted by the Attorney-General's Department (AGD). Their track record is not stellar. Remember the laughable one-page definition of metadata that made no sense technically? Remember their minister, Australia's favourite attorney-general, Senator George Brandis QC, stumbling through an excruciating TV interview, completely unable to explain the concept? Happy days.
Less well-known was an episode in 2011, under the previous government, of the Cybercrime Legislation Amendment Bill 2011. This was intended to bring Australian law in line with the Council of Europe Convention on Cybercrime. Except the legislation was prepared in such a rush that key sections didn't meet those needs at all.
With this constant haste, with AGD less technically clueful than it imagines, with an Attorney-General's office that's far from nimble, and with an Attorney-General whose personal understanding of how the world works is at best antiquated -- well, does this strike you as a team ready to tackle the subtleties of legitimate and illegitimate uses of encryption algorithms, vulnerability scanners, and zero-day exploits?
I live in fear that one morning after a late-night Senate debate, Australia will discover that it's outlawed multiplication.
Now that would be some humiliating, international-grade dumb.
DTCA isn't the only potential trap for hasty legislators. Mandatory telco data retention is now law, but the system has to be implemented, and then operated.
And coming soon are the Telecommunications Sector Security Reforms (TSSR). This legislation aims to "establish a security framework for the telecommunications sector", with the intention of protecting this critical infrastructure. But it proposes to give the Attorney-General the power to order a telco "to do or refrain from doing a specified thing to manage security risks", and there's some potential for disaster.
There's plenty of scope in all that for Australia to do something dumb with cryptography in 2016. With the team as it is, it's almost inevitable.