Authorities plan to mass-uninstall Emotet from infected hosts on April 25, 2021

Updated on January 28 to correct date from March 25 to April 25. The error in interpreting the date was discovered by Malwarebytes earlier today. Original article, with the corrected date is below.
Law enforcement officials in the Netherlands are in the process of delivering an Emotet update that will remove the malware from all infected computers on April 25, 2021, ZDNet has learned today.
ZDNET Recommends
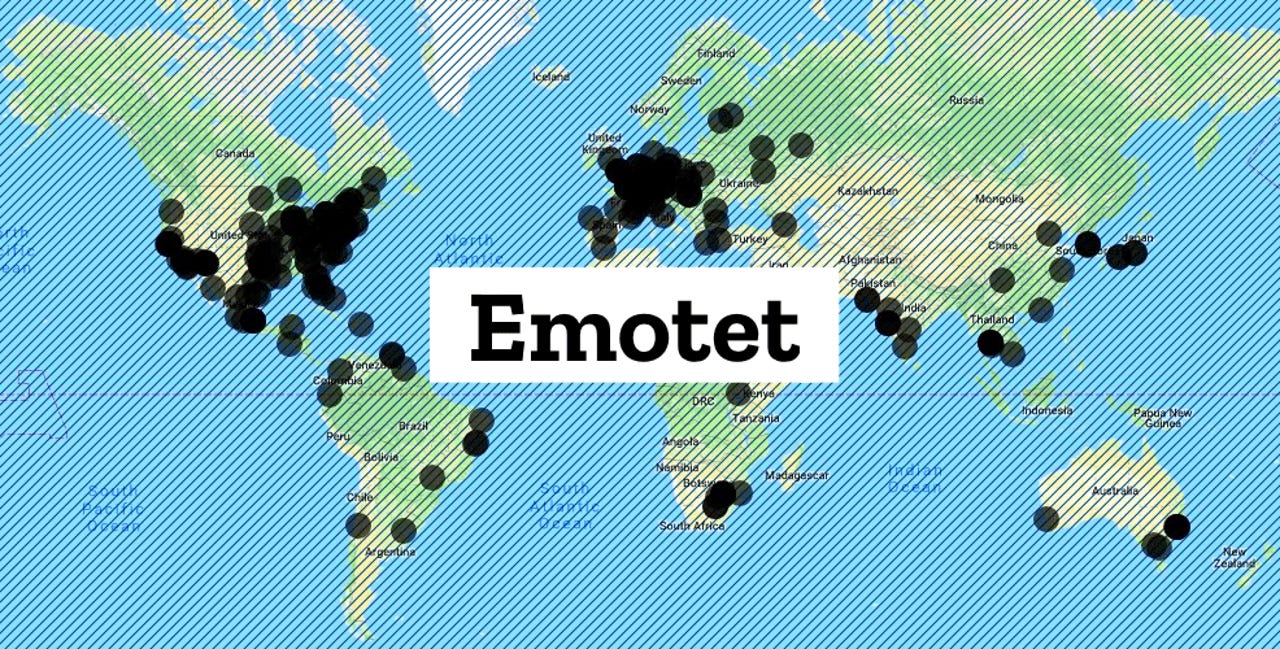
The update was made possible after law enforcement agencies from across eight countries orchestrated a coordinated takedown this week to seize servers and arrest individuals behind Emotet, considered today's largest malware botnet.
While servers were located across multiple countries, Dutch officials said that two of three of Emotet's primary command and control (C&C) servers were located inside its borders.
Dutch police officials said today they used their access to these two crucial servers to deploy a boobytrapped Emotet update to all infected hosts.
According to public reports, also confirmed by ZDNet with two cyber-security firms that have historically tracked Emotet operations, this update contains a time-bomb-like code that will uninstall the Emotet malware on April 25, 2021, at 12:00, the local time of each computer.
All Emotet epochs now are delivering the payload (https://t.co/Tv21VmJm4s) which has the code to remove Emotet on 25 March 2021 12:00. I believe that #Emotet #Killed pic.twitter.com/FnrdqZmQcd
— milkream (@milkr3am) January 27, 2021
Last chance to audit networks
"The technical disruption that the Dutch police detailed in their press release, if it works as they described, will effectively reset Emotet," Binary Defense senior director Randy Pargman told ZDNet today in an online chat.
"It forces the threat actors behind it to start over and attempt to rebuild from scratch, and it gives IT staff at companies around the world a chance to locate and remediate their computers that have been infected," Pargman added.
Currently, the Europol takedown prevents the Emotet gang from selling access to Emotet-infected computers to other malware gangs, a tactic the Emotet gang has been known for doing.
But Emotet hosts where cybercrime gangs have already bought access remain at risk.
Pargman is now urging companies to take advantage of this time window until April 25 to investigate internal networks for the presence of the Emotet malware and see if other gangs used it to deploy other threats.
After Emotet uninstalls itself on April 25, such investigations will be harder to carry out.
Arrests in Ukraine
Since ZDNet's early coverage of the Emotet takedown, Ukrainian police officials have also come out to announce they arrested two individuals who they believe were tasked with keeping Emotet's servers up and running.
A video of the arrests and apartment searches is available below.