BlackBerry releases new security tool for reverse-engineering PE files

Today, at the Black Hat USA 2020 security conference, BlackBerry released a new tool for the cyber-security community.
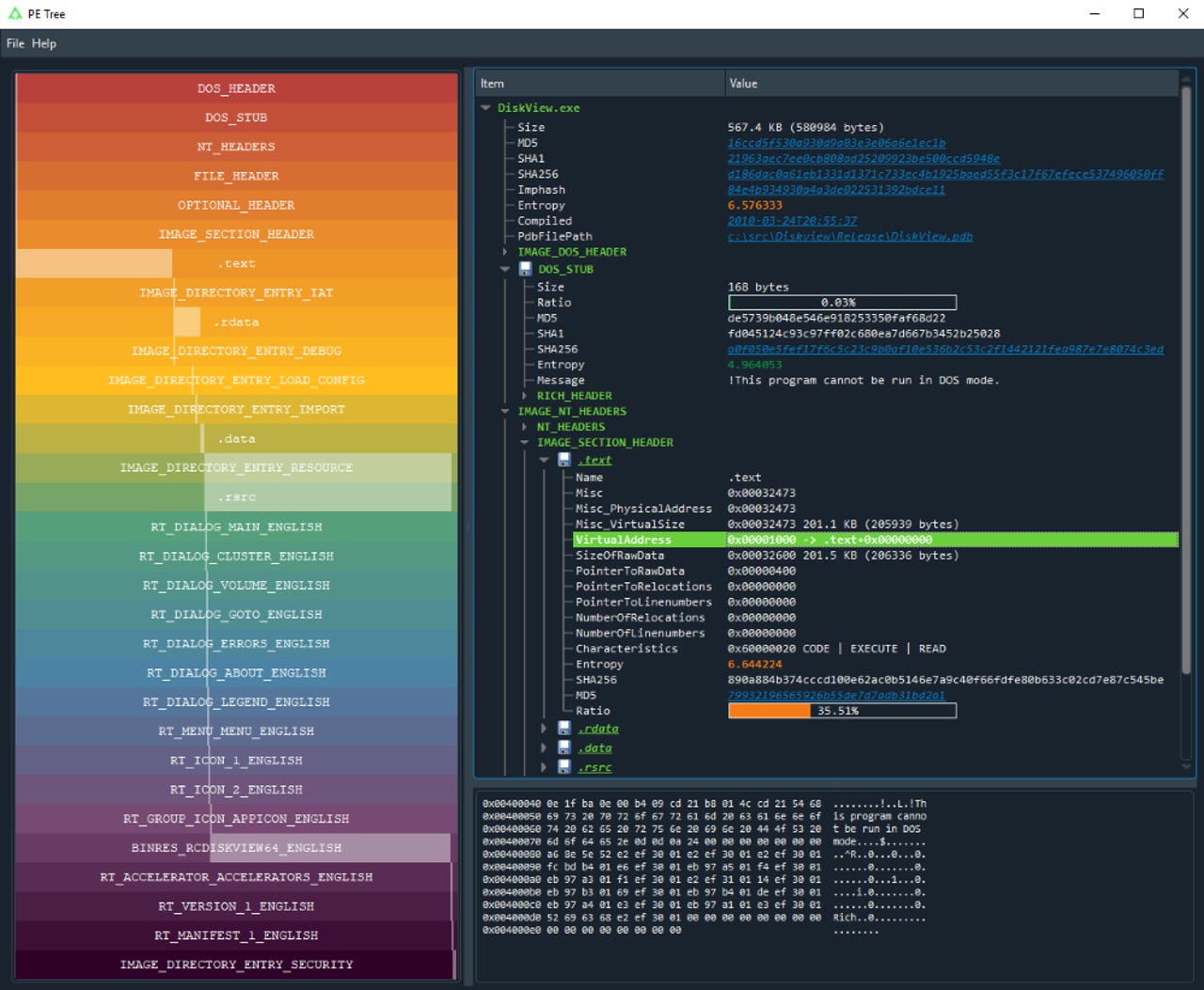
Named PE Tree, this is a new Python-based app for Linux, Mac, and Windows that can be used to reverse-engineer and analyze the internal structure of Portable Executable (PE) files -- a common file that malware authors have used to hide malicious payloads.
