Azure AD Cloud App Discovery, First Take: Shining a light on shadow IT

It's always amusing to be told that the cloud isn't ready for business by companies who don't realize that their staff haven't got the memo. One survey quoted CTOs of several large organizations as saying they wouldn't use software as a service (SaaS); yet some of those same businesses were already case studies for SaaS offerings the CTOs were rejecting. When signing up for SaaS only takes a company credit card and services like Box and Yammer tempt users in with free services, you can expect that cloud services are everywhere in your business unless you're actively blocking them (which is harder than you think).
If you're realistic, you know that cloud and SaaS tools are in use in your business, but you probably don't know which ones. So it would be useful to discover what's being used. And while there may be a few cloud services you want to move users away from (if you're paying for Box or OneDrive for Business, for example, you'll want work documents there rather than in DropBox or Google Drive), if those cloud apps help people get the job done then you'll want to manage them.
Azure Active Directory, Microsoft's directory services in the cloud, includes a range of management tools such as single sign-on and multi-factor authentication. If you have an official Twitter account that several employees post through, you want to protect the account password from hackers — and from employees who leave and might want to embarrass you. You can use Azure AD to let users sign into cloud services using their standard user name and password, so they don't have another set of credentials to remember, forget, change, get phished for or take with them when they leave. You can also use the Azure AD multi-factor authentication service to add an extra level of protection, so users have to put in a code from a text or email message, or just answer the phone to log in.
Cloud App Discovery
There's a list of over 1,200 cloud apps and online services you can manage with Azure AD — everything from AirBnB and AWS to Zen Payroll and Zoho Docs. You're not going to set up all of them on the off chance someone is using them, so the new preview Cloud App Discovery module is ideal. You can use it to see who's using what, and you can add the useful ones to your Azure management system straight away. Even if you don't use Azure AD for other things, this is a useful tool for scanning what's being used around your company. While it's in preview, this is a separate service, but it will move into the Azure Management Portal by the time it's generally available. It's not clear if it will be available as part of Azure Active Directory Free (which lets you give users single sign-on for up to ten cloud apps each) or if you'll need Azure Active Directory Premium. The premium version gives you multi-factor authentication for single sign-on app access, and includes extra features like group management tools that let you only give users in the Finance AD group access to finance cloud apps and HR users access to HR cloud services.
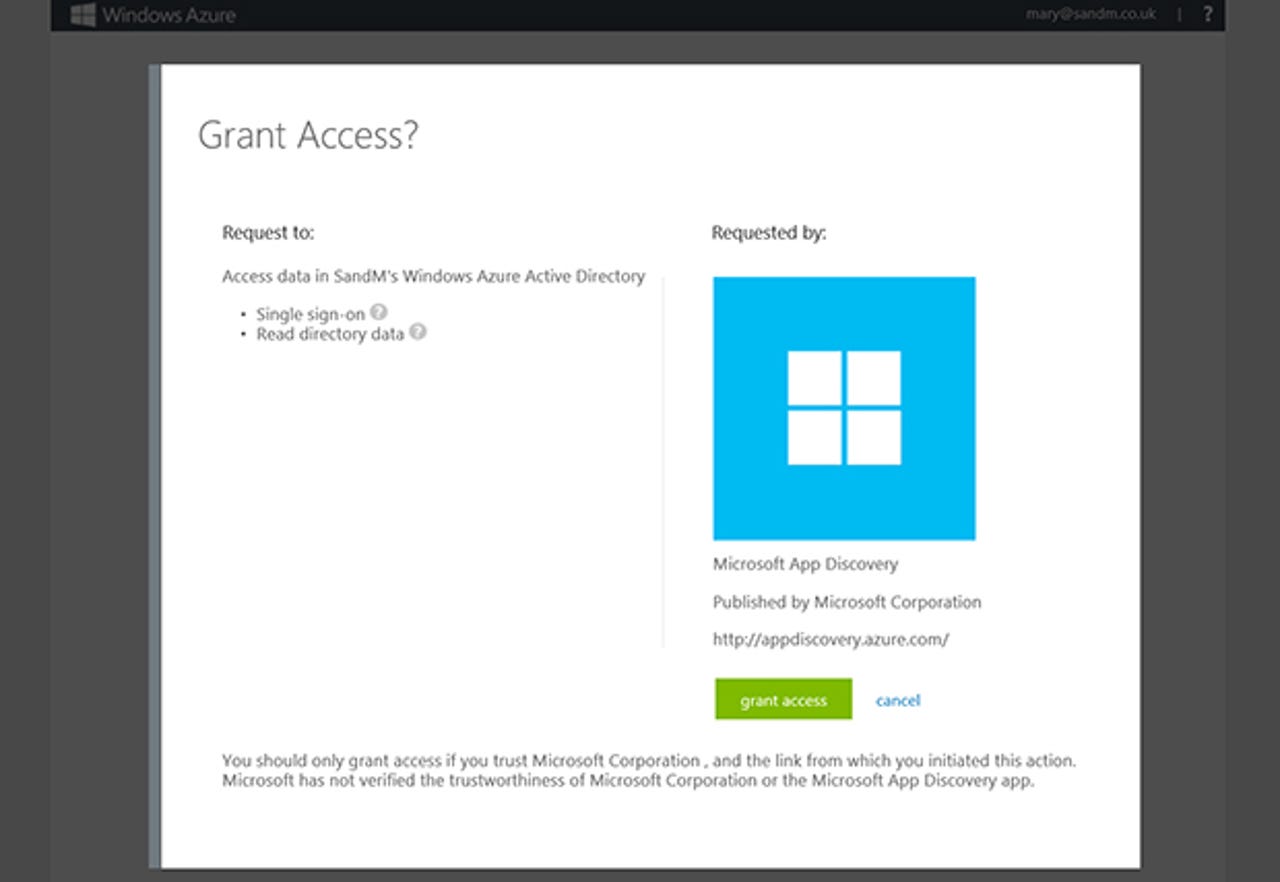
While it's in preview, setting up Cloud App Discovery is easy — simply sign into the portal with any Microsoft organizational account (if you don't already have one from Office 365 or Azure you can get one with an Azure trial). You need to be an administrator because you need to be able to consent to Azure connecting to your Active Directory; the alternative email address for your admin account will also get an email notification of the access, for security.
Next you need to download the discovery agent and deploy it onto the Windows PCs (Windows 7 and above) that you want to monitor where it runs as a service. We're expecting Microsoft to include the discovery functionality in existing agents like the ones for System Center and Intune, but for now it's separate (and it comes in a ZIP as an EXE and a certificate); you can deploy it with whatever deployment tools you usually use to push software out to the PCs in your business.
When you go back to the portal you'll start to see details of the apps the service has discovered. We saw the initial list of apps after only a couple of minutes, but it continued to grow and after a few hours the service had found a total of 328 'apps' from our two test users.
The definition of app is very broad here; it includes YouTube and AOL and other things you might usually think of as websites for content (like Reddit and Buzzfeed) as well as more traditional cloud apps. That's because the service isn't looking for cloud clients that are installed — there are plenty of desktop management tools that will do that, and it doesn't help you track usage of a service like Salesforce where users can do everything on the website — but for cloud traffic. That means it also picks up tools that websites use for integrating social media or web analytics, which can be a bit confusing at first.
You may want to see everything at least once, in order to get a view of what's going on that's far more friendly than the average firewall traffic report. If not, you can filter the dashboard to see just business cloud apps.
The filters in the dashboard are where things get interesting; you can look across all the apps in use and see which are used by the most people, or which generate the most web requests, and how much data they transfer. Click the 'apps discovered' pane for specific details that you can filter in different ways.
Azure categorizes the apps it finds, and you can drill into a category and see details just for those apps, or click through to a single app and see how many people are using it and how often, as well as how much data it's uploading and downloading. What you don't get to see is who is using which services, but it's fascinating to see just how many cloud services are in use, how often they're accessed and how much data they're transferring back and forth. You can also sort the app list by 'recently discovered' to keep an eye on what new apps are showing up.
When you get down to a single app, you can click to start managing it in Azure AD; if you have Azure AD set up already that takes you to a portal where you fill in account details and manage users. For apps Azure doesn't know about, there's a link to the feedback site where you can log a request for Microsoft to add them to its list.
There's no way to indicate that you don't need to be tracking specific websites, or at least of hiding them in the list on the portal, which would be useful. You might want to see if a lot of content is being uploaded to Reddit, for example, but seeing how many web requests have been made to The Telegraph's site is moving from monitoring cloud usage to questions about employee productivity.
As this is a preview we expect Microsoft to add more features and refine the experience before the Cloud App Discovery service becomes generally available. Even as a preview, it's a useful service — if a little too broad in what it counts as a cloud app.