The tool has been open-sourced on GitHub since last week, but today marks its official release.
"Reverse engineering of malware is an extremely time- and labor-intensive process, which can involve hours of disassembling and sometimes deconstructing a software program," the company said in a press release today.
"The BlackBerry Research and Intelligence team initially developed this open source tool for internal use and is now making it available to the malware reverse engineering community," it added.
According to BlackBerry, PE Tree's benefits include:
- Listing PE file content in an easy-to-navigate tree view
- Integration with the IDA Pro decompiler (easy navigation of PE structures, dumping in-memory PE files, performing import reconstruction)
- VirusTotal search integration
- Can send data to CyberChef
- Can run as either a standalone application or an IDAPython plugin
- Open source license allows community contributions
The tool is an alternative to PE-bear, a similar app developed by Malwarebytes malware analyst Aleksandra "Hasherezade" Doniec.
Cyber-security vendors embracing the open-source space
PE Tree also marks the release of yet another useful cyber-security tool into the open source space. This is a major change in approach for cyber-security firms, which have historically kept their internal tools out of the public eye, or closed-source and under expensive commercial licenses.
Over the past two years, we've seen:
- FireEye release CommandoVM, a Windows-based virtual machine specifically built for malware research, as an alternative to Kali Linux, the community's favorite OS.
- FireEye release Flashmingo, an app to automatically search for Flash vulnerabilities.
- FireEye release Crescendo, a real-time event viewer for macOS.
- FireEye release StringSifter, a machine learning tool that automatically ranks strings based on their relevance for malware analysis.
- FireEye release SharPersist, a red-team utility for establishing persistence on Windows using different techniques.
- FireEye release Capa, a tool that can analyze malware and detect malicious capabilities.
- FireEye release SilkETW, a tool for collecting and searching Event Tracing for Windows (ETW) logs.
- CERT-Poland release DRAKVUF, an automated hypervisor-level malware analysis system/sandbox.
- CyberArk release SkyWrapper, a tool that can scan AWS infrastructure and detect if hackers have abused self-replicating tokens to maintain access to compromised systems.
- CyberArk release SkyArk, a tool to detect shadow admin accounts in AWS and Azure environments.
- F-Secure release TamaGo, a Go-based firmware for bare metal ARM System-on-Chip (SoC) components.
- F-Secure release Jandroid, a tool to identify potential logic bug exploit chains on Android.
- F-Secure release C3, an open source tool for building custom command-and-control servers.
- SEC Consult release SEC Xtractor, a tool for hardware exploitation and firmware extraction.
- NCC Group release Sniffle, the world's first open source sniffer for Bluetooth 5.
- NCC Group release Phantom Tap (PhanTap), a tool for silently intercepting network traffic.
- NCC Group releases WStalker, a proxy to support the testing of web API calls.
- Google release Tsunami, a vulnerability scanner for large-scale enterprise networks.
- Google release UKIP, a tool to prevent USB keystroke injection attacks on Linux.
- Google release the Sandboxed API, a project for sandboxing C/C++ libraries on Linux.
- Cloudflare release Flan Scan, a network vulnerability scanner.
- Red Canary release Chain Reactor, a tool for adversary simulations on Linux systems.
- SpecterOps release Satellite, a payload and proxy service for red team operations.
- Trustwave release SCShell, a tool for fileless lateral movement that relies on Service Manager.
- Trustwave release CrackQ, a tool for managing hashcat password-cracking jobs in a queuing system.
- France's ANSSI cyber-security agency release DFIR ORC, an open-source forensics tool dedicated to artifact collection from Windows systems.
- Sophos release Sandboxie, a user-friendly app to let users sandbox (isolate) dangerous apps inside their own limited container.
- NSA release Ghidra, a complete software reverse-engineering toolkit.
- Intel release HBFA, an app to help with firmware security testing.
- Kroll release KAPE, an artifact parser for incident response teams, to search for possible clues of compromise